New Stealer’s Suspicious Relationship with State-Sponsored Ryuk Ransomware?

AhnLab’s security analysts recently discovered a new stealer targeting to steal personal information. Apart from the new stealer’s purpose and how it works, similarities with the Ryuk ransomware was also an attention grabber. Ryuk ransomware, first found in 2018, is known to target specific countries.

The new stealer searches for files on infected systems that match specific conditions, such as extension, size, and names. Then it verifies if certain keywords are present in the files and transmits them to the attacker’s server via FTP. The new stealer searches for files, including documents, images, and archived files with various file extensions, such as, .txt, .xls, .xlsx, .doc, .docx, .pdf, .jpg, .zip, and .rar.
Where and What the Stealer Targets
From the files it searched, the stealer’s looks for files containing words, such as “personal,” “secret,” “confident,” “balance” along with names, such as Emma, Liam, Olivia, Noah, Ava, William, Isabella, James, Sophia, and Logan, as listed in Table 1.
| personal , securityN-CSR10-SBEDGAR spy radaragentnewswire , marketwired , 10-Q, 10Q , 8K , fraud , hack , NSA , FBI , defence , attack , military , tank , secret , CSI , balance , statement , checking , saving , routing , finance , agreement , SWIFT , BIC , IBAN , license , Compilation , report , secret , confident , hidden , clandestine , illegall , compromate , privacy , private , contract , concealed , backdoorundercover , clandestine , investigation , federal , bureau , government , security , unclassified , seed , personal , confident , mail , letter , passport , scans , Emma , Liam , Olivia , Noah , Ava , William , Isabella , James , Sophia , Logan |
In addition to searching keywords, it searches for strings of numbers in the “000-00-0000” format, which is commonly used for U.S. social security numbers.
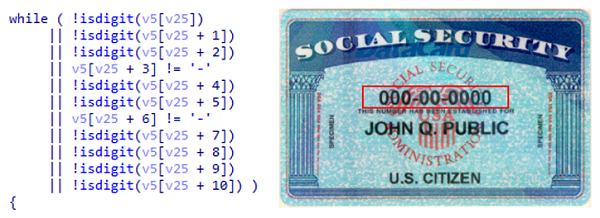
Figure 1. Code for searching text strings (left) and an example of the U.S. social security number (right, Wikipedia.org)
The stealer may have been designed to target specific countries based on the fact that the stealer searches text strings and names in English, uses U.S. social security number format, and includes names of national investigation institutes, such as NSA, FBI, federal, bureau, in the keyword search.
Commonalities Shared with the State-Sponsored Ryuk Ransomware
The new stealer was first discovered this year in mid-September. Although this stealer targets users’ personal information, the Trojan contains identical text strings to that of Ryuk ransomware. Also, the internal code flows were similar. Additional evidence that backs up its relationship with Ryuk ransomware was that file names, such as “RyukReadMe.txt,” was excluded from transmission. This name is identical to the name of the ransom note file in systems infected by the Ryuk ransomware.
Ryuk ransomware excluded files named, “AhnLab,” when encrypting files and folders in infected systems. AhnLab, Inc. is a one of the most well-known cybersecurity vendors in South Korea. As shown in Figure 2, the newly discovered stealer code also uses text strings to check for the existence of folders related to AhnLab products when searching for files. When found, it excludes the file from the breach.
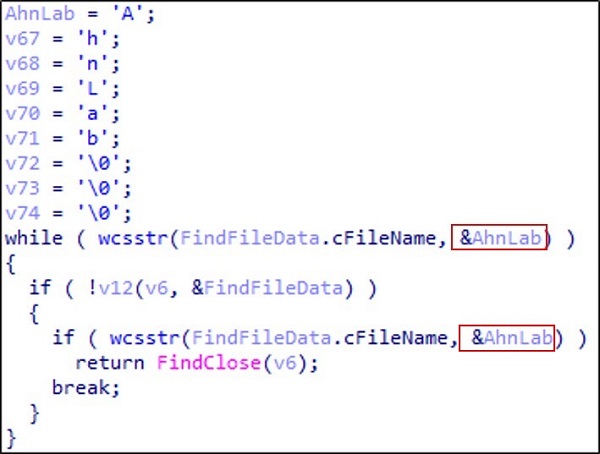
Figure 2. String code scanning folder named AhnLab
In the meantime, the malware, which is assumed as an early version of the stealer, scans the language setting of the infected systems and exclude systems using specific locales or languages, as listed in Table 2. However, the newly discovered stealer did not have this process.
| Korea, Russia, ukraina, Belarusian, Hong Kong SAR, Czech, Romanian, Albanian, Georgian, Rhaeto-Romanic |
How the New Stealer Works
As mentioned earlier, upon the execution of the malware, this stealer scans for files containing specific extensions and keywords. Then, it transmits files smaller than 50,000,000 bytes to the attacker’s C&C server via FTP. Files with “.docx” or “.xlsx” extensions are then unzipped using the libzip library before scanning for specific keywords. Therefore, the malware only executes when the unzipping libzip library exists on the infected system.
After being executed, this stealer deletes the dropper file used to transmit itself to the infected system. Such operation is assumed to have been designed to prevent tracing by security analysts.
AhnLab’s anti-malware solution, V3 detects this malware and blocks the C&C server URLs it accesses as follows.
<V3 Product Alias>
– Trojan/Win32.Ryukstealer
<URLs blocked by V3>
66.42.76.46/files_server/a8-5
109.236.92.162/upload/files/military2
185.254.121.157/upload/files/a71, and many others


