Shadow of WannaCry, 2019 SMB Exploitation
WannaCry (or WannaCryptor), which infected more than 300,000 systems in May 2017 and gripped the whole world in fear, spread rapidly by exploiting a Windows SMB security vulnerability (MS17-010). Precaution is required since the recently discovered malware is a CoinMiner, a type of malware that mines cryptocurrency.
This report details the analysis by AhnLab on the attack cases that exploited the SMB vulnerability (MS17-010) from 2018 to the first quarter of 2019.
1. NRSMiner Malware Attack (2018)
In March 2018, a company was found infected with NRSMiner malware. By exploiting the SMB vulnerability (MS17-010) like WannaCryptor, this malware scans the internal network of the company and installs the malware that mines the cryptocurrency Monero if the system is vulnerable. NRSMiner consists of a package file in the ZIP compressed file format, and has a different filename for the package “MsraReportDataCache32.tlb” for each variant.
Figure 2-1 shows the structure of the NRSMiner package. Once the system is infected, one of the file names, Srv or Srv64, is changed to “tpmagentservice.dll” according to the installed OS environment and is registered as a service. This then later creates and executes the attack modules and the mining tool later. Spoolsv and Spoolsv64 executables load the package file, installs necessary modules depending on the environment, and scans the MS17-010 vulnerability in the system. Hash and Hash64 are XMRig, a public tool known to mine Monero. Crypt is a compressed folder containing publicly available MS17-010 vulnerability-related tools and files.

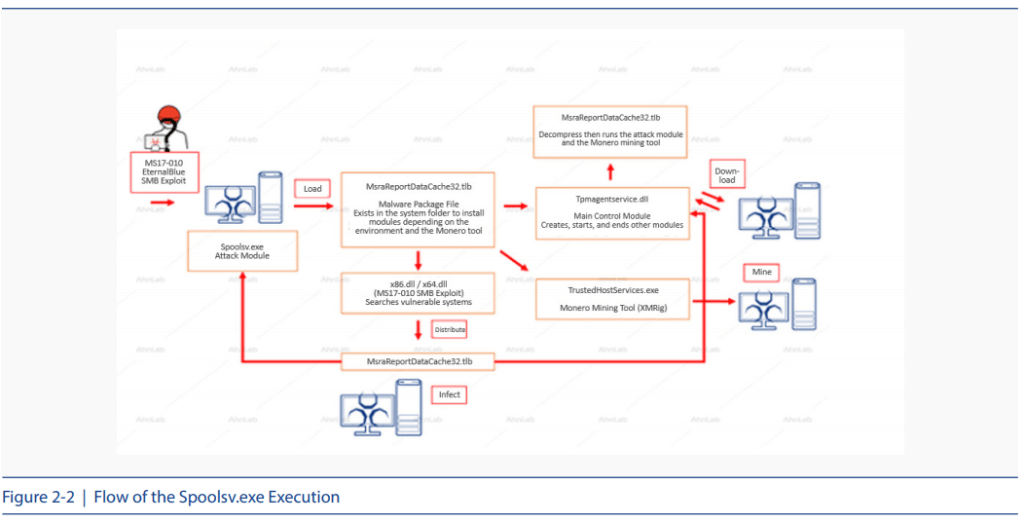
Figure 2-2 shows how the Spoolsv.exe file runs an attack module. This file performs the function of unpacking the “MsraReportDataCache32.tlb” package and loading the internal modules. As shown in Figure 2-1, the TLB file consists of: XMRig (Public Monero mining tool) called hash and hash64, attack modules called spoolsv and spoolsv64, main modules called srv and srv64, and a compressed file in the name of Crypt that includes tools and files related to the EternalBlue SMB vulnerability (MS17-010). When the Spoolsv.exe file is executed, it runs six threads and performs the following series of steps. First, it creates a folder in the system as shown in Table 2-1, loads the malicious package file, and decompresses the loaded file.

To propagate the SMB vulnerability exploit, it runs the svchost.exe (Eternalblue-2.2.0.exe) and the spoolsv.exe (Doublepulsar-1.3.1.exe) file in the Crypt compression folder inside the MsraReportDataCache32.tlb file. Depending on the Windows environment, the x64.dll or x86.dll file is loaded and the file names are hard-coded in spoolsv64.exe.
Finally, a vulnerability scan is conducted within the thread of the spoolsv64.exe process. If successful, it copies the TLB file from the x64.dll and x86.dll module to the target system and conducts decompressions. Then the filename is changed to “tpmagentservice.dll,” the srv service is registered, and the spoolsv64.exe file is executed again.
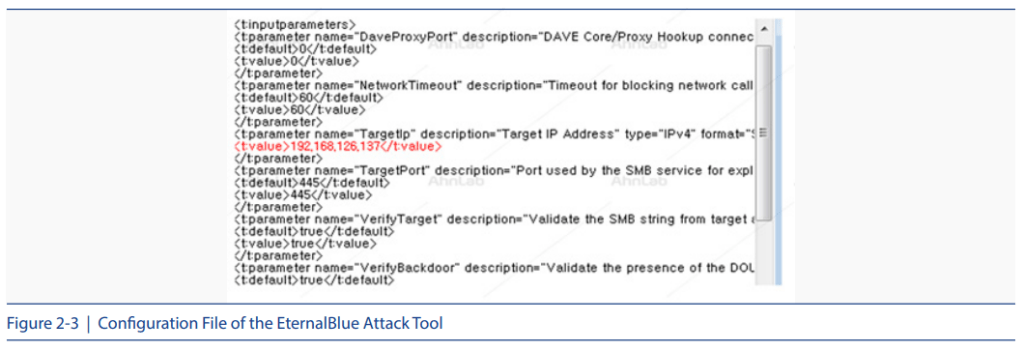
The internal network propagation using the vulnerability proceeds as shown in Figure 2-3. The example is based on the x64 window.
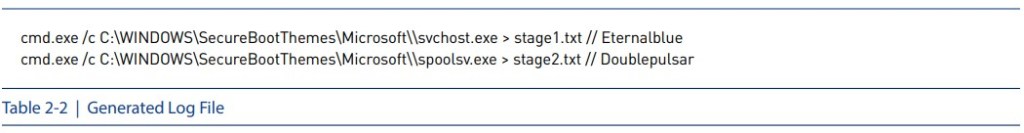
When the EternalBlue tool is executed, two log files stage1.txt and stage2.txt are created as shown in Table 2-2.
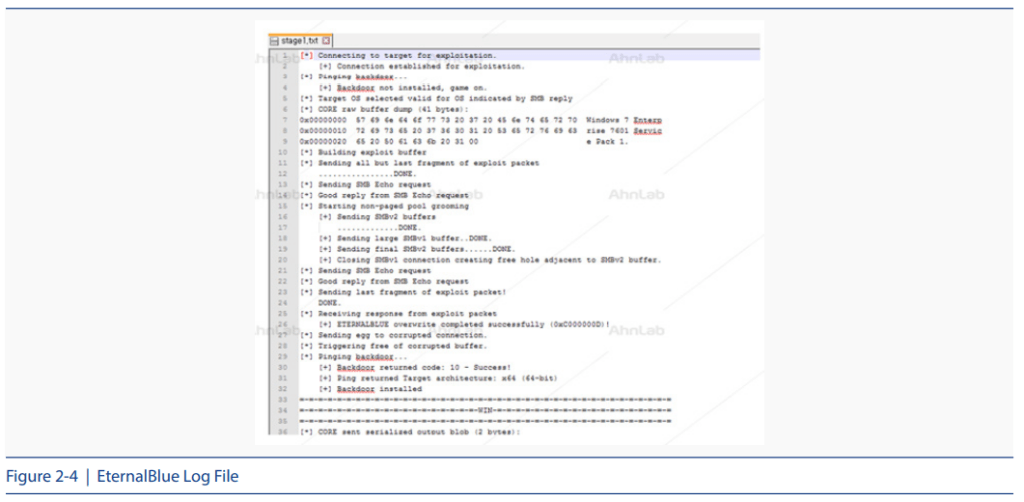
The stage1.txt file is the execution log file of the EternalBlue tool, and details are shown in Figure 2-4.
The vulnerability packet is also sent to the target system as shown in Figure 2-5.

Then the lsass.exe file creates a malicious package file, MsraReportDataCache32.tlb, in the remote system it has infiltrated the system. The content of this package file is shown in Figure 2-6. The package file records information in 102,400 bytes each time to the file and directly sends the plain binary without the additional step of encryption.
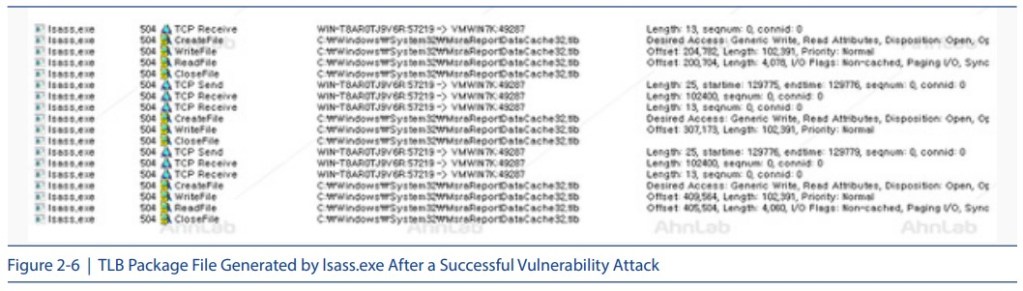
The TCP port for packet transmission uses the dynamically allocated 492xx and 572xx bands. For testing, src: 49287 and dest: 57219 ports were used.
If the vulnerability attack is successful, the “MsraReportDataCache32.tlb” file is transferred and the transferred file is decompressed. The decompressed folder is saved in the same path, Windows\SecureBootThemes\Microsoft. The name of the srv64 file is changed to “system32\ tpagentservice.dll”, copied to the system and registered as a service for operation. This is the main control module which runs the spoolsv64.exe file within the TLB package and finds another vulnerable system to distribute the package file. Finally, the XMRig tool, in the name of hash or hash64, for mining Monero is executed. The mining pool address is shown in Table 2-3.

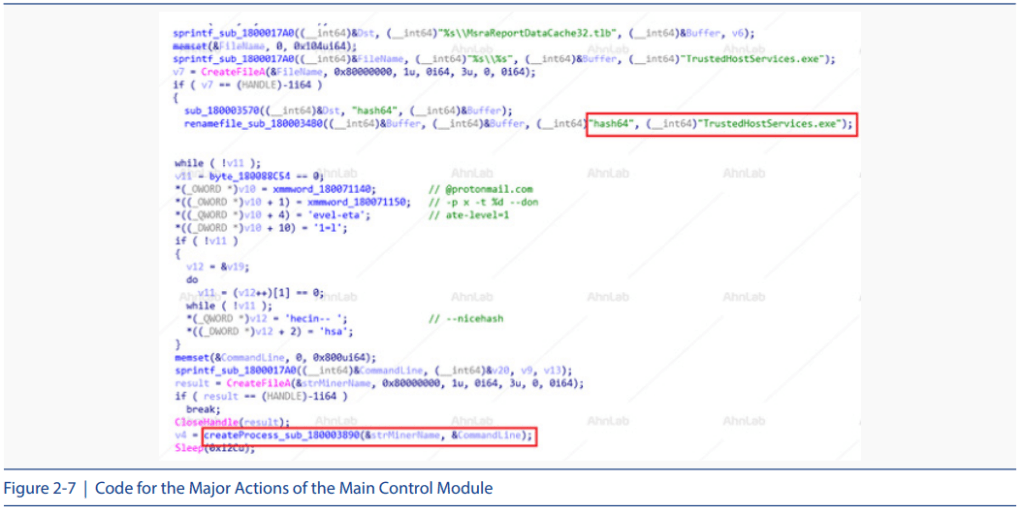
The main control module decompresses the malware package file “MsraReportDataCache32. tlb” and creates and executes the attack module and “TrustedHostServices.exe”, the Monero coin mining program. The code for the main actions of the control module is shown in Figure 2-7.
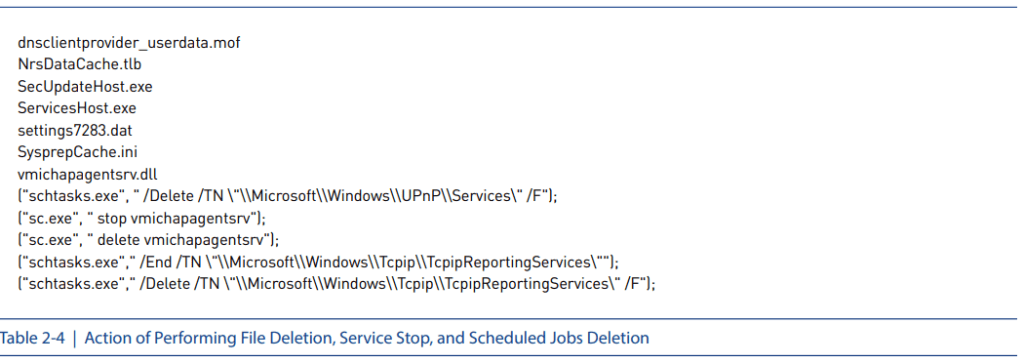
Also as shown in Table 2-4, the control module deletes all files that are presumed to be the previous version, stop services, and deletes scheduled jobs.
Also, the main control module has its own Mongoose-based web server feature with the role of transmitting the MsraReportDataCache32.tlb package file to other infected system using the port 26397. Also, if an external internet connection is available, the malicious package file is downloaded from the remote server as shown in Figure 2-8.
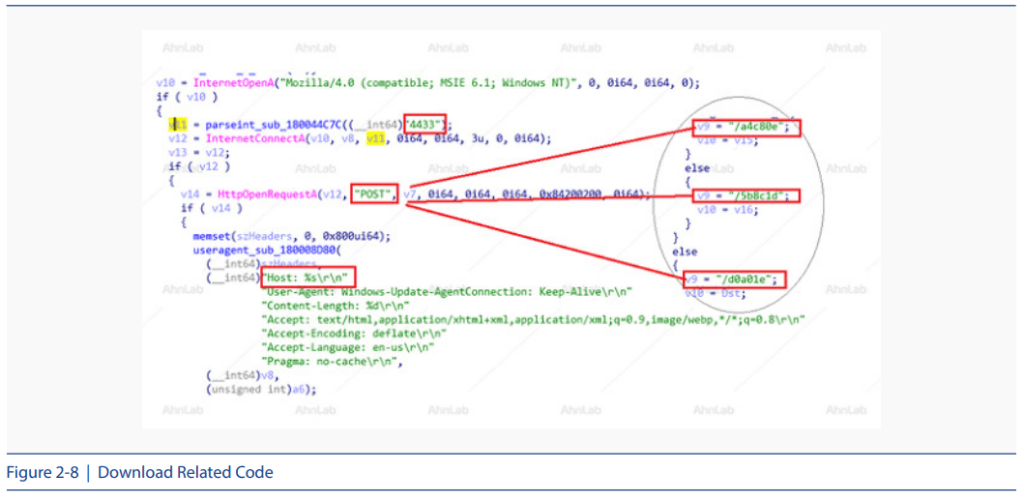
The TLB package is updated through this web server using the download address shown in Table 2-5.

2. Analysis of the POS Attack Case (2018)
In July 2018, 100,000 POS terminals were hacked in South Korea. The hacking caused most POS terminals to disconnect from the internet and prevented normal operation of the payment service. One of the companies which was the victim of this hacking incident posted about their service failures that occurred due to the exploit of the Windows security vulnerability and also the recommendations for security patches.
Most of the infected terminals were running the Windows XP operating system that has the SMB vulnerabilities and did not have the security updates applied. The threat actor exploited this vulnerability, like the WannaCryptor ransomware, to install Gh0st RAT, which is a backdoor malware and CoinMiner. The Figure 2-9 shows the operation process of the malware.
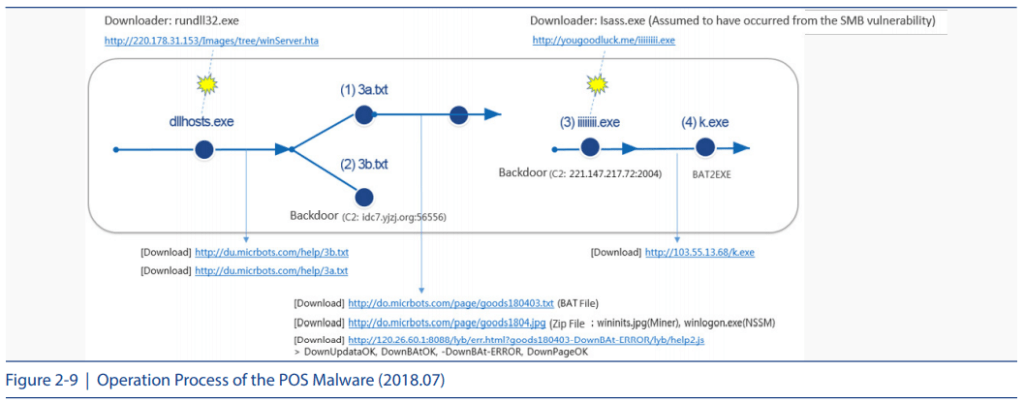
The AhnLab Smart Defense (ASD) engine was used to find the iiiiiiii.exe file, the third file in Figure 2-9 which was created by “lsass.exe”, Windows system file. From this, we can deduce that this is an attack exploiting the SMB vulnerability which was propagated by an infected system. The malware for the remote control Gh0st RAT is “3b.txt”, the second file in Figure 2-9. The first file, “3a.txt”, downloads CoinMiner, a tool for mining cryptocurrency.

AhnLab’s V3 products provide the behavior detection function against such SMB vulnerability attacks. The report count in Figure 2-10 shows that there was a sudden rise in the attack attempts between June 24th and July 7, 2018 which is the same period as the POS hacking incident in Korea.
3. Analysis of the POS Attack Case 2 (2019)
In February 2019, another case of an infection that uses the CoinMiner malware to exploit the SMB vulnerability was found targeting the South Korean POS terminals. The overall operation process of this malware is shown in Figure 2-11 below.
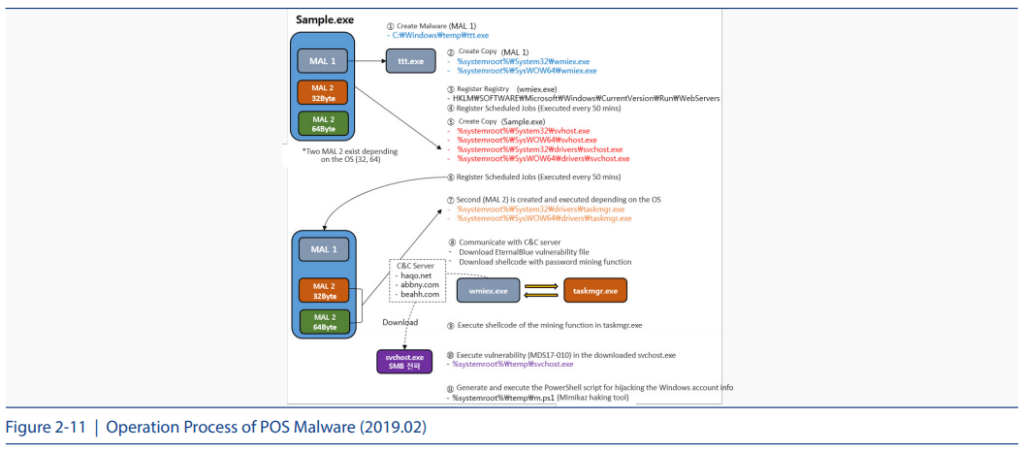
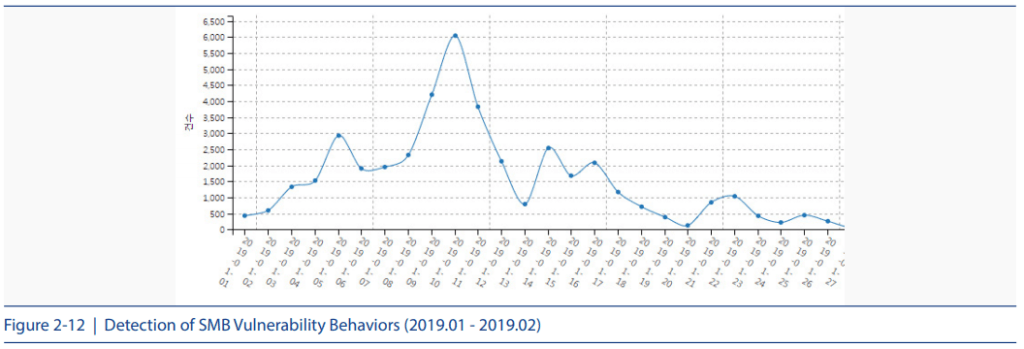
The sample.exe file is a malware which contains two different types of 32-bit and 64-bit files to apply depending on the operating environment. The “svchost.exe” file copied in the drive folder in the system path (%system%drivers) performs the actual role of initiating the SMB vulnerability attack. The last file that is downloaded and installed is the CoinMiner malware and Mimikatz, a hacking tool for stealing the Windows account information. Unlike the POS attack of July 2018, the interesting characteristics of the CoinMiner malware is that it is a script rather than an executable. The detection report in Figure 2-12 shows a sudden rise in the SMB vulnerability related behaviors from a specific period of January to February of 2019.
4. Conclusion
In 2008, a worm called Conficker started to infect many systems and continued to do so, targeting the SMB vulnerability (MS08-067) to propagate the infection. Companies using the SMB service are susceptible to the types of attacks, especially when they are not applied with the recent security updates. To prevent such damage, the following security patches related to the Microsoft Windows operating system’s EternalBlue SMB vulnerability (MS17-010) must be applied.
In view of the March 2010 NRSMiner malware attacks and the POS attacks which took place in February and July 2018, it seems that the SMB vulnerability (MS17-010) attacks will continue in an increasingly sophisticated way. Therefore, security inspections and updates are important especially for the POS terminals in a vulnerable environment.
[SMB Vulnerability Patch]
– https://docs.microsoft.com/en-us/security-updates/securitybulletins/2017/ms17-010


