Trick or Treat! Corporate targeting Trickbot
Trickbot, orginally a banking Trojan, aims to collect and leak corporate confidential information. Recently, attackers have distributed fake Word files and obfuscated scripts to trick corporate users in downloading the Trickbot downloader. Thereby, extra attention is required to prevent downloading Tickbot.
When the user opens the Word document attachment in the email, it will tell the user to click the “Enable Content” button with the message, “Document created in the previous version,” as shown in Figure 1. However, this is a trick to activate the VBA macro and execute a malicious script. The script hides within the body paragraph with white text color.

Figure 1. Trickbot distributed as a Word file
When the user clicks the ‘Enable Content’ button in Figure 1, the script executes without the user’s permission. Subsequently, false alerts, such as ‘MS Word error’ and ‘Insufficient permissions,’ are displayed, as shown in Figure 2. These alerts automatically disappear in 30 seconds.
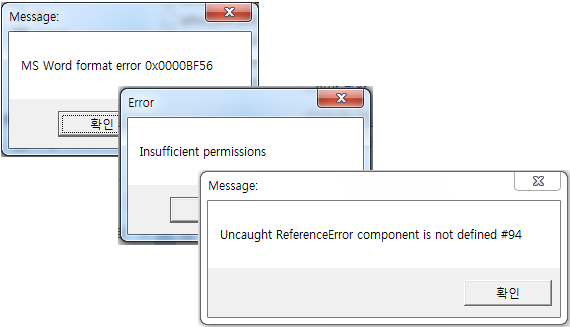
Figure 2. False alerts
This script checks the information on the PC environment, such as OS and processes, to determine whether the infected PC is an analysis system or sandbox. If confirmed as an analysis system or sandbox, it generates an error and immediately ends the operation. If confirmed as a regular PC, it sends the collected PC information to the attacker’s C&C server and copies the script to the Startup folder under “shell.jse,” allowing the script to execute with every boot.
Also, it downloads the malicious files from the C&C server to install them under a random numeric name in “%TEMP%” path of the infected PC. The malware downloaded here is Trickbot, which disables Windows Defender, collects significant information, stores it in the “C:\User\(User Account)\AppData\Roaming\(Specific Name)\data\” path, and sends it to the attacker.
Attackers are constantly changing their attack techniques to bypass the suspicion of the users and the detection of security solutions, such as vaccine programs. Recently, they have been avoiding the suspicion of users through various methods, including the method of adding a print object called ActiveDocument.PrintOu to the macro code of the document to display a printing task windows when macro is executed.
AhnLab’s V3 products detect the malware under the following aliases:
<V3 Product Aliases>
– VBA/Dropper.S1~S6
– Win-Trojan/Suspig9.Exp
– Trojan/Win32.Trickbot



