[Warning] ‘Amadey’ Malware Targeting Korean Cryptocurrency Companies
Recently, AhnLab ASEC has confirmed numbers of ‘Amadey’ malware attacks targeting Korean cryptocurrency companies. The attack utilizes various email attachments such as DOC, RTF, VBS, and EXE. The following are the name of document files and executable files discovered from the attack:
*English translation will be provided for Korean file names
- Crypto Market Predictor for Desktop V2.13.exe
- Price list on blockchain 24.03.2019.exe
- Price list coins 26.03.19.bat
- 주식회사 크립토???_세무조정계산서(추가).doc (Cryto Co.???_TaxAdjustmentStatement(Added).doc)
- ?토큰전망분석.doc (Token_Forecast.doc)
- 추가안내서.hwp.exe (Addtional_Notice.hwp.exe)
- ??? 상세분석.doc (Detailed_Analysis.doc)
- ????송금내역.doc (????Payment_Details.doc)
- ??? 회원님 거래내역.doc (Transaction_Details.doc)
- ??coin 관련 문의내용.doc (??coin_Inquiry.doc)
- ??? 음악학원 2월.doc (Music_Institute_Feb.doc)
- ???? 입고내역.doc (Warehousing_Details.doc)
- 참고사항.doc. (공백) .vbs (Reference_Details.doc (blank) .vbs)
- ????_휴먼기업은행 확인건.doc (????_HumanCorp.Bank_CheckList.doc)
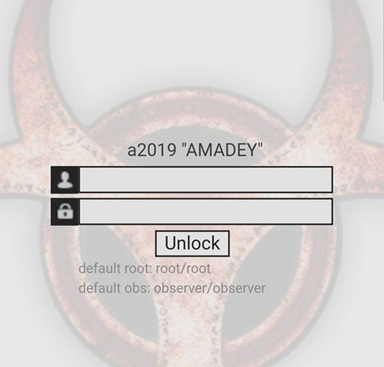
The malware is mostly spread via email attachment. The macro code inserted in the document file drives the infected PC to access the malicious website for Amadey malware distribution and download the secondary malicious file. The figure below is the screenshot of login webpage ‘https://cert-us.com’, that the user will see when one’s PC is infected by the malware. The screen can be an indicator for users to presume the matter of Amadey malware infection.
The figure below is one of the actual document files used for malware distribution. The document was written in Korean but the content is obviously about cryptocurrency. When the document file is executed, the victim will access to the attacker’s webpage(http://cert-us.com/CC/index.php) and download the secondary malicious file without knowing.

The below are address of attackers’ webpage, that were confirmed to be related to ‘Amadey’:
- http://51.15.252.131/CC/index.php
- http://ashleywalkerfuns.com/2hYbb4x/index.php
- http://kadzimagenius.com/index.php
- http://cert-us.com/CC/index.php
- http://result-viewer.com/CC/index.php
- http://servicestatus.one/b2ccsaG/index.php
- http://skcalladhellormi.xyz/s41g7gglkb/index.php
- http://software-update.live/computer/index.php
- http://datpapernl.com
- 95.215.1.196 (port:80)
- 51.15.232.120 (port:80)
- vua4cd.xyz (port:80)
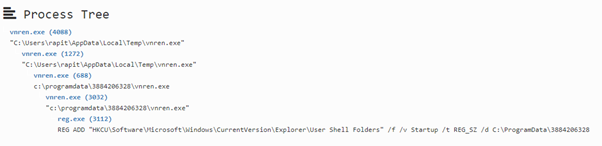
Once a downloaded EXE file infects PC, it creates files and adds them to the registry. Under “C:\ProgramData,” it creates a folder with 10 random digit name(ex. 1f29f7ab8f. Then, it duplicates itself and adds to the registry for autorun.
[Creating files]
- C:\ProgramData\1f29f7ab8f\gnhlon.exe
- C:\ProgramData\9528110fb2\kmrin.exe
- C:\ProgramData\ac7bf85f8b\gdsun.exe
- C:\ProgramData\7426030338\vnrin.exe
[Adding to the registry]
- KEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
“Startup” = c:\programdata\9528110fb2\kmrin.exe
Also, some of the malware were found out to contain the valid certificate.
The following is the information of certificates used by the malware. Also, there are some other malware without the certificate.
- Issued to: LOGI 4 LIMITED, Issuer: DigiCert EV Code Signing CA (SHA2)
- Issued to: NEON CRAYON LIMITED, Issuer: COMODO RSA Code Signing CA
- Issued to: ALISA LTD, Issuer: Sectigo RSA Code Signing CA
- Issued to: ALL COLOUR AGENCY LTD, Issuer: DigiCert SHA2 Assured ID Code Signing CA
AhnLab’s V3 products detect the malware under the following aliases:
- Trojan/Win32.Amabot
- BAT/Amabot
- BinImage/Amabot
- Win-Trojan/Logi.Exp
- Win-Trojan/Craydoor.Exp
- Win-Trojan/Alisa.Exp
- Win-Trojan/ALLColour.Exp


