BlueCrab: The Successor of GandCrab with Different Execution Method Depending on Use of V3Lite


A newly emerged BlueCrab ransomware is distributed in various ways, similar to GandCrab. Its distribution methods include phishing email with a malicious document attached and phishing utility download page. AhnLab ASEC has been monitoring the distribution code of Javascript disguising as a utility program.
When Javascript file(.js) downloaded from the phishing utility download page is executed, BlueCrab ransomware is run at the same time.
The current execution flow of Javascript is shown in Figure 1. BlueCrab ransomware is injected into Powershell.exe and performs encryption.
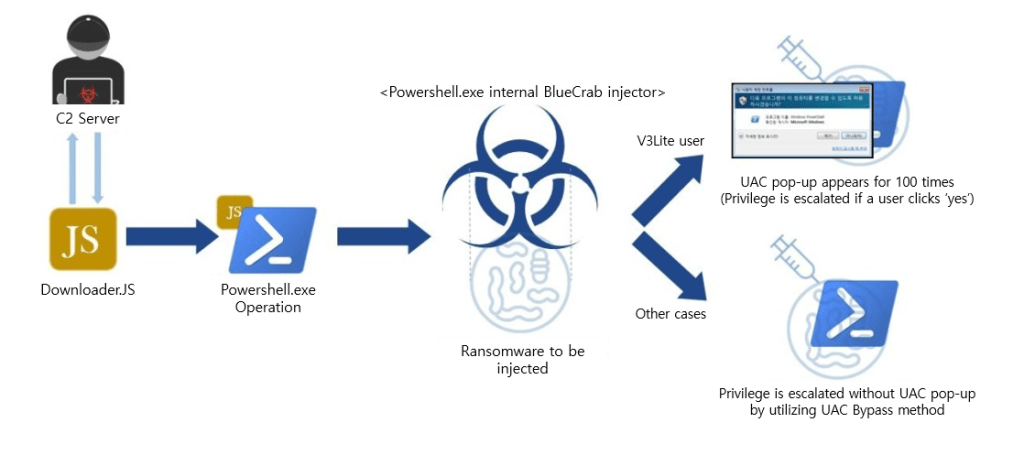
Figure 1. Execution flow of Javascript distributing BlueCrab
One of the special characteristics of BlueCrab is that it uses a unique execution method against V3Lite users. V3Lite is blocking BlueCrab ransomware’s specific UAC(user account control) bypass method in advance based on behavioral analysis. In response to this, operators ceased to use UAC bypass method against V3Lite users and instead, began prompting users to click ‘Yes’ and run ransomware by setting a notification pop-up to repeat itself for hundred times. In the environment without V3Lite, it carries out its bypass method without users’ knowledge.
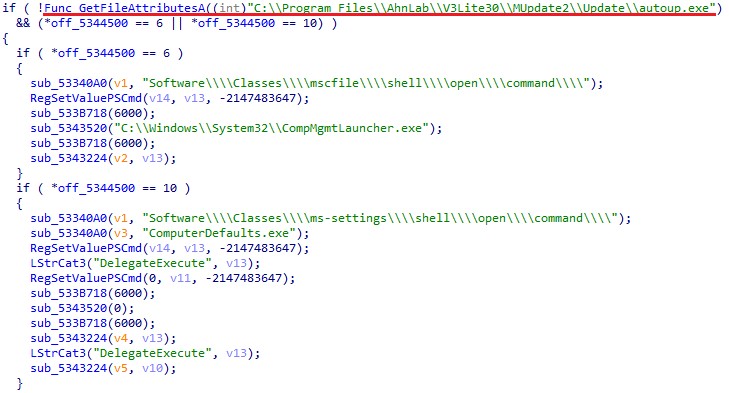
Figure 2. Certain UAC bypass string checks the existence of V3Lite
Figure 2 exhibits a certain UAC bypass code. The code underlined in red checks whether V3Lite exists and if it does, the code is not run.
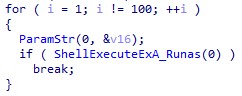
Figure 3. ‘for statement’ triggering UAC notification pop-up to repeat for 100 times

Figure 4. ShellExecuteExA_Rusas function
Figure 3 shows a part of code that repeats cented. Figure 4 is ShellExecueExA function that causes UAC notification pop-up to appear.
If it is run with this particular method, UAC notification pop-up appears, and the pop-up repeats itself for hundred times until user clicks ‘Yes’.
The script for BlueCrab ransomware distribution with the method above is detected and blocked by the behavior detection under the following aliases:
[File Detection]
– JS/Gandcrab.S10 (2019.05.10.00)
[Behavior Detection]
– Malware/MDP.Behavior.M1997
– Malware/MDP.Behavior.M2084
– Malware/MDP.Behavior.M2194




