ASEC Weekly Malware Statistics (September 12th, 2022 – September 18th, 2022)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known malware. This post will list weekly statistics collected from September 12th, 2022 (Monday) to September 18th, 2022 (Sunday).
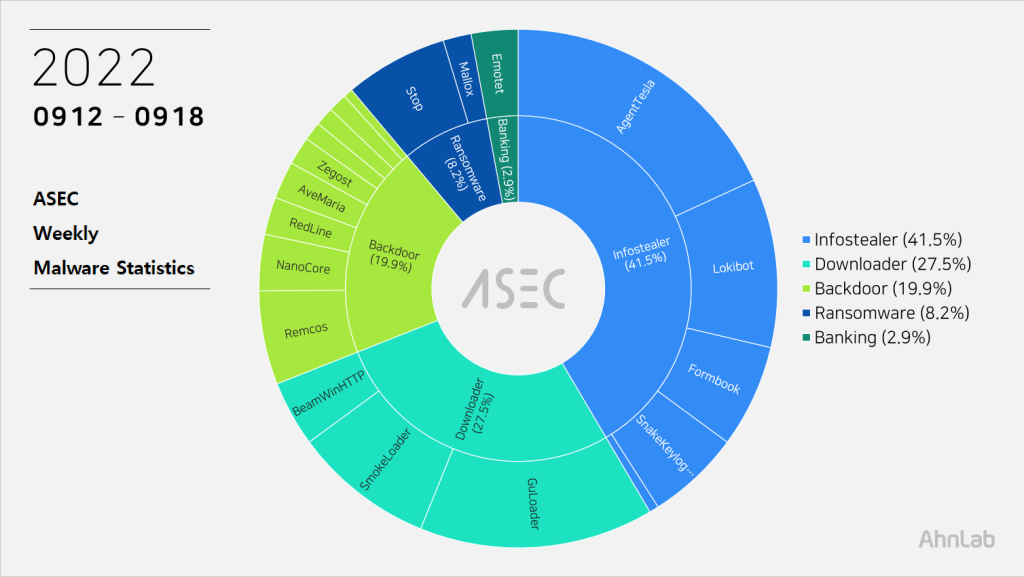
For the main category, info-stealer ranked top with 41.5%, followed by downloader with 27.5%, backdoor with 19.9%, ransomware with 8.2%, and banking malware with 2.9%.
Top 1 – AgentTesla
AgentTesla is an infostealer that ranked first place with 18.1%. It is an info-stealer that leaks user credentials saved in web browsers, emails, and FTP clients.
It uses e-mail to leak collected information, and there are samples that used FTP or Discord API. C&C information of recently collected samples is as follows.
- server : smtpout.secureserver[.]net (173.201.193[.]229)
sender : bijupaulose@glamdustasia[.]com
receiver : 99lindatessin@gmail[.]com
user : bijupaulose@glamdustasia[.]com
pw : Eva****204 - server : mail.hindusthan[.]com (192.185.46[.]31)
sender : fombbsr@hindusthan[.]com
receiver : sundus.saharbmacapital@gmail[.]com
user : fombbsr@hindusthan[.]com
pw : f1****3
As most are distributed through spam emails disguised as invoices, shipment documents, and purchase orders, the file names contain such words shown above (Invoice, Shipment, and P.O. – Purchase Order). Multiple collected samples were disguised as files with extensions of pdf and xlsx.
- SOA.exe
- payment_copy.exe
- inw)9876567849-4976456478.exe
- Joh******_-PO-_216238068_PDF.exe
- june_transaction_receipts_090028783.ex.exe
- RSW~0987365367-049874664789P-PLS.exe
- QTN NO 11478.exe
- Wire TT Copy012522430xxxxxpmp20221309.exe
Top 2 – GuLoader
GuLoader, which ranked second place with 14.6%, is a downloader malware that downloads additional malware and runs it. It was packed with Visual Basic language in the past to bypass detection, but is now distributed in a form of an NSIS installer. It used to be known as CloudEye but got the name GuLoader because Google Drive is frequently used as a download URL. In addition to Google Drive, various URLs such as One Drive from Microsoft and Discord can also be used.
- kngpdrp[.]shop/PL341
- index.php gwinaz[.]pro/PL341/index.php
- 85.31.46[.]229/sos/pvugVPOGOuOEnf78.afm
- siasky[.]net/PAN0gbpVRyiCOOw8UAcSXcMLiO1w3yFZdaOmS_4t3-a-Vg
- kronlux[.]ro/mon2.pcx
- vortexfoto[.]hu/PVC.toc
Instead of being downloaded in a file form, GuLoader is downloaded on memory to avoid detection, and the downloaded file is encoded, not PE. It is then executed after being decoded in the memory, downloading malware such as infostealer (Formbook and AgentTesla) and RAT (Remcos and NanoCore).
As most are distributed through spam emails disguised as invoices, shipment documents, and purchase orders, the file names contain such words shown above (Invoice, Shipment, and P.O. – Purchase Order). Some samples have extensions disguised as document files such as pdf and xlsx or Auto CAD blueprint files such as dwg.
- rfq.exe
- po4624524-8659923530035201.exe
- HTS32100-19-2306F.exe
- Inv_#MB-220830-1A_-Shipping_Document_(CN).exe
- DOCUMENT.EXE
- Specfication_for_SRPI_Project.exe
- fe**x – [[-email-]].exe
Top 3 – Lokibot
Lokibot malware ranked third place with 10.5%. It is an info-stealer that leaks information about programs such as web browsers, email clients, and FTP clients.
The following is a list of the most C&C servers for the malware.
- 162.213.249[.]190/?hello00x
- sempersim[.]su/gj23/fre.php
- tixfilmz[.]ml/Eze/PWS/fre.php
- 162.0.223[.]13/?hello00x
- 171.22.30[.]147/user/five/fre.php
- 208.67.105[.]161/jungleone/five/fre.php
Top 4 – SmokeLoader
Smoke Loader is an info-stealer / downloader malware that ranked fourth place with 8.8%. For an analysis report related to Smoke Loader, refer to the ASEC Report below.
[PDF] ASEC REPORT vol.101_Smoke Loader Learns New Tricks
The confirmed C&C server URLs are as follows.
- cracker[.]biz
- host-file-host6[.]com
- ginjin[.]org
- susuerulianita1[.]net
- furubujjul[.]net
Top 5 – Formbook
Formbook ranked fifth place with 6.4%.
Like other info-stealer, it is mainly distributed through spam emails. The distributed file names are close to each other.
- 769377HBH998___PDF.exe
- GMT_TBN(28K)_-_VESSEL_DETAILS.exe
- PDF RENOBLE BROKER UK LTDNEW ORDER MT110000 FOBUSD.exe
Formbook is injected into normal processes (one is a running explorer.exe and the other is in system32) that perform malicious behaviors. Besides user credentials in the web browser, the malware can steal various information through keylogging, clipboard grabbing, and web browser form grabbing.
Below is the list of confirmed C&C server URLs of Formbook.
- http://www.derpallet[.]info/q40s/
- http://www.dockudos[.]info/poj5/
- http://www.envacatures[.]com/e7nb/
- http://www.gogojackmin[.]com/txuu/
- http://www.ideawage[.]info/0yv3/
- http://www.idgeformedia[.]com/bwe0/
- http://www.irusmedia[.]info/nm2c/
- http://www.iuxinnian[.]com/eauu/
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.



