GandCrab Ransomware Distribution Begins in Korea
A new ransomware named GandCrab is also being distributed in Korea. The ransomware infects PC when user visits a website vulnerable due to exploit kit. Ever since its first discovery, GandCrab has been distributed incessantly across the cyber sphere.
Once PC is infected by GandCrab ransomware, file extension is changed to .GDCB and GDCB-DECRYPT.txt is created.
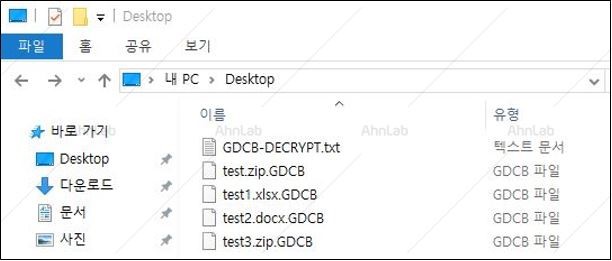
Figure 1. Extension change due to the ransomware
When GandCrab ransomware is executed, it copies itself as ‘%appdata%\Microsoft\[Randomstr{6}].exe’ adds to registry so it can remain in PC and secure its persistence for execution.
| File creation path | %appdata%\Microsoft\[Randomstr{6}].exe | |
| Registry | HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
Afterward, it checks if a certain process is running and if so, it terminates that process.
| Process termination target |
| msftesql.exe sqlagent.exe sqlbrowser.exe sqlservr.exe sqlwriter.exe oracle.exe ocssd.exe dbsnmp.exe synctime.exe mydesktopqos.exe agntsvc.exeisqlplussvc.exe xfssvccon.exe mydesktopservice.exe ocautoupds.exe agntsvc.exeagntsvc.exe agntsvc.exeencsvc.exe firefoxconfig.exe tbirdconfig.exe ocomm.exe mysqld.exe mysqld-nt.exe mysqld-opt.exe dbeng50.exe sqbcoreservice.exe excel.exe infopath.exe msaccess.exe mspub.exe onenote.exe outlook.exe powerpnt.exe steam.exe thebat.exe thebat64.exe thunderbird.exe visio.exe winword.exe wordpad.exe |
The ransomware also collects and transfers user information by C2 connection. It checks the list of running process among collected user information and sends the list in case AV software is in use. The list of processes that are checked is as below.
| List of anti-malware that are checked if in use |
| AVP.EXE ekrn.exe avgnt.exe ashDisp.exe NortonAntiBot.exe Mcshield.exe avengine.exe cmdagent.exe smc.exe persfw.exe pccpfw.exe fsguiexe.exe cfp.exe msmpeng.exe |
Other than that, the malware also sends IP, PC_USER, PC_NAME, PC_GROUP, Language, OS version, OS bit, Identifier, and Storage Device information to C2 server.
| C2 domain |
| no****ra***m.bit em***o*t.bit ga****ab.bit |
Next, it proceeds with encryption. The targets are:
| Encryption target extensions (456 total) |
| .1cd, .3dm, .3ds, .3fr, .3g2, .3gp, .3pr, .7z, .7zip, .aac, .ab4, .abd, .acc, .accdb, .accde, .accdr, .accdt, .ach, .acr, .act, .adb, .adp, .ads, .agdl, .ai, .aiff, .ait, .al, .aoi, .apj, .apk, .arw, .ascx, .asf, .asm, .asp, .aspx, .asset, .asx, .atb, .avi, .awg, .back, .backup, .backupdb, .bak, .bank, .bay, .bdb, .bgt, .bik, .bin, .bkp, .blend, .bmp, .bpw, .bsa, .c, .cash, .cdb, .cdf, .cdr, .cdr3, .cdr4, .cdr5, .cdr6, .cdrw, .cdx, .ce1, .ce2, .cer, .cfg, .cfn, .cgm, .cib, .class, .cls, .cmt, .config, .contact, .cpi, .cpp, .cr2, .craw, .crt, .crw, .cry, .cs, .csh, .csl, .css, .csv, .d3dbsp, .dac, .das, .dat, .db, .db_journal, .db3, .dbf, .dbx, .dc2, .dcr, .dcs, .ddd, .ddoc, .ddrw, .dds, .def, .der, .des, .design, .dgc, .dgn, .dit, .djvu, .dng, .doc, .docm, .docx, .dot, .dotm, .dotx, .drf, .drw, .dtd, .dwg, .dxb, .dxf, .dxg, .edb, .eml, .eps, .erbsql, .erf, .exf, .fdb, .ffd, .fff, .fh, .fhd, .fla, .flac, .flb, .flf, .flv, .flvv, .forge, .fpx, .fxg, .gbr, .gho, .gif, .gray, .grey, .groups, .gry, .h, .hbk, .hdd, .hpp, .html, .ibank, .ibd, .ibz, .idx, .iif, .iiq, .incpas, .indd, .info, .info_, .ini, .iwi, .jar, .java, .jnt, .jpe, .jpeg, .jpg, .js, .json, .k2p, .kc2, .kdbx, .kdc, .key, .kpdx, .kwm, .laccdb, .lbf, .lck, .ldf, .lit, .litemod, .litesql, .lock, .log, .ltx, .lua, .m, .m2ts, .m3u, .m4a, .m4p, .m4v, .ma, .mab, .mapimail, .max, .mbx, .md, .mdb, .mdc, .mdf, .mef, .mfw, .mid, .mkv, .mlb, .mmw, .mny, .money, .moneywell, .mos, .mov, .mp3, .mp4, .mpeg, .mpg, .mrw, .msf, .msg, .myd, .nd, .ndd, .ndf, .nef, .nk2, .nop, .nrw, .ns2, .ns3, .ns4, .nsd, .nsf, .nsg, .nsh, .nvram, .nwb, .nx2, .nxl, .nyf, .oab, .obj, .odb, .odc, .odf, .odg, .odm, .odp, .ods, .odt, .ogg, .oil, .omg, .one, .orf, .ost, .otg, .oth, .otp, .ots, .ott, .p12, .p7b, .p7c, .pab, .pages, .pas, .pat, .pbf, .pcd, .pct, .pdb, .pdd, .pdf, .pef, .pem, .pfx, .php, .pif, .pl, .plc, .plus_muhd, .pm!, .pm, .pmi, .pmj, .pml, .pmm, .pmo, .pmr, .pnc, .pnd, .png, .pnx, .pot, .potm, .potx, .ppam, .pps, .ppsm, .ppsx,.ppt, .pptm, .pptx, .prf, .private, .ps, .psafe3, .psd, .pspimage, .pst, .ptx, .pub, .pwm, .py, .qba, .qbb, .qbm, .qbr, .qbw, .qbx, .qby, .qcow, .qcow2, .qed, .qtb, .r3d, .raf, .rar, .rat, .raw, .rdb, .re4, .rm, .rtf, .rvt, .rw2, .rwl, .rwz, .s3db, .safe, .sas7bdat, .sav, .save, .say, .sd0, .sda, .sdb, .sdf, .sh, .sldm, .sldx, .slm, .sql, .sqlite, .sqlite3, .sqlitedb, .sqlite-shm, .sqlite-wal, .sr2, .srb, .srf, .srs, .srt, .srw, .st4, .st5, .st6, .st7, .st8, .stc, .std, .sti, .stl, .stm, .stw, .stx, .svg, .swf, .sxc, .sxd, .sxg, .sxi, .sxm, .sxw, .tax, .tbb, .tbk, .tbn, .tex, .tga, .thm, .tif, .tiff, .tlg, .tlx, .txt, .upk, .usr, .vbox, .vdi, .vhd, .vhdx, .vmdk, .vmsd, .vmx, .vmxf, .vob, .vpd, .vsd, .wab, .wad, .wallet, .war, .wav, .wb2, .wma, .wmf, .wmv, .wpd, .wps, .x11, .x3f, .xis, .xla, .xlam, .xlk, .xlm, .xlr, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xps, .xxx, .ycbcra, .yuv, .zip |
Some paths and filenames are excluded from encryption targets..
| Paths excluded from encryption target list | Files excluded from encryption target list |
| \ProgramData\ \Program Files\ \Tor Browser\ \Ransomware\ \All Users\ \Local Settings\ %ProgramFiles% %CommonProgramFiles% %windir% %LOCALAPPDATA% | desktop.ini autorun.inf ntuser.dat iconcache.db bootsect.bak boot.ini ntuser.dat.log thumbs.db GDCB-DECRYPT.txt |
After encryption is completed, it deletes Volumn Shadow Copy using wmic, vassadmin and etc to prevent restoration.
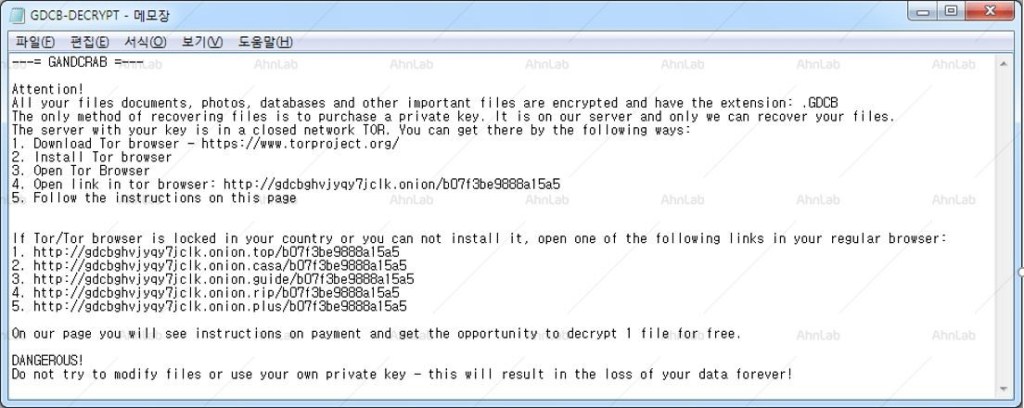
Figure 2. Ransom note
Although it is not possible to completely prevent infection or restore the system, updating Windows security patch and V3 to the latest version is required to minimize the damage.
Users should be vigilant with executing email attachments from unreliable source of accessing unidentified webpage. Also, flash security update should conducted as operators exploit flash vulnerabilities.
AhnLab V3 detects GandCrab ransomware under the following aliases:
[File Detection]
Trojan/Win32.GandCrypt(2018.02.05.07)
[Behavior Detection]
Malware/MDP.Ransom.M1171


