Be Careful with Excel File Disguised as ‘Wage Statement’ Distributed via Email
Users should be careful as many spam emails with downloader malware targeting Korean companies have been distributed.
The titles of detected spam emails are “October Wage Statement” and “Estimate for XX”. These spam mails attach Microsoft Office Excel document files by the name of “QF001_1093_101819.xls” and “P001_102019_4472.xls” or direct to phishing webpage disguised as OneDrive to prompt users to download malware. The sender is “Kim Sun-ah” but the title and content are likely to change.
When a malicious excel file is run, the screen appears to prompt users to use the macro. Once it is allowed, the malicious macro is executed. Upon allowing the use of macro, a loading screen pops up while the macro is run. The macro code included in the excel document drops, loads, and then execute the malicious DLL.


The routine of loading and running malicious DLL follows afterward, which means that malicious behavior is carried out by excel.exe process(malicious DLL inside the file). The malware drops and loads DLL of different versions for x86 and x64 environments, but they share the same feature.

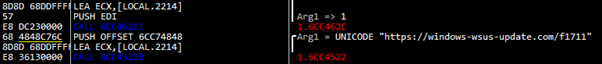
DLL malware connects to C2 and performs its downloader tasks after sending the basic information such as PC name, user name, version, and architecture of OS. Since access to the C2 is not allowed anymore, it is impossible to check the downloaded malware.
| C&C server: https://windows-wsus-update[.]com/f1711 |
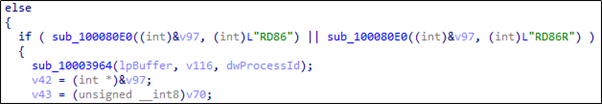
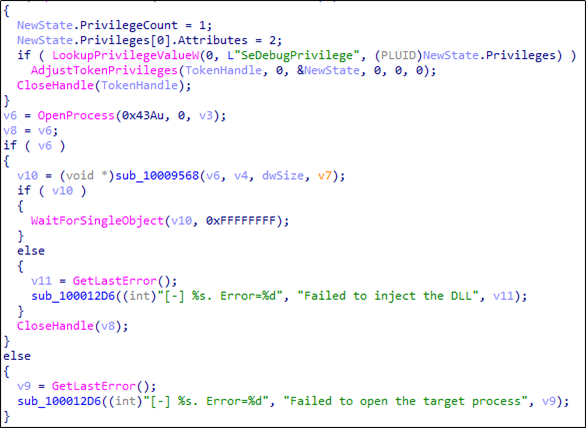
Assuming the connection to C2 is successful, there is another feature to inject the malware into other processes. This means that the malware other than the downloaded malware executed within excel.exe can also be run in other normal processes.
AhnLab is detecting malicious document files and downloaded executables distributed via spam mail as below. AhnLab is leveraging the ASD network to block the C&C network that malicious word file connects.
– VBA/Loader.S1 (2019.10.18.04)
– Trojan/Win32.Reflect.R295021 (2019.10.18.03)
– Trojan/Win64.Reflect.R295103 (2019.10.18.07)




