XLoader Info-stealer Distributed Using MS Equation Editor Vulnerability (CVE-2017-11882)

AhnLab Security Intelligence Center (ASEC) publishes the information of phishing emails to AhnLab TIP monthly under the title “Trends Report on Phishing Emails.” There are various keywords/topics disguised as phishing, and this blog will cover cases where emails disguised as emails for checking purchases and order confirmations are used to distribute the XLoader info-stealer. The email body asks to check if the purchase order is correct and contact back with the attached DOCX file to be executed.
During the process of executing the attached malicious document, it was confirmed that the environment still uses the MS Equation Editor vulnerability (CVE-2017-11882). It is likely to be exposed to attacks in a vulnerable environment. After the MS Equation Editor vulnerability, the XLoader info-stealer built by HorusProtector will operate in memory.
HorusProtector is a commercial protector that distributes various malware. The builder is distributed free of charge in the attacker’s chat room, and the method is to purchase a license key from the attacker for authentication. When building, it has the feature of specifying the process to be injected and injecting the final malware to be executed. The latest version at the time of analysis was confirmed to be v0.4.2.
Figure 1 Phishing Email Body

Figure 2 HorusProtector Builder Image
In the past, the initial file was distributed as a VBE single file. However, in this case, the initial file starts as a DOCX document file, and the DOCX document file contains an RTF document that exploits the Equation Editor vulnerability.

[Fig. 3] RTF File Embedded in a DOCX Document
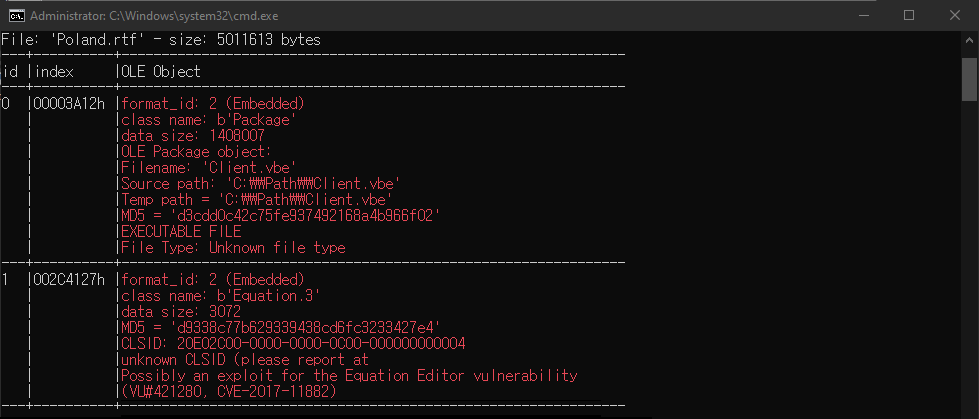
[Figure 4] Client.vbe and Vulnerability Code Included in RTF
Upon execution of the DOCX file, the internal RTF document is run via External connection. This RTF document creates the “Client.vbe” file in a temporary folder and utilizes the formula editor vulnerability to run the “cmd.exe /C cscript %tmp%\Client.vbe” command. In the past, the VBE file did not contain the final malware and was downloaded and executed from C2. The file size was also around 10KB. However, as seen in the case, HorusProtector currently being distributed has the VBE file containing the final malware and the size is approximately 1.34MB.

[Figure 5] (Left) Decoded VBE Code of the Previous Version (Right) Decoded VBE Code of the Current Version
When Client.vbe is executed, it creates a key with a 15-character random name under “Computer\HKEY_CURRENT_USER\SOFTWARE\” and generates a subkey named “donn“. The data saved in each registry key is as follows.
※ In the sample of the main text, a key named “gSngToQWoKopCel” is created.
- gSngToQWoKopCel : Name of the process to be injected, BASE64-encoded DLL loader file, PowerShell script to run the loader
- donn : BASE64-encoded Malware executed in the end

[Figure 6] (Top) Registry Key Values Related to Execution, (Bottom) Malware Data Finally Executed
Lastly, the PowerShell script creates “RegAsm.exe” as a child process, and the DLL loader file decodes and executes the final malware. The final malware executed is identified as the infostealer XLoader.
HorusProtector has been distributing various malwares since 2024. Initially, it distributed VBE single files, but currently, it is distributed through phishing emails that include MS Office documents utilizing the Equation Editor vulnerability. The fact that malwares exploiting past vulnerabilities are still being distributed implies that there are still many users in vulnerable environments. Users must use Office products without the Equation Editor or prevent malware infection through security updates. When opening files attached to emails from unknown sources, extra caution is required.