ASEC Weekly Malware Statistics (October 17th, 2022 – October 23rd, 2022)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known malware. This post will list weekly statistics collected from October 17th, 2022 (Monday) to October 23rd (Sunday).
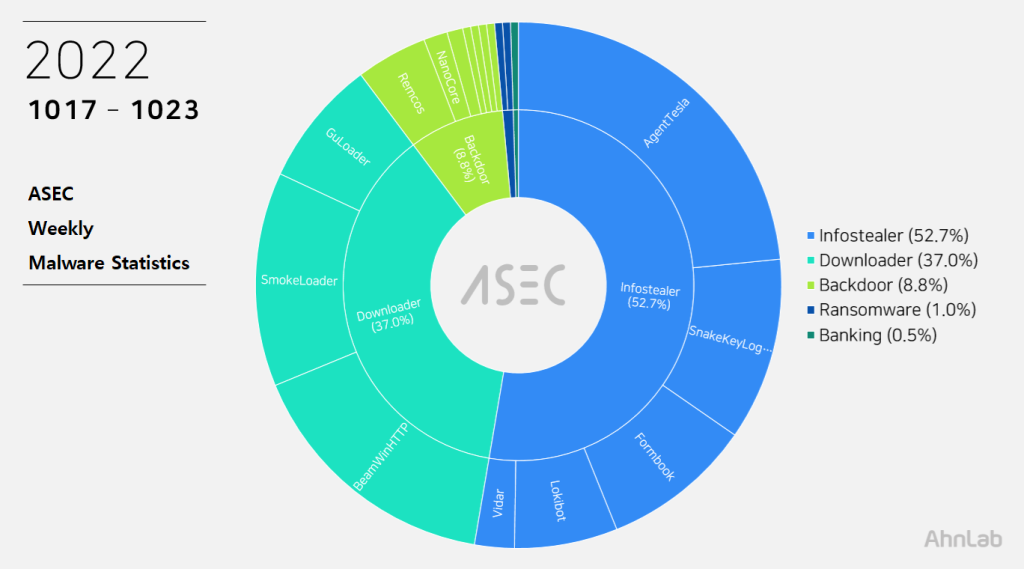
For the main category, info-stealer ranked top with 52.7%, followed by downloader with 37.0%, backdoor with 8.8%, ransomware with 1.0%, and banking malware with 0.5%.
Top 1 – Agent Tesla
AgentTesla is an infostealer that ranked first place with 23.4%. It is an info-stealer that leaks user credentials saved in web browsers, emails, and FTP clients.
It uses e-mail (SMTP) to leak collected information, and there are samples that used FTP or Discord API. C&C information of recently collected samples is as follows.
- server : mail.timeoptic[.]com (43.241.56[.]16)
sender : sales@timeoptic[.]com
receiver : goldtrusttship66@gmail[.]com
user : sales@timeoptic[.]com
pw : 5***0 - server mail.fttmas[.]com (167.250.5[.]29)
sender : sales2@fttmas[.]com
receiver : mpdolx@yandex[.]com
user : sales2@fttmas[.]com
pw : 0****^(? - server : mail.scahe.co[.]in (219.90.65[.]155)
sender : sj@scahe.co[.]in
receiver : cloud.page@yandex[.]com
user : sj@scahe.co[.]in
pw : sc****45
As most are distributed through spam emails disguised as invoices, shipment documents, and purchase orders, the file names contain such words shown above (Invoice, Shipment, and P.O. – Purchase Order). Multiple collected samples were disguised as files with extensions of pdf and xlsx.
- PO_6039792_Order_Confirmation.exe
- Remittance_advice.exe
- Debit_note.exe
- FB-108N FB-108NK 詢價 – 田勤.exe
- BBMT2022Q753_AA_CARPENTRY_SCAN.exe
- Bank_slip.exe
- PO#ATN-19055-1.exe
- BALANCE_PAYMENT.exe
- Quote_2200001842.exe
Top 2 – BeamWinHTTP
BeamWinHTTP is a downloader malware that ranked second with 16.1%. BeamWinHTTP is distributed via malware disguised as PUP installer. When it is executed, it installs PUP malware Garbage Cleaner, and can download and install additional malware at the same time.
The confirmed C&C server URL is as follows.
- 45.15.156[.]54/itsnotmalware/count.php
- 45.139.105[.]171/itsnotmalware/count.php
Top 3 – Smokeloader
Smokeloader is infostealer / downloader malware that is distributed via exploit kits. This week, it ranked third place with 13.2%. Like other malware that is distributed via exploit kits, this malware also has MalPe form.
When executed, it injects itself to explorer.exe, and the actual malicious behavior is executed by explorer.exe. After connecting to C&C server, it can either download additional module, or download another malware. Additionally downloaded malware usually has a feature of infostealer, and explorer.exe (child process) is created and injects module to operate.
Smoke Loader is an info-stealer / downloader malware that ranked fifth place with 6.6%. For an analysis report related to Smoke Loader, refer to the ASEC Report below.
[PDF] ASEC REPORT vol.101_Smoke Loader Learns New Tricks
The confirmed C&C server URLs are as follows.
- hiragaih[.]com
- kyotoltdssl[.]com
- kuitobowls[.]com
- sakuratoma[.]com
- yukyurice[.]com
- kyotobowls[.]com
- fujysoey[.]com
- gesshtbow[.]com
- hasekushi[.]com
Another malware can be downloaded from outside by using C&C server, and currently confirmed malware strains are Dharma and Lockbit ransomware.
Top 4 – SnakeKeylogger
Taking the fourth place with 9.1%, SnakeKeylogger is an info-stealer type malware that leaks information such as user key inputs, system clipboards, and browser account information.
Like AgentTesla, this malware uses e-mail servers and user accounts when leaking collected information. The following is the accounts used by recently collected samples.
- host : us2.smtp.mailhostbox[.]com (208.91.199[.]225)
sender: sonia.socorro@centra1-logistica[.]com
receiver: sonia.socorro@centra1-logistica[.]com
user: sonia.socorro@centra1-logistica[.]com
pw: 29m***N^G - host : us2.smtp.mailhostbox[.]com (208.91.199[.]225)
sender: wbb@sumce-cn[.]com
receiver: wbb@sumce-cn[.]com
user: wbb@sumce-cn[.]com
pw: ipy***O$r9 - host : us2.smtp.mailhostbox[.]com (208.91.199[.]225)
sender : coordinacion1@oibvagenciaduana-ec[.]com
receiver : coordinacion1@oibvagenciaduana-ec[.]com
user : coordinacion1@oibvagenciaduana-ec[.]com
pw : TR***1
Top 5 – Formbook
Formbook ranked fifth place with 9.3%.
Like other info-stealer, it is mainly distributed through spam emails. The distributed file names are close to each other.
- SPRING SHINE – VSL PARTICULARS.exe
- Proof of payment.exe
- revised_invoice.exe
- MV OCEAN DRAGON(SHIP PARTICULARS).exe
- Request for Quotation.exe
- SOA FROM 2020 TO FEB 2021.pdf.exe
- DHL Notification_pdf.exe
- Rev NX028362 Contract Tender.exe
- DHL_PDF.exe
Formbook is injected into normal processes (one is a running explorer.exe and the other is in system32) and performs the malicious behaviors. Besides user credentials in the web browser, the malware can steal various information through keylogging, clipboard grabbing, and web browser form grabbing.
Below is the list of confirmed C&C server URLs of Formbook.
- hxxp://www.dwpato[.]xyz/s11n/
- hxxp://www.aseopli[.]online/g2e8/
- hxxp://www.myvea[.]online/c0e5/
- hxxp://www.flayos[.]xyz/g47e/
- hxxp://www.shutro[.]online/mr06/
- hxxp://www.asyimpo[.]xyz/g28p/
- hxxp://www.gastries[.]info/ndgi/
- hxxp://www.myvea[.]online/c0e5/
- hxxp://www.lastsummercog[.]com/ermr/
- hxxp://www.ziewip[.]xyz/sm28/
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.



