March 2026 Security Issues in the Korean & Global Financial Sector

Content.
a number of malware samples including phishing, web shell, droppers, backdoor malware, downloaders, Infostealer, and CoinMiner targeting the financial sector have been distributed.
we observed a number of cases where Korean disguised attachment names and HTML/JS execution methods were utilized to propagate phishing.
account compromise campaigns through the Telegram API were confirmed, with approximately 4% of the compromised accounts coming from the financial sector.
The AnySign4PC vulnerability was exploited in a watering hole attack by the Lazarus group, resulting in remote code execution, and multiple watering hole distribution sites were found to be continuously used.
on the dark web and forums, cases of selling and claiming to disclose large databases of Korean & Global financial companies such as NR Capital were reported.
a number of cases of ransomware groups (Apt73, PayoutsKing, WorldLeaks, etc.) breaching the financial sector and disclosing DLS were confirmed, raising the risk of double extortion and large-scale data leakage.
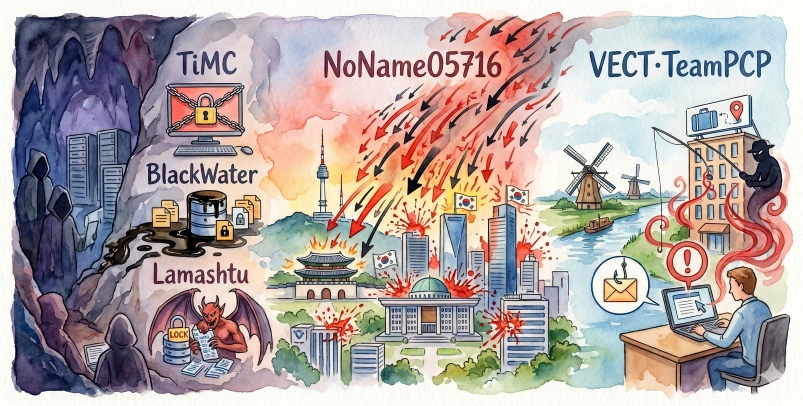
pro-political DDoS attacks by hacktivists reduced the availability of some banking websites and claimed customer data breaches.
Purpose and Scope.
this report comprehensively summarizes cases of malware distribution, account compromise, watering hole/vulnerability exploitation, dark web data distribution, and ransomware/DDoS breaches in the financial sector collected during the month of March 2026.
the research includes cases of Korean & Global financial institutions, dark web and forum posts, and security vendor monitoring data.
Key statistics.
the top 10 malware for the month included Web Shell, Phishing, Backdoor, Dropper, Downloader, Infostealer, and CoinMiner.
a large number of attachment names were identified in Korean, and HTML/JS executable files were frequently used as phishing funnels.
internal estimates reported that the Telegram breach affected approximately 4% of accounts in the financial sector.
dark web postings confirmed large breach and sale claims, including NR Capital (approximately 2TB claimed), Ameriprise (200GB claimed), Nu Colombia (30k documents claimed), and Agrobanco (250k claimed).
in the ransomware attack cases, it was reported that some companies’ data was released to the DLS or was exfiltrated in full.
Bottom line.
attacks targeting the financial sector are multilayered, from initial penetration through phishing to vulnerability-based watering hole RCE, account exfiltration, data theft and distribution, ransomware double extortion, and DDoS.
this leads to the need for financial institutions to strengthen logs, patching, backups, and access control, as well as industry-wide intelligence sharing.
continuous monitoring and prompt disclosure of information and law enforcement cooperation in the event of an incident are important to mitigate damage in the financial sector.