Does Operation ShadowHammer Only Target ASUS Certificate?
On March 25, 2019, Kaspersky Lab reported that ASUS’s software update server was compromised, causing the spread of malware that includes valid certificates. Kaspersky Lab named the attack “Operation ShadowHammer“. The security vendor delivered relevant information to ASUS on January 31, 2019, and the initial attack is speculated to have taken place between June to November of 2018. Compromised ASUS Live Update is a utility program mostly installed in ASUS computer and automatically updates the components such as BIOS, UEFI, drivers, and applications.
According to Kaspersky’s statistics, over 57,000 Kaspersky product users are known to have downloaded and installed the backdoor version of ASUS Live Update. Still, it is expected that over 1 million users worldwide would be affected.
According to ASUS’s analysis, Live Update installation file (md5: aa15eb28292321b586c27d8401703494) that Kaspersky revealed, it is suggested that the purpose of this attack is to leak the information by targeting users with certain MAC address. The problem is that a disclosed installation file contains a valid certificate named ‘ASUSTek Computer Inc’. The figure below shows the valid certificate used in the malware. The serial number is ’05e6a0be5ac359c7ff11f4b467ab20fc’.

Source: https://securelist.com/operation-shadowhammer/89992/
However, AhnLab ASEC confirmed that there is an additional ASUS certificate(expired) other than the serial number above. The newly found serial number is ‘0ff067d801f7daeeae842e9fe5f610ea’.
Also, users must remain vigilant as there are various valid certificates other than ASUS among malware detected under the name of ShadowHammer.
The malware is designed to download the secondary information leaking malware upon infection. A described behavior is only applicable to users with a specific MAC address(MAC address is saved in the form of hash within the malware).
Malware distributed with the name “gxxsvc.exe” similarly checks the MAC information and then collects the user information and sends it to the address below if identified as the target; the data includes the running process list, PC name, etc.
Regarding the ASUS install file, there are two ways of downloading malware. One is to download the malware via executable file within the install file; the executable file contains PDB information in the form of AsusShellCode.pdb. The other one is to download via shellcode without any executable file. The executable with download feature included in the install file is not created as a file but exists only as a memory and has the following PDB info:
– D:\C++\AsusShellCode\Release\AsusShellCode.pdb
The URL below is commonly used as the download address. Additional analysis was unable to be carried out since the file from the URL was inaccessible. We assume that the backdoor and malicious behavior were conducted by downloaded logo2.jpg.
– https://asushotfix.com/logo2.jpg
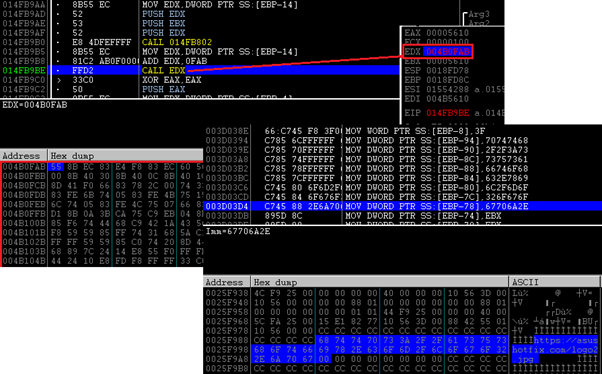
The figure below shows the code that downloads logo2.jpg via shellcode.
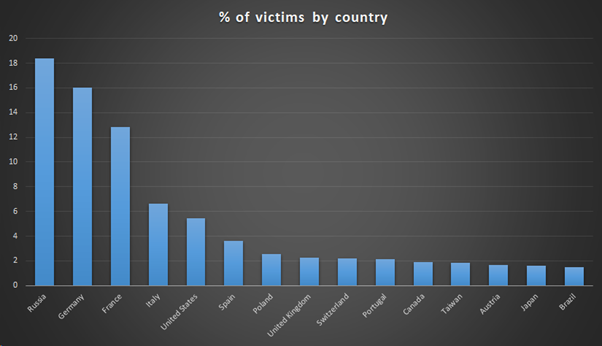
According to Kaspersky, most victims are located in Russia, Germany, and France, and there has been no attack against Korea. However, considering that various valid certificates other than ASUS were exploited in ShadowHammer attack, Korean users must remain vigilant.
Source: https://securelist.com/operation-shadowhammer/89992/
AhnLab’s V3 carried out the Generic detection against two types of modulated ASUS install files under following aliases:
– Win-Trojan/ShadowHammer.Exp (2019.03.29.03)
– Win-Trojan/ShadowHammer2.Exp (2019.03.29.03)


