ASEC Weekly Malware Statistics (February 7th, 2022 – February 13th, 2022)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known malware. This post will list weekly statistics collected from February 7th, 2022 (Monday) to February 13th, 2022 (Sunday).
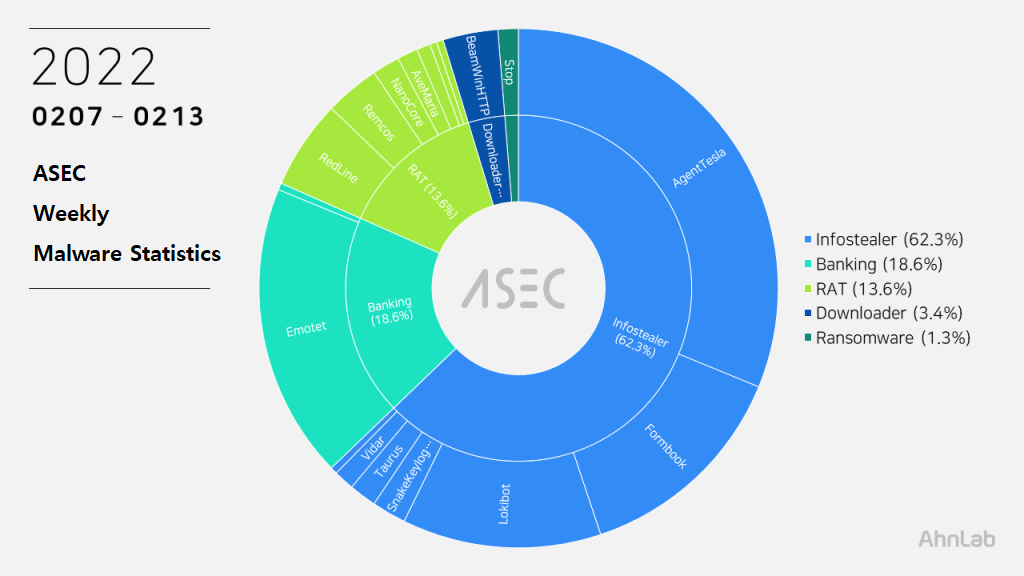
For the main category, info-stealer ranked top with 62.3%, followed by banking malware with 18.6%, RAT (Remote Administration Tool) with 13.6%, downloader with 3.4%, and ransomware with 1.3%.
Top 1 – AgentTesla
AgentTesla ranked first place with 30.9% once again. It is an info-stealer malware that leaks user credentials saved in web browsers, emails, and FTP clients.
Recently collected samples use the following email servers and user accounts when leaking the collected information.
- server : mail.imibic[.]org
sender : facturacion@imibic[.]org
receiver : facturacion@imibic[.]org
user : facturacion@imibic[.]org
pw : 537****48! - server : mail.tuquyfood[.]com
sender : tuquyfood@tuquyfood[.]com
receiver : marketdept@davitecco[.]com
user : tuquyfood@tuquyfood[.]com
pw : Tien****23 - server : mail.butterflymotors[.]com
sender : hr@butterflymotors[.]com
receiver : ellisjemie2b@gmail[.]com
user : hr@butterflymotors[.]com
pw : #ifO****n2j{
As most are distributed through spam emails disguised as invoices, shipment documents, and purchase orders, the file names contain such words shown above (Invoice, Shipment, P.O. – Purchase Order). Multiple collected samples were disguised as files with extensions of pdf and xlsx.
- DHLAWB130501923096PDF.exe
- DOC.exe
- DOCS.exe
- IHARA RFQ_20983764_pdf.exe
- INDIA HCU27GHED.exe
- invoices.exe
- New po docs..exe
- pay.exe
- Payment Slip.exe
- PO211022.exe
- QUOTATIONESV20220210.PDF.exe
- RFQ Quotation.exe
- RFQ1090212004.PDF.exe
- RFQNº00024625.PDF.exe
- SHIPMENT DOCUMENTS-INVOICE.exe
- shipping docs BL PL.exe
- SKT66800.EXE
- SPECIFIC.EXE
Top 2 – Emotet
Emotet was ranked second place with 18.2%. Emotet is a banking malware that is being continuously distributed via spam mails.
In its basic form, it is a downloader without additional features, but once installed on a system, it can download additional modules or additional malware.
Additional modules include user info-stealing modules that steal information such as web browser and e-mail credentials, and propagation module that spreads via shared folders. Additional malware strains include other banking malware such as Oakbot and Trickbot.
The following are the some of the confirmed C&C server domains for Emotet:
- 217.182.143[.]207:443
- 159.69.237[.]188:443
- 103.75.201[.]4:443
- 144.76.186[.]55:7080
- 51.254.140[.]238:7080
- 162.214.50[.]39:7080
- 174.136.15[.]27:8080
- 198.199.98[.]78:8080
- 185.148.168[.]220:8080
- 139.196.72[.]155:8080
- 45.118.115[.]99:8080
- 178.79.147[.]66:8080
Top 3 – Formbook
Formbook is an infostealer malware that ranked third place with 13.6%.
Like other info-stealer malware, it is mainly distributed through spam emails. The distributed file names are close to each other.
- doc_2863910036.exe
- hsbc customer information.exe
- HSBC Payment Advice.exe
- IMG_00945006777.exe
- Order EHP 5286 2022.scr
- ORDER S20220211-601.exe
- PQR-380.HESS – STRUCTURE MATERIALS FOR PUNCHLIST.exe
- sewoong ref no. mq-3018 & mq-3019.exe
As Formbook is injected in a normal process that is in the directory of explorer.exe and system32, the malicious behaviors are performed by the normal process. Besides user credentials in the web browser, the malware can steal various information through keylogging, clipboard grabbing, and web browser form grabbing.
Below is the list of confirmed C&C server URLs of Formbook.
- hxxp://www.alpeshpate[.]com/mwfc/
- hxxp://www.becu84ts[.]com/gcnc/
- hxxp://www.besrbee[.]com/yrcy/
- hxxp://www.harsors[.]com/r3hg/
- hxxp://www.mefacin[.]online/k12t/
- hxxp://www.minimi36[.]com/aemt/
- hxxp://www.sacremots[.]com/ahb9/
- hxxp://www.sacremots[.]com/tod8/
Top 4 – Lokibot
Lokibot ranked fourth place with 12.3%. It is an info-stealer malware that leaks information about programs such as web browsers, email clients, and FTP clients.
Being a malware that is distributed through spam emails, it shares similar file names with other malware spam emails.
- B2B – TX 424 Feb 2022.exe
- ENQUIRY LIST FEB72022.exe
- PO 220208-001A.exe
- PO 220209-0081A.exe
- PO_FF-feb_2202F25.exe
- PO-3451099 (09_02_22).exe
- Purchase order.exe
As shown below, most Lokibot C&C server URLs tend to end in fre.php.
- hxxp://copictory[.]cf/fashion/fre.php
- hxxp://nesofirenit[.]gq/portion/fre.php
- hxxp://rkfs[.]xyz/MV1/w2/fre.php
- hxxp://secure01-redirect[.]net/gc18/fre.php
- hxxp://secure01-redirect[.]net/gc23/fre.php
- hxxp://secure01-redirect[.]net/gc26/fre.php
- hxxp://sudais.com[.]pk/876/2Panel/fre.php
Top 5 – RedLine
RedLine ranked fifth place with 5.5%. The malware steals various information such as web browsers, FTP clients, cryptocurrency wallets, and PC settings. It can also download additional malware by receiving commands from the C&C server. Like BeamWinHTTP, there have been numerous cases of RedLine being distributed under the disguise of a software crack file.
The following are the confirmed C&C server domains for RedLine:
- 185.215.113[.]83:60722
- 185.215.113[.]83:60722
- 185.215.113[.]94:55535
- 45.142.215[.]47:27643
- 49.12.5[.]55:17967
- 91.243.32[.]42:52075
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.



