ASEC Weekly Malware Statistics (November 1st, 2021 – November 7th, 2021)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known malware. This post will list weekly statistics collected from November 1st, 2021 (Monday) to November 7th, 2021 (Sunday).
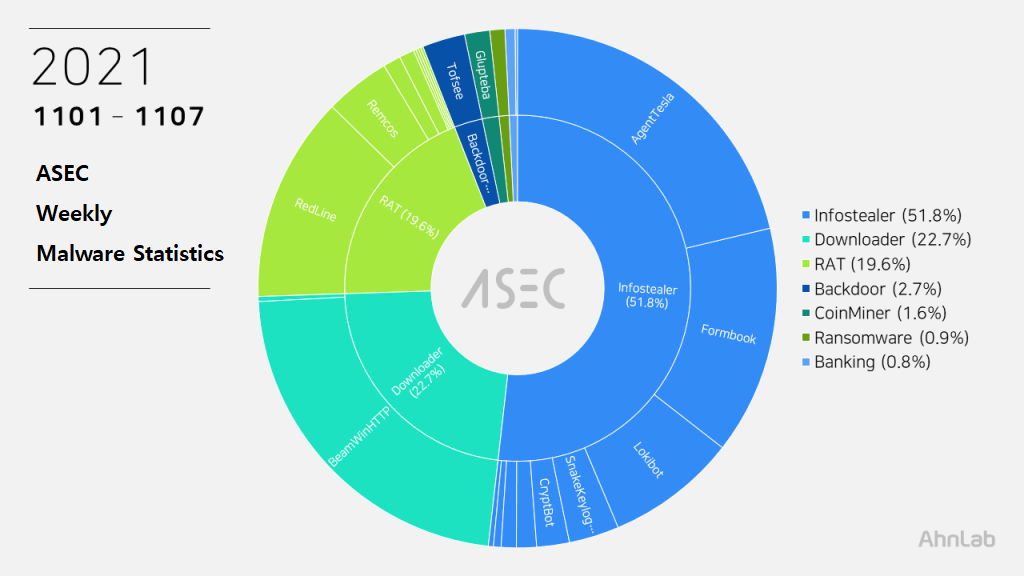
For the main category, info-stealer ranked top with 51.8%, followed by Downloader with 22.7%, RAT (Remote Administration Tool) malware with 19.6%, Backdoor malware with 2.7%, and CoinMiner with 1.6%.
Top 1 – BeamWinHTTP
BeamWinHTTP is a downloader malware that has taken first place once again with 22.4%. BeamWinHTTP is distributed via malware disguised as PUP installer. When it is executed, it installs PUP malware Garbage Cleaner, and can download and install additional malware at the same time.
The confirmed C&C server URL is as follows.
- gcl-gb[.]biz
Top 2 – AgentTesla
AgentTesla was ranked second place with 21.3%. It is an info-stealer malware that leaks user credentials saved in web browsers, emails, and FTP clients.
Recently collected samples use the following email servers and user accounts when leaking the collected information.
- mail.medicare-equipment[.]com
sender : medicare@madicare-equipment[.]com
receiver : ghostxxz@yandex[.]com
user : medicare@madicare-equipment[.]com
pw : AllThe****777 - mail.emulines[.]biz
sender : maxi.rosario@emulines[.]biz
receiver : maxi.rosario@emulines[.]biz
user : maxi.rosario@emulines[.]biz
pw : oaOwC****6YR - mail.sancaheidelberg.co[.]za
sender : sandy@sancaheidelberg.co[.]za
receiver : sandy@sancaheidelberg.co[.]za
user : sandy@sancaheidelberg.co[.]za
pw : Syste****00
As most are distributed through spam emails disguised as invoices, shipment documents, and purchase orders, the file names contain such words shown above (Invoice, Shipment, P.O. – Purchase Order). Some samples have extensions disguised as document files such as pdf and xlsx or Auto CAD blueprint files such as dwg.
- 17869 [order].exe
- 1MV. BRAVE SAILOR (V.1801) – AGENT NOMINATION (Bunkering Only).exe
- 2021193746437. XLS.exe
- BALANCE Confirmation xxls.exe
- Bank details.exe
- COPIA DE PAGO TT_pdf_________________________________________.exe
- DHL9142591441.PDF.exe
- Quotation.exe
- sale order.exe
- SHIP-INVOICE_21DG096-097. XLS.exe
- SNE.Order_OrisOxin Co..exe
- SNE-20210123.exe
Top 3 – Formbook
Formbook is an info-stealer malware that ranked third place with 14.2%.
Like other info-stealer malware, it is mainly distributed through spam emails. The distributed file names are close to each other.
- Product-Catalog23.exe
- commercialJ-80-PM-MRQ-4025-6901.exe
- DOC.exe
- Drawings HQ30-DM140.exe
- Ekli PO No. 162223 (Mazak Corporation)pdf.exe
- inquiry.exe Purchase Order- 10,000 MT.exe
- Quotation.exe
- quote s1.GM.220.21.exe
- RFQref0948321.PDF.exe
- ScanPMT.exe
- SURRENDED BL Draft-Sea-Waybill-FLXT-1304583.exe
As Formbook is injected in a normal process that is in the directory of explorer.exe and system32, the malicious behaviors are performed by the normal process. Besides user credentials in the web browser, the malware can steal various information through keylogging, clipboard grabbing, and web browser form grabbing. Below is the list of confirmed C&C server URLs of Formbook.
- hxxp://www.bainrix[.]com/ahdu/
- hxxp://www.banceout3[.]com/sywu/
- hxxp://www.mefacin[.]online/gt4l/
- hxxp://www.norllix[.]com/gab8/
- hxxp://www.seo-clicks7[.]com/cnp0/
- hxxp://www.wecuxs[.]com/ntfs/
- hxxp://www.wecuxs[.]/vocn/
Top 4 – RedLine
RedLine malware ranked fourth place with 12.8%, making it into the Top 5 again. The malware steals various information such as web browsers, FTP clients, cryptocurrency wallets, and PC settings. It can also download additional malware by receiving commands from the C&C server.
The following are the confirmed C&C server domains for RedLine:
- piatulusher[.]xyz
- 135.181.129[.]119:4805
- 91.121.67[.]60:23325
Top 5 – Lokibot
Lokibot malware ranked fifth place with 8.1%. It is an info-stealer malware that leaks information about programs such as web browsers, email clients, and FTP clients.
Being a malware that is distributed through spam emails, it shares similar file names with other malware spam emails.
- Gen2**ve_T800-3.exe
- Se**ong Ref No. MQ-3018 & MQ-3019.exe
- AWB 8532266141 .jpg.exe
- PO_445622380.exe
- Quotation Request..exe
- SO5040230.exe
- PO 211102-02B.exe
- RFQ_SG951021-22.exe
- PO 211101-002A.exe
- Offer_sheet_Quotation.exe
As shown below, most Lokibot C&C server URLs tend to end in fre.php.
- hxxp://203.159.80[.]151/king/fre.php
- hxxp://23.254.225[.]235/oga/fre.php
- hxxp://23.254.225[.]235/uyaka/fre.php
- hxxp://23.254.225[.]235/wj/fre.php
- hxxp://arinzeproducts[.]xyz/five/fre.php
- hxxp://bobreplace[.]xyz/five/fre.php
- hxxp://navijunks[.]ml/chores/fre.php
- hxxp://peakledz[.]xyz//five/fre.php
- hxxp://secure01-redirect[.]net/ga17/fre.php
- hxxp://secure01-redirect[.]net/ga24/fre.php
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.



