ASEC Weekly Malware Statistics (August 9th, 2021 – August 15th, 2021)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known threats. This post will list weekly statistics collected from August 9th, 2021 (Monday) to August 15th, 2021 (Sunday).
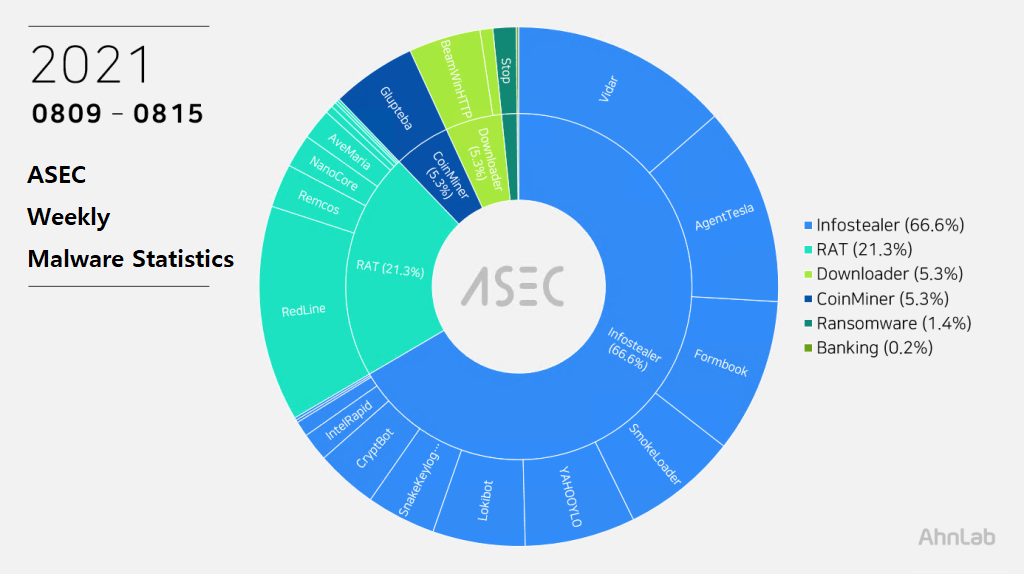
For the main category, Infostealer ranked top with 66.6%, followed by RAT (Remote Administration Tool) malware with 21.3%, Downloader and CoinMiner with 5.3%, Ransomware with 1.4%, and banking malware with 1.3%.
Top 1 – Vidar
Vidar was ranked first place with 13.6%. It is an infostealer / downloader malware. Vidar not only steals information from web browser, FTP, cryptocurrency wallet address, and screenshot, but also downloads additional malware.
As shown in the blogs below, spam mails are being sent periodically to Korean users, and its characteristic is that it exists with other ransomware within the compressed file attached to the spam mail.
Recently, certain game platforms are being abused to spread ransomware.
The following has explanations on Vidar’s info-leaking feature.
C&C URLs that were used during the period are the following.
- hxxp://116.203.127[.]162/517
- hxxp://kckark[.]xyz/main.php
- hxxp://23.88.49[.]119/706
- hxxp://176.123.2[.]239/517
Top 2 – RedLine
RedLine ranked second with 13.4%. The threat steals various information from web browser, FTP client, cryptocurrency wallet, and PC settings. It can also download additional malware by receiving commands from the C&C server.
The following are the confirmed C&C server domains for RedLine:
- hxxp://sytareliar[.]xyz/
- hxxp://yabelesatg[.]xyz/
- hxxp://sandedean[.]xyz/
- hxxp://iryarahara[.]xyz/
- hxxp://ssissmongo[.]xyz/
Top 3 – AgentTesla
AgentTesla was ranked third place with 12.3%. It is an Infostealer that leaks user information saved in web browsers, e-mails, and FTP clients.
Recently collected samples use the following mail servers and user accounts when leaking the collected information.
- smtp.gmail[.]com (173.194.76[.]108)
sender : aalahajirazak.ibrahim@gmail[.]com
receiver : aalahajirazak.ibrahim@gmail[.]com
user : aalahajirazak.ibrahim@gmail[.]com
pw : sontcehkw***wuqj - serv-10708.handsonwebhosting[.]com (107.152.108[.]114)
sender : emma@multillantaszl[.]com
receiver : emma@multillantaszl[.]com
user : emma@multillantaszl[.]com
pw : icui4***@@ - mail.karanex[.]com (185.8.128[.]141)
sender : sales@karanex[.]com
receiver : sales@karanex[.]com
user : sales@karanex[.]com
pw : roz%***3
As most are distributed through spam mails disguised as invoices, shipment documents, and purchase orders, the file names contain such words shown above (Invoice, Shipment, P.O. – Purchase Order). Some samples have extensions disguised as document files such as pdf and xlsx or Auto CAD blueprint files such as dwg.
- Reconfirm payment invoice #Order396541.exe
- 07.08.0260.exe
- WTR BFV 156 -Rev4.exe
- Supply Damages&TT_pay swift.exe
- NT1-20-7262-AGA-PurchaseOrder.exe
- COMPROBANTE.PDF.bat
- Banamex__Pago_07768843.pdf.exe
- Pulley Specification.exe
- sample.exe
Top 4 – Formbook
Formbook is an Infostealer ranked fourth place with 8.2%.
Like other Infostealers, it is mainly distributed through spam mails. The distributed file names are close to each other.
- quote.exe
- 2021_08_10_scan00744.exe
- Apol_Order_100821.exe
- SOA invoice.exe
- Order-H21811.exe
- CATALOG & ORDER LIST.Pdf.exe
- PO2-1874.exe
As Formbook is injected in a normal process that is in the directory of explorer.exe and system32, the malicious behaviors are performed by the normal process. Besides user account information in the web browser, the threat can steal various information through keylogging, clipboard grabbing, and web browser form grabbing. Below is the list of confirmed C&C server URLs of Formbook.
- hxxp://www.atlerz[.]com/glgd/
- hxxp://www.psm-gen[.]com/cg53/
- hxxp://www.atlerz[.]com/glgd/
- hxxp://www.racevc[.]com/ur5u/
- hxxp://www.afcerd[.]com/chad/
- hxxp://www.baincot[.]com/nins/
- hxxp://www.solevux[.]com/fw3d/
- hxxp://www.nieght[.]com/i6sj/
- hxxp://www.abrosnm3[.]com/rqe8/
- hxxp://www.blinbins[.]com/q4kr/
- hxxp://www.bulukx[.]com/ixwn/
Top 5 – Smoke Loader
Smoke Loader is an infostealer / downloader that ranked fifth place with 7.2%. For analysis report related to Smoke Loader, refer to the ASEC Report below.
[PDF] ASEC REPORT vol.101_Smoke Loader Learns New Tricks
The confirmed C&C server URLs are as follows.
- conceitosseg[.]com/upload/
- integrasidata[.]com/upload/
- ozentekstil[.]com/upload/
- finbelportal[.]com/upload/
- telanganadigital[.]com/upload/
- khaleelahmed[.]com/upload/
- twvickiassociation[.]com/upload/
- www20833[.]com/upload/
- cocinasintonterias[.]com/upload/
- masaofukunaga[.]com/upload/
- gnckids[.]com/upload/
- aucmoney[.]com/upload/
- thegymmum[.]com/upload/
- atvcampingtrips[.]com/upload/
- kuapakualaman[.]com/upload/
- renatazarazua[.]com/upload/
- nasufmutlu[.]com/upload/
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.


