Increase of Malware Signed with Valid Digital Certificate

Code signing is a process of signing a file with digital signature based on the personal information of the applicant to enhance trust and secure integrity. The file creator receives digital certificate via Certificate Authority(CA) and signs the file using the certificate.
Since the code signed file is certified by the authorities, it is easy to avoid download validation process in web browser and detection of Anti-Virus(AV) product when executed. Thus, operators sometimes distribute a malicious file with adding the information of valid digital signature. Such attempt, for example Stuxnet in 2010 has been present from the past.
It is notable that among malicious files actively spread in Korea in the first half of this year, many of them were signed with a valid digital certificate and it is still in progress. Also, the ASUS issue that information stealer malware was detected in the file signed with certificate from the company, was heated.
Users may ask ‘if it is possible to only receive digital certificate from trusted certificate authority after they fully check user identity, how can operators develop malware signed with valid certificate?’ It is more likely to be one of three types based on the certificate issuance scenario.
- Stealing an issued certificate of other company
- Disguising as a normal company or using paper company name to directly receive certificate from CA
- Purchasing ‘#2 certificate’ from black market
Majority of malicious files confirmed in 2019 were signed with valid certificate via method 2 and 3 above. It is less but there were cases with method 1. Now, we will explore the type and feature of malicious file as well as certificate information.
1. Directly receiving certificate – Remote backdoor ‘Ammyy’ and ransomware ‘Clop’ that attacks system connected to AD service domain.
If we count some vigorous malware in Korea, two of them will be the remote backdoor “Ammyy” distributed to corporates and ransomware Clop that Ammyy installs. Backdoor file has been developed using source code of Ammyy’s remote-control program that is available online. Then, it remotely access the system by planting it in the target PC. The malicious file that attacker attempts to ultimately run in controlled system is the ransomware Clop.
During the distribution phase, operators check whether the target PC user is in Active Directory(AD) service architecture that uses a domain controller. If so, they proceed to the next step, which is spreading. This means that attackers target companies that normally form domain with users and operate the system.
While tracking ransomware Clop, AhnLab confirmed that key PE files that form three phases were code signed: ▲file that downloads backdoor file ▲Ammyy backdoor file ▲ransomware Clop file. The digital certificate used for signing has not changed its information per file feature, but various certificates were applied to each file. It implies that same operator creates and distributes files, from downloader to ransomware.
The following shows the certificate information(certificate authority and issued target) that were found to be used for the attack above. All of them received that certificate with the name of existing small companies in UK. Considering the fact that most of these companies are not related to software production or certificate issuance, their business information are suspected to be either stolen or traded illegally.
| COMODO RSA Code Signing CA |
| ALCOHOL LTD ALLO’ LTD AWAY PARTNERS LIMITED VAL TRADEMARK TWO LIMITED VERY TELE LIMITED |
| Sectigo RSA Code Signing CA |
| ALISA L LIMITED WINTER AEROSPACE LTD THE COMPANY OF WORDS LTD DELUX LTD COME AWAY FILMS LTD MAN TURBO (UK) LIMITED ANGEL AID LTD DE&GO LTD MARIA’S PEGASEAL LTD D.E.PLANT LIMITED STYLE DESIGN & BUILD LTD |
| Sectigo RSA Code Signing CA |
| DVERI FADO, TOV MEGAPOLIS SERVICES LTD |
| thawte SHA256 Code Signing CA |
| PRIMA ASTRA LTD JIN CONSULTANCY LIMITED FLOWER DELI LTD VIEW DESIGN LIMITED BURGER AND BEATS LIMITED LIMIT FORCE LIMITED ANG APPCONN LIMITED REBROSE LEISURE LIMITED 3AN LIMITED A&D DOMUS LIMITED BEAR ADAMS CONSULTING LIMITED SLOW COOKED VENTURES LTD ICE ACTIVATION LIMITED PIZZAZZ LTD |
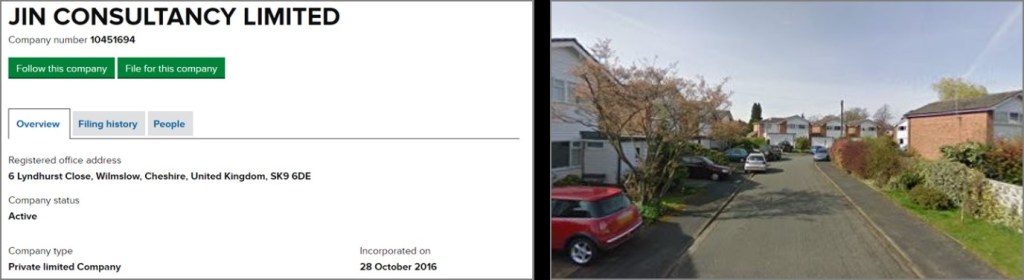
Figure 1 – Business information and view of company that is known to receive certificate (source: UK Companies House information, Google Maps)
2. Stealing certificate – a malware signed with ASUS certificate – Operation ‘ShadowHammer’
On March 2019, Kaspersky Lab reported that there is a malicious file signed with valid certificate of ASUS, a renowned global hardware manufacturer. The malware was known to be produced a year before. The certificate was leaked as the software update server was compromised, and according to Kaspersky Lab, over 57,000 users downloaded the malicious file and approximately 1 million users could be affected.
AhnLab checked the information of the certificate and thoroughly analyzed files that were signed with this certificate. The result revealed that some of the files signed with valid certificate were developed as a file that can perform not only a feature of normal ASUS program but also that of malware. The added code connected to asushotfix.com, a malware distribution website disguised as ASUS website, and downloaded another file. Also, a variant of ShadowHammer malicious file was discovered in both expired ASUS certificate and others.
This case of existing certificate being stolen and abused to develop malware has few differences [1] scenario. First, there is a far heavier damage as targeting a huge supplier like ASUS. Also, since there are files distributed with normal code signing, it is difficult to immediately determine whether it is malicious. As for the attacker, there is no cost for acquiring the certificate. However, persistence of the attack tends to be weaker as there is difficulty in stealing certificate and the issuer can immediately discard the certificate as soon as the file is turned out to be malicious.
The following shows the information of certificates(certificate authority and issued target) that were found to be used for the ShadowHammer attack. Other than ASUS, certificates of gaming companies in Korea and Sigapore were also stolen to create and distribute malware. Currently, the certificate of ASUS has been disposed but those from Singapore and Korea are still valid.
| DigiCert SHA2 Assured ID Code Signing CA |
| ASUSTeK Computer Inc. (Serial Number: 55A7AA5F0E52BA4D78C145811C830107) ASUSTeK Computer Inc. (Serial Number: 0ff067d801f7daeeae842e9fe5f610ea) |
| VeriSign Class 3 Code Signing 2010 CA |
| Garena Online Pte Ltd (Serial Number: 4881c660940900f949fe4d60fa7f937e) |
| COMODO RSA Code Signing CA |
| ZEPETTO Co. (Serial Number: 00fdf2837dac12b7bb30ad058f999ecf00) |
Since the file signed with a valid digital signature is already acknowledged with its credibility, it is difficult for AV product to detect it as malicious just with its behavior. Even if a certificate is actually leaked or stolen, it is hard to judge its authenticity. Thus, malware analyst is required to have a deeper look into the files even with valid certificates.
AhnLab established a separate database storing digital certificate information of file and lowers trust level of certificate when detecting the malicious file with valid signature. If certain malicious files are collected repeatedly, AhnLab detect entire files as malware based on their certificate information: issue target, serial no., and etc. Moreover, if a certificate has been stolen due to hacking or other incident, AhnLab refers to the time stamp of file creation to clearly separate those files from normal files. Below is the AhnLab’s detection information on the cases discussed in this post. The detection information has been continuously updated reflecting the result of monitoring and analysis.
– Win-Trojan/Suspig.Exp
– Win-Trojan/ALLColour.Exp
– Win-Trojan/Logi.Exp
– Win-Trojan/Craydoor.Exp
– Win-Trojan/ShadowHammer.Exp




