March 2023 Threat Trend Report on Kimsuky Group

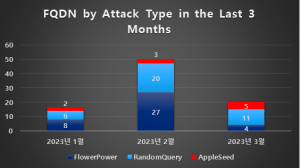
The Kimsuky group’s activities in March 2023 showed a decline in comparison to their activities in February.
Unlike the past where most major issues were found in the FlowerPower type, this month was focused on the RandomQuery type, which showed the highest amount of activity.
The FlowerPower type began to use “Korean domains”, and it has been confirmed that the RandomQuery type has been using various initial distribution methods and using new ways to distribute xRAT.
Finally, it has been confirmed that the RandomQuery type’s system has been changing, just like the FlowerPower type.
Attack Statistics
FlowerPower
(1) Using a Korean Domain (Punycode)
RandomQuery
(1) Distribution via LNK Files
(2) Distribution via OneNote Files
(3) Distribution of xRAT via Google Drive
(4) Distribution of xRAT via RandomQuery variant
(5) Changes to the RandomQuery System