[Exclusive] How to Block Encryption of GandCrab v4.1.2 (Kill-Switch) – Update (v4.1.3)
On July 13, AhnLab shared the method to block encryption of GandCrab v4.1.1; Fortinet announced a similar information on July 9. However, on July 17, GandCrab 4.1.2 version was newly found as below. There was a message inserted that seemingly ridicules both security vendors.
– “#fortinet & #ahnlab, mutex is also kill-switch not only lockfile ;)”
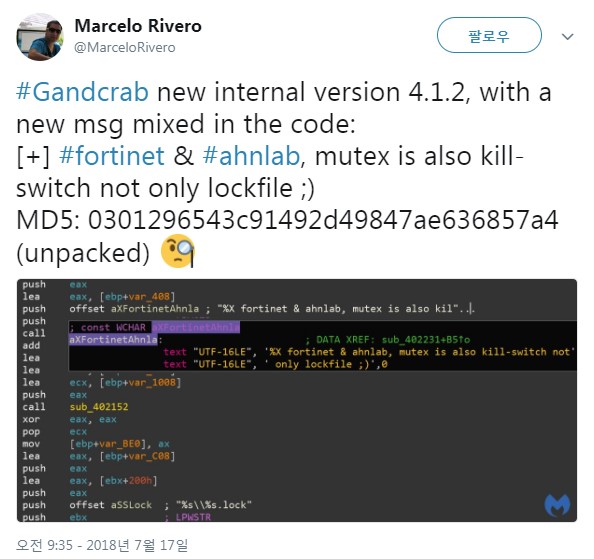
Figure 1. Twitter post on GandCrab v4.1.2 (Reference: https://twitter.com/MarceloRivero/status/1019259361259028480?s=09)
Addition of the message was not the only change in 4.1.2 version. It also complicated the algorithm of *.lock filename creation which is a key to prevent encryption and extended the length of filename from 8-byte to 20-byte. AhnLab ASEC confirmed that the changed filename creation algorithm is Custom Salsa20, a partially modified Salsa20 and developed a new encryption blocking tool based on collected information.
The Figure 2 below shows the code that creates *.lock file in the new 4.1.2 version. The red box indicates the added strings which present that lock filename is created via Salsa20 function.
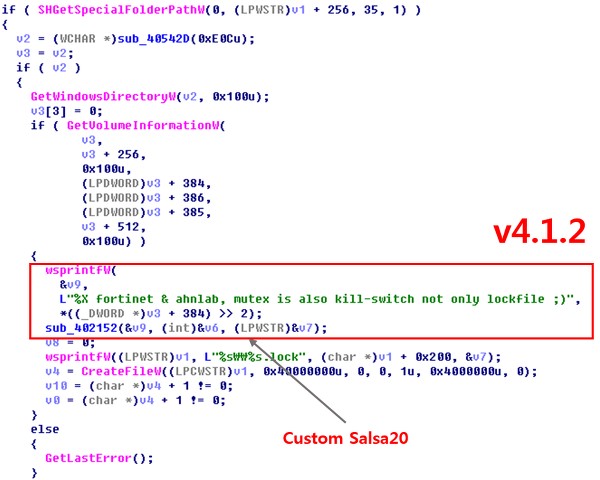
Figure 2. lock file creation of GandCrab v4.1.2
Information on Key and Vector for Salsa20 encryption are as below:
- KEY[] (hexadecimal): 01 02 03 04 05 06 07 08 09 0A 0B 0C 0D 0E 0F 10 01 02 03 04 05 06 07 08 09 0A 0B 0C 0D 0E 0F 10
- VEC[] (hexadecimal): 01 02 03 04 05 06 07 08
- Entry value: “380978EA fortinet & ahnlab, mutex is also kill-switch not only lockfile ;)” (380978EA value is information created via drive volume and is different for each user)
It is still able to kill-switch as long as the modified filename exists in a specific path. The place of creation and instruction of use for lock files are as follows:
Folder: CSIDL_COMMON_APPDATA
- Win XP: C:\Documents and Settings\All Users\Application Data
- Win 7, 8, 10: C:\ProgramData
File: 8A5BA4B9C369950A5FEC.lock (example)
Filename is created based on volume information of root drive + Custom Salsa20 algorithm
GandCrab_KillSwitch_(4.0_4.1.1_4.1.2_4.1.3).zip
How to use the tool
- Download the attached executable and right click to ‘run as administrator.’
- Check *.lock file that has been created in the folder (Common AppData).
V3 products have been detecting and responding to GandCrab v4.1.2 under the following aliases. Also, AhnLab ASEC is continuously monitoring ransomware GandCrab distributed in Korea, and V3 products are well-prepared to carry out preemptive response to new versions.
- Behavior Detection: Malware/MDP.Ransom
- File Detection: Win-Trojan/Gandcrab04.Exp (2018.07.17.00)
- MD5: f153ac5527a3e0bc3e663b8e953cc529


