Threat Trend Report on Kimsuky – April 2023

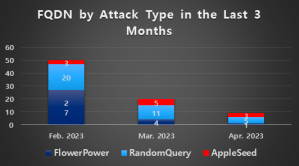
The Kimsuky group’s activities in April 2023 showed a decline in comparison to their activities in March, falling under half the number of the previous month. Korean domains were used for FlowerPower like before without major changes, and the RandomQuery type also remained the same. Lastly, we confirmed that the domain responsible for distributing AppleSeed has been spreading the Google Chrome Remote Desktop setup script. Also, the dropper file and AppleSeed file used different argument values, which is a shift from the usual method of using identical ones.
-
- FlowerPower
- RandomQuery
- AppleSeed
- Found Using Chrome Remote Desktop
- AppleSeed Using Two Argument Values



