Preemptive Defense Measures against Fileless Magniber Ransomware (V3 Behavior Detection)


After the distribution of Magniber recovery tools developed by AhnLab Analysis Team in 2018, Magniber has been transformed into a fileless format, disabling any kind of recovery. For successful file encryption, this fileless Magniber has evolved to bypass behavior detection and perform indiscriminate injection to unspecified processes that have privileges on infected system. Through these techniques, the subject of ransomware becomes the normal running process of the infected system. Even if the process is terminated, the ransomware is recursively executed by a different process to make blocking difficult after injection.
In case an Anti-Virus(AV) product simply detects and terminates ransomware behavior (file encryption) processes, users must reboot the system as either BSoD(Blue Screen of Death) pops up or PC may not function properly when Windows system process is terminated. The operators of Manigber have modified operation method in multiple ways such as changing the injection object to disable recovery and complicate and bypass the behavior detection. However, operators have been maintaining CVE-2018-8174 VBScript engine vulnerability since 2018, that they exploit for initial infection; it is Internet Explorer vulnerability so Chrome users are not applied.
Manigber ransomware connects users to the webpage with CVE-2018-8174 vulnerability by utilizing malicious advertising technique when users access to a vulnerable webpage. In the environment without security update, file gets encrypted only with an access to webpage as a remote code is executed.
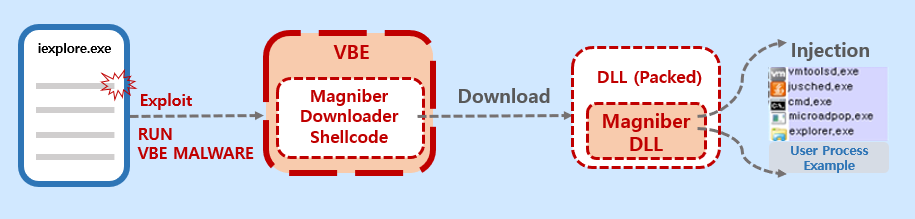
In the up to date security environment without the CVE-2018-8174 vulnerability of remote code execution, the first phase shown in Figure 1, Manigber DLL file cannot carry out file encryption as its injection will fail.
Internet Explorer Security Update Information: Link
However, AhnLab Smart Defense(ASD) receives hundreds of daily reports on vulnerability execution logs within systems without security patch. AhnLab Analysis Team analyzed these vulnerabilities to conduct behavior detection. As a result, current V3 products detect CVE-2018-8174 vulnerability based on its behavior and have behavior detection feature(Malware/MDP.Exploit.M2214) which terminates Internet Explorer performing malicious behavior.
However, AhnLab’s ASD (AhnLab Smart Defence) system is receiving hundreds of daily reports every day on vulnerability execution logs within systems with no security patches. The AhnLab analysis team has analyzed these vulnerabilities and has done operations to detect vulnerabilities based on their behaviors. Based on the analysis, the current V3 product can now detect CVE-2018-8174 vulnerability with the behavior detection, and also has a feature that terminates the Internet Explorer if malicious behavior is detected (Malware/MDP.Exploit.M2214).
If the block screen appears while visiting a web page and Internet Explorer gets closed, users should recognize it as an insecure webpage and refrain themselves from revisiting.
Behavior Detection
Malware/MDP.Exploit.M2214