njRAT Malware Distributed via Major Korean Webhard

njRAT malware is a RAT malware that steals user’s personal information and runs by receiving the attacker’s command. This malware is constantly being distributed to users in Korea.
Upon analyzing the detection log, AhnLab ASEC team discovered that njRAT is mostly distributed via Webhard and torrent websites, disguised as ordinary file such as video games, authentication tools, and utilities. In most cases, PCs are infected with malware the moment the source program is run, making it difficult for users to realize that their PCs are infected.
In this report, ASEC analysis team will introduce the cases where njRAT malware is being distributed via Korean Webhard sites. Reverse tracking of njRAT filenames revealed the posts in a major Korean Webhard site that are distributing the malware.
Furthermore, the previously uploaded original files without the malware were found on the same website, and upon comparing the two different versions, the following differences were revealed.

The malicious archive file contained savework.dll and d4work.dll which are the additional files that do not exist in the original file. savework.dll is a normal Game.exe file that underwent a name change, and d4work.dll is the njRAT malware. The filename extension for both files is .dll, but in reality, they are executables (.exe).

The attacker distributed the file after changing the name of the video game executable in the original file, adding the malware, and developing an executable that runs both the malware and the game.
Game.exe that the attacker developed and added is a file developed using Vbs2Exe, and it uses a normal Game.exe icon to disguise itself. Vbs2Exe is a program that converts a script language VBS into an executable in a form of PE. A file that is built using this program is structured to load and run commands in the resource area.
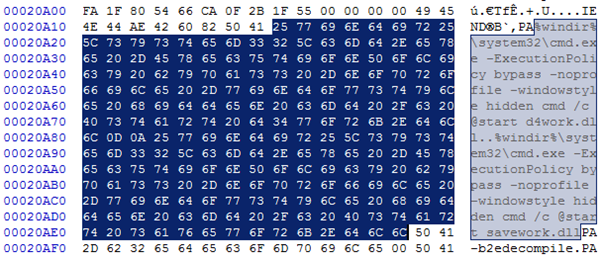
When the file is run, d4work.dll (njRAT malware) and savework.dll (original Game.exe) is run via the following command, infecting the PC with the malware and running the game at the same time.
- %windir%\system32\cmd.exe -ExecutionPolicy bypass -noprofile -windowstyle hidden cmd /c @start d4work.dll
- %windir%\system32\cmd.exe -ExecutionPolicy bypass -noprofile -windowstyle hidden cmd /c @start savework.dll
Upon running the d4work.dll file, it copies itself with a specific filename under %appdata%, creates a shortcut, and adds autorun via registry. Afterward, it connects to C2, awaits the attacker’s command, and performs various malicious behaviors following the attacker’s command.
Among the njRAT malware distributed during the recent week, some of the filenames and filepaths that are believed to be distributed via Webhard are as follow: Many are being distributed under disguised game or a utility file, and diverse Korean Webhard sites are being misused as the source of distribution.
- \Xdisk\[rj289299]asylum\Sera&Noel-The whereabouts of the kidnapped princess-\game.exe)
- \Princess Quest Shame and Dishonor ver101\new folder\game.exe)
- \motherslessons\game.exe
- \Get hot with the hottie!\the lady is in heat\d3dcompiler_46.dll)
- \fileXX\(190329)rpg with subscription plan bewitching sword2 ver.1.0\steam.com)
- \Windows 10 genuine validation tool\Windows 10 genuine validation tool.exe)
- \the apostle of gospel\d4work.dll)
- \Xdisk\sinnenn_ver1\game\d4work.dll)
- \Change hard disk serial number\set up.exe)
- \Hancom 2020\set up.exe)
- \SuddenAttack hack sa (1)\sa.exe)
- \Xdisk\loaned wife\ps\aa\reget.exe)
- \Life on an uninhabited island\d3dcompiler_46.dll)
- \Naruto\reget.exe)
- \FileX download\[rj291663] Female Knight Frey 1.0\reget.exe)
As shown in the examples above, the malware is being distributed actively via file-sharing websites such as the Korean Webhard, therefore users must remain vigilant. Executables downloaded from a file-sharing website must be run with caution. AhnLab recommends users to download products from the developers’ official websites.
[V3 Detection]
- Trojan/Win32.Loader.C4183142
- Backdoor/Win32.Korat.C4182520
[Relevant IOC Info]
- md5: 1c359f9edf43f2986f782b631f418ebb (악성 Game.exe)
- md5: 88e4da56049f4aa60a1ebeb47ad4dafa (d4work.dll)
- C2: so69.kro.kr




