[Caution] Distribution of WastedLocker Ransomware Targeting Specific Companies
![[Caution] Distribution of WastedLocker Ransomware Targeting Specific Companies](https://asec.ahnlab.com/wp-content/uploads/2020/09/locker_finger-1-803x490.png?crop=1)
On July 23, smartwatch & wearable manufacturer ‘Garmin’ was attacked by ransomware named WastedLocker, resulting in cessation of service and production line.
The developer of this ransomware is a Russian cybercrime group that goes by the name of ‘Evil Corp’ and it is assumed that after launching an APT attack, they used an invasive testing tool Cobalt Striker to distribute WastedLocker ransomware.
WastedLocker is typical ransomware that encrypts system files and asks for financial compensation in return for decrypting the system files. In the case of WastedLocker ransomware, it has a command interface that can control the range of encryption depending on the specific parameter condition that is sent to the program. It is assumed that the attacker designed the malware in this way to narrow the encryption target range down to specific targets within the resources secured from the infected system.
WastedLocker performs 4 major malicious behaviors:
| 1. Create a copy of the self in a specific ADS area and run recursion (*Camouflage mechanism). 2. If not run as administrator, perform UAC BYPASS (*Privilege escalation mechanism). 3. Perform an encryption process based on a specific parameter (*Ransomware behavior). 4. Delete self (*Trace deletion mechanism). |
1. Create a copy of self in a specific ADS area and run recursion (*Camouflage mechanism)
1.1. Copy arbitrary exe or dll file within the system folder to a temporary folder
└ %AppData%\Roaming\[random]

1.2. Insert a copy of self to ADS area (:bin) of an arbitrarily copied file.
└ %AppData%\Roaming\[random]:bin

Inserting a copy of self to ADS area
1.3 If run as administrator, give parameter to the copy of self in the ADS area and call.
Condition 1) If parameter is entered
└ %AppData%\Roaming\[random]:bin %parameter% -r
Condition 2) If parameter is not entered (*Default: -r)
└ %AppData%\Roaming\[random]:bin –r

2. If not run as administrator, perform UAC bypass (*Privilege escalation mechanism)
2.1 Create a trick folder and use NtFsControlFile API to set mount point (c:\Windows \”).
└ %Temp%\[random]
Set mount point “C:\Windows \”
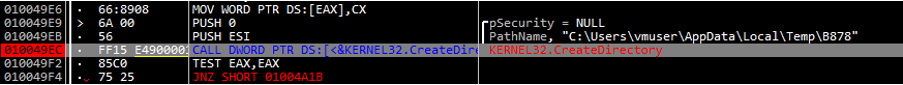
Creating a directory with random name to Temp path

Creating a directory with random name to Temp pathSet mount point “C:\Windows \”
2.2 Copy a normal system file with configured AutoElevate to trick folder.
└ %system32%winsat.exe -> %Temp%\[random]\system32\winsat.exe

2.3 Copy a normal module that winsat.exe imports to trick folder.
└ %system32%winmm.dll -> %Temp%\[random]\system32\winmm.dll

2.4 Patch winmm.dll and perform DLL hijacking.
└ Calls a copy of self in ADS area from patched DLL.

3. Perform encryption process behavior below based on parameter condition (*ransomware)
(Usecase Arg : -p, -f, -u, -r, -s )
-p: Perform encryption for designated file/directory, and perform encryption for all drives and devices again.
└ ex) -p c:\user\vmuser\desktop
-f: Perform encryption for designated file/directory.
└ ex) -f c:\user\documents\test.txt
-u: Use proof of identification (username, password) to encrypt file of designated network resource.
└ ex) -u username:password \\hostname
-r: Remove volume shadow, create a copy of self to %system32% filepath, add as service after reconfiguring ACL and run.
└ ImagePath: C:\Windows\system32\[random].exe %parameter% -s
-s: Branch to service routine and perform encryption for all files (parameter-X) or designated file (parameter-O).
<Encryption Process>
1. Select files for directory listing & encryption.
└ Extensions excluded from encryption process:
*\ntldr | \bootmgr | *\grldr | *.386 | *.adv | *.ani | *.bak | *.bat | *.bin | *.cab | *.cmd | *.com | *.cpl | *.cur | *.dat | *.diagcab | *.diagcfg | *.dll | *.drv | *.exe | *.hlp | *.hta | *.icl | *.icns | *.ics | *.idx | *.ini | *.key | *.lnk | *.mod | *.msc | *.msi | *.msp | *.msstyles | *.msu | *.nls | *.nomedia | *.ocx | *.ps1 | *.rom | *.rtp | *.scr | *.sdi | *.shs | *.sys | *.theme | *.themepack | *.wim | *.wpx
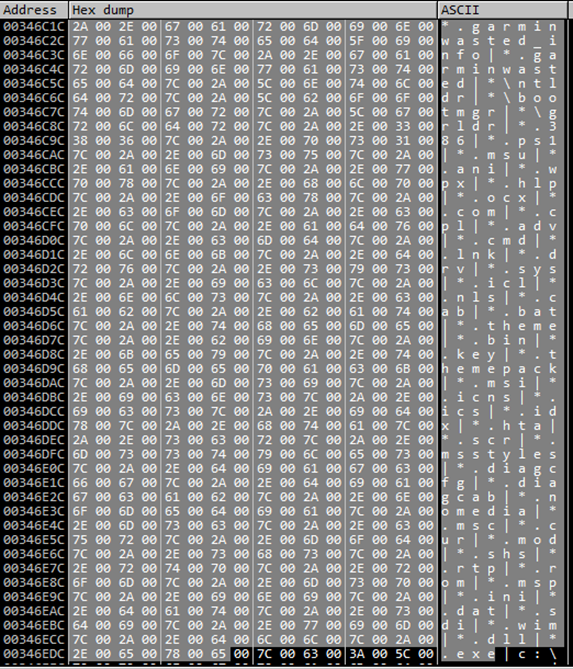
└ Directories excluded from encryption process:
*\$recycle.bin* | *\appdata* | *\bin* | *\boot* | *\caches* | *\dev* | *\etc* | *\initdr* | *\lib* | *\programdata* | *\run* | *\sbin* | *\sys* | *\system volume information* | *\users\all users* | *\var* | *\vmlinuz* | *\webcache* | *\windowsapps* | c:\program files (x86)* | c:\program files* | c:\programdata* | c:\recovery* | c:\windows* | c:\users\ %USERNAME%\appdata\local\temp* | c:\users\ %USERNAME%\appdata\roaming*
Directories excluded from encryption
2. Perform encryption for selected file and create ransom note.
└ Encryption algorithm/block mode: AES-256 / CBC
└ Encryption key: 256-bit key and 128-bit IV randomly generated by internal algorithm
256-bit key and 128-bit IV that is randomly generated each time
└ Decryption key: Use AES key that was used in encryption and RSA public-key with integrated IV (4096-bit) to encrypt, and perform logging to ransom note via final Base64-encoding (*Decryption key can be obtained upon obtaining attacker’s RSA private key.)
4096-bit RSA public-key
Decryption key that was logged to ransom note after RSA encryption and final Base64-encoding
└ Encrypted filename: [filename].garminwasted (*garmin: name of target company / wasted: ransomware name)
└ Ransom note name: [filename].garminwasted (*garmin: name of target company / wasted: ransomware name)
4. Delete self (*Trace deletion mechanism)
Use del command of command line to delete self
[Analysis Summary]
Firstly, to hide, WastedLocker ransomware creates and re-executes a copy of itself within a specific ADS area. If it wasn’t run as administrator, it attempts UAC BYPASS and performs an encryption process based on the parameter entered in the program. And at the end, when the encryption process is over, it completely deletes itself or the copy of itself to remove all traces.
AhnLab’s anti-malware software V3 detects the malware using the following aliases.
[File Detection]
– Trojan/Win32.WastedLocker.R345840 (2020.07.24.03)
– Trojan/Win32.Ransom.C4170354 (2020.07.28.04)
[Behavior Detection]
– Malware/MDP.SystemManipulation.M2255 (2019.08.02.09)




