AveMaria malware being distributed as spam mail

AveMaria is a RAT (Remote Administration Tool) malware with a remote control feature that receives commands from the C&C server and performs a variety of malicious behaviors. As shown in the weekly statistics below, it is not included in the Top 5, but it has consistently been taking up a certain percentage of the total.
AveMaria malware has been distributed via spam mails similar to AgentTesla, Lokibot, and Formbook malware. Additionally, it is packeted and distributed in a form of .NET to bypass detection.
The spam mail used in distribution of AveMaria has 2 zip files: .7z file and .zip file.
- RFQ-PO-005668657-08-4-20-Order_Sample,xlxs.7z
- RFQ-PO-005668657-08-4-20-Order_Sample,xlxs.zip
These archive files all contain the same exe file: AveMaria malware.
- RFQ-PO-005668657-08-4-20-Order_Sample,xlxs.exe
When the user extracts the archive file and mistakenly runs the file thinking that it’s an .xlsx file, AveMaria malware is run. The followings are the features that this malware can execute by receiving commands from the attacker:
First, the attacker can assign an option when creating AveMaria, and various features can be activated based on the set options.
[Various features based on options]
a. Assign the name installed
Copy and relaunch with the assigned name, and the file path is %AppData%\Roaming.
b. Persistence mechanism
Add registry Run Key with the assigned name and make it run after reboot.
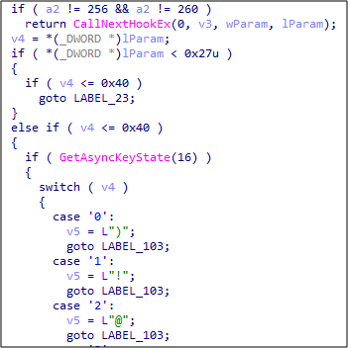
c. Offline keylogging
Start keylogging upon execution and save data in %AppData%\Local\Microsoft\Microsoft Vision folder. keylogging uses a method to global message hook with SetWindowsHookExA() function.
d. Watchdog
Feature that re-runs AveMaria malware when it is terminated. Create cmd.exe as a child process and inject shellcode. The shellcode’s feature is to circulate iteration, check whether AveMaria is run, and re-run it if the malware is terminated.

e. Permission escalation
When malware is run for the first time but has no admin permission, UAC Bypass technique is used to escalate the malware’s permission to the administrator level. See below for further details.
f. Windows Defender exclusion
Use the powershell command below to add Windows Defender exclusion file path, and render the items undetectable by Windows Defender.
- powershell Add-MpPreference -ExclusionPath C:\
[Feature performed by attacker commands]
Because AveMaria is a RAT malware, it supports various features that are run based on the attacker’s command.

a. File tasks
Perform features such as lookup/upload/download for files in the infected PC.
b. Process-related tasks
Perform features such as lookup/terminate for processes that are currently running in the infected PC.
c. Update
Update its module.
d. Download & run
Receive an URL from the attacker, download additional malware externally, and run it.
e. Remote shell
Receive a command from the attacker, run the command using cmd.exe, and send output result to the C&C server.
f. Online keylogging
Send keylogging info to the attacker in real-time.
g. WebCam
Activate webcam of the infected PC and send a video to the attacker in real-time.
h. Reverse Proxy
Use the infected PC as a proxy server. This means that when this feature is enabled, external connection and malicious behavior from the C&C server is carried out through the infected PC. And externally, this behavior is acknowledged as the behavior of the infected PC instead of the original attacker as the IP of the infected PC is shown instead of the IP of the actual attacker.
Also note that the malware sends a string named “AVE_MARIA” for authentication when performing a proxy connection with the C&C server. AveMaria’s original name is WARZONE RAT, but it is often called AveMaria due to this string.

i. Remote VNC Control
Download vncdll.dll from the C&C server and load it in the memory. This DLL is a DLL that performs a VNC server feature.

This means that the module that acts as the VNC server runs within the AveMaria process. Afterward, the attacker can use a VNC client program such as TightVNC and others like TigerVNC to connect to the infected PC and perform remote control.
j. Reverse RDP
Drop RdpWrapper DLL to the infected PC and add as a service. The file path of the dropped RdpWrapper DLL is as follows, and this is added as a service with the name TermService.
- %Program Files%microsft DN1\sqlmap.dll
Create a random string and add to user account as ID/PW afterward. Then, add the added user account to the following registry key so that the user cannot recognize that an account has been added.
- HKOM\Software\Microsoft\Windows NT\CurrentVersion\winlogon\SpecialAccounts\UserList
Lastly, the added ID/PW is added to the registry key shown below and saved.
- ID : HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\[random] / rudp
- Password : HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\[random] / rpdp
Afterward, the attacker can use the created ID/PW to RDP connect to the infected PC and perform remote control.
k. Permission escalation
This is a feature to escalate permission using UAC bypass. Normally, when running via double-clicking, the file is run with normal permission, but features such as adding services mentioned above require high (admin) permission. Therefore, this is a necessary feature for the attacker.
AveMaria has 2 UAC bypass techniques, and one of them is abusing DLL Hijacking vulnerability of Dism.exe. This feature uses malware saved with the name WM_DSP in the resource section.
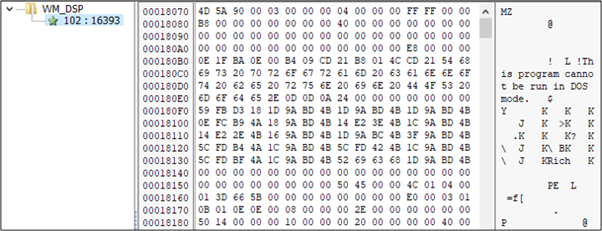
This malware uses IFilerOperation to inject the shellcode that saves the malicious DLL to the system32 directory into explorer.exe. Through this, the malicious DLL can be copied to the system32 directory without permission. Note that this DLL is also saved with the name WM_DISP in the resource section of PE. Afterward, it creates oemsetup.xml required to perform malicious behavior and uses it as a parameter to run Auto Elevate program, pkmgr.exe. As a result, Dism.exe that contains DLL Hijacking vulnerability is run as a child process, and loads DismCore.dll which is a malicious DLL copied to the system32 directory. This DismCore.dll has a feature of running AveMaria, and because it runs as a child process of the Auto Elevate program, it is run with administrator permission which enables permission escalation.
If the environment of the infected PC is Windows 10, a different UAC Bypass technique is used. When designating the malware directory to the following registry and running an Auto Elevate program sdclt.exe, it refers to the key and runs AveMaria through control.exe. This method is abusing the fact the key is HKCU registry key that Auto Elevate program can modify without admin permission.
- HKCU\Software\Classes\Folder\Shell\Open\command
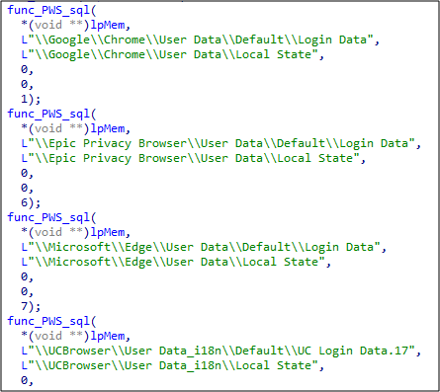
l. Stealing account info
Older version of AveMaria targeted web browsers such as Chrome, Firefox, IE, and Edge, along with email client programs such as Outlook, Thunderbird, and Foxmail for information theft.
For Chrome, similar to vncdll, it downloads sqlite3.dll in the memory, takes the address of functions that the DLL exports, uses features of these functions (same as sqlite3.dll), and extract account info.

In case of older IE and Edge, the malware loads vaultcli.dll and extracts account info using exporting functions from the DLL. For Firefox and Thunderbird, the malware loads nss3.dll, msvcr120.dll, msvcp120.dll, mozglue.dll, softokn3.dll, and vcruntime140.dll which exist in the installation folder and uses the required functions to extract account info. If the functions don’t exist, then the malware can download them externally.
The newest version of AveMaria added other web browsers as its info-stealer targets such as Opera, Chromium, and QQ Browser.
When there’s a suspicious email in the inbox, users must refrain from opening the attachment files within the email. Also, V3 should be updated to the latest version so that malware infection can be prevented.
AhnLab’s anti-malware software V3 detects the malware using the following aliases:
[File Detection]
- Trojan/Win32.Kryptik.R346819
[Behavior Detection]
- Malware/MDP.Inject.M218
- Malware/MDP.Behavior.M3346
[Relevant IOC Info]
C2
– 54369253290033.sytes[.]net:5200
HASH
– 77384b5848a963645b44fedc97075bc2




