ASEC Weekly Malware Statistics (July 26th, 2021 – August 1st, 2021)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to major malware. This post will list weekly statistics collected from July 26th, 2021 (Monday) to August 1st, 2021 (Sunday).
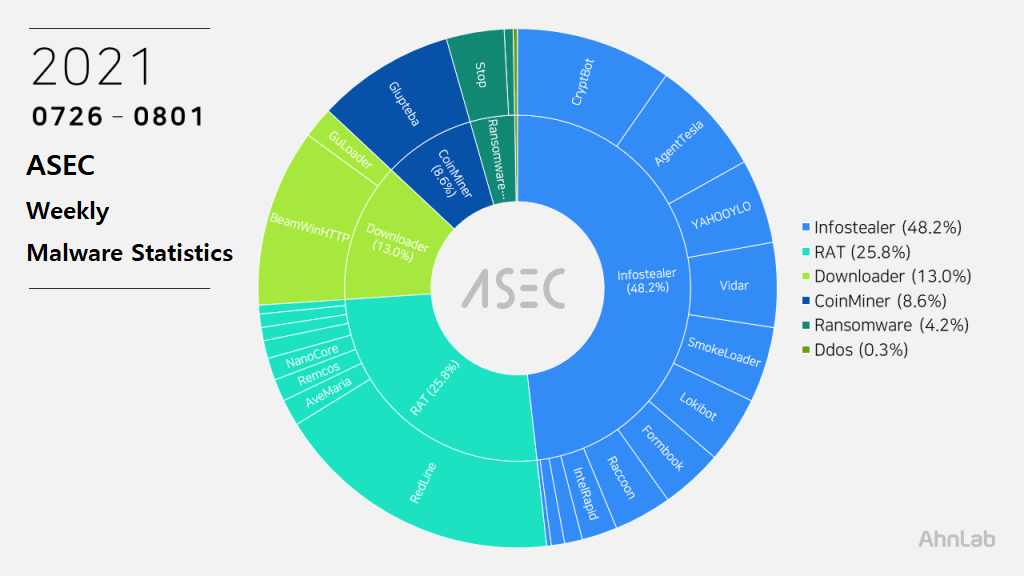
For the main category, Infostealer ranked top with 48.2%, followed by RAT (Remote Administration Tool) malware with 25.8%, downloader with 13.0%, CoinMiner with 8.6%, ransomware with 4.2%, and Ddos with 0.3%.
Top 1 – RedLine
RedLine malware has taken first place once again with 18.0%. The malware steals various information such as web browser, FTP client, cryptocurrency wallet, and PC settings. It can also download additional malware by receiving commands from the C&C server.
The following are the confirmed C&C server domains for RedLine:
- hxxps://all-brain-company[.]xyz/
- hxxp://yarinefatt[.]xyz
- hxxp://zertypelil[.]xyz
- hxxp://ivaloribar[.]xyz/
- hxxp://naxunarium[.]xyz/
- hxxp://salkefard[.]xyz/
- hxxp://verecalina[.]xyz/
Top 2 – BeamWinHTTP
BeamWinHTTP is a downloader malware that ranked second with 11.1%. BeamWinHTTP is distributed via malware disguised as PUP installer. When it is executed, it installs PUP malware Garbage Cleaner, and can download and install additional malware at the same time.
The confirmed C&C server URL is as follows.
- hxxp:///gc-prtnrs[.]top/decision.php
Top 3 – CryptBot
This week, CryptBot ranked third with 9.7%. CryptBot is mainly distributed through malicious sites disguised as software download pages. Upon entering a certain keyword in the search engine, these malicious websites appear on the top page. When the PC is infected, it attempts to steal various user info and download additional malware.
The following are the C&C server URLs and additional malware download URLs of CryptBot.
- C&C1: wymkjd37[.]top/index.php
C&C2: moriue03[.]top/index.php
Download URL: hofxuo04[.]top/download.php?file=lv.exe - C&C1: smanik53[.]top/index.php
C&C2: morzie05[.]top/index.php
Download URL: gurqfo07[.]top/download.php?file=lv.exe - C&C1: smaoez65[.]top/index.php
C&C2: mortuh06[.]top/index.php
Download URL: gurswi09[.]top/download.php?file=lv.exe - C&C1: smauxw61[.]top/index.php
C&C2: mortuh06[.]top/index.php
Download URL: gurswi09[.]top/download.php?file=lv.exe
The distributed filenames are as follows.
- main_setup_x86x64.exe
- p3-signed.exe
- Setup.exe
- setup_installer.exe
- setup_x86_x64_install.exe
- setuplauncher_v2.exe
- setuplauncher_v3.exe
- x86_x64_setup.exe
Top 4 – Glupteba
Glupteba is a malware developed with Golang, taking fourth place with 8.6%. It downloads various additional modules and has various features, but it is actually a CoinMiner malware that installs XMR (Monero) CoinMiner.
When Glupteba is executed, it acquires the system permission by going through UAC Bypass and using TrustedInstaller’s permission. It then disguises as a normal process named C:Windowsrsscsrss.exe and remains in the system. Afterward, Glupteba downloads additional modules such as rootkit drivers for a purpose of concealing processes and files, and ultimately installs Eternal Blue package to spread through XMR CoinMiner and SMB vulnerabilities.
So far, most of the confirmed Glupteba samples are being downloaded and distributed via PUPs. Even though Glupteba is being distributed via PUP, it takes the appearance of a MalPe packer (it is mentioned in the previous blog post).
Malware strains that take the appearance of a MalPe packer can be distributed via Exploit Kit. There are also cases of Vidar malware and PUP where the malware disguised as a normal program was distributed.
[Additional Module Download URL]
- hxxps://spolaect[.]info
[C&C Server URL]
- hxxps://ninhaine[.]com
- hxxps://2makestorage[.]com
- hxxps://nisdably[.]com
Top 5 – AgentTesla
AgentTesla was ranked fifth place with 7.2%. It is an info-stealer malware that leaks user information saved in web browsers, e-mails, and FTP clients.
Recently collected samples use the following mail servers and user accounts when leaking the collected information.
- serv-10708.handsonwebhosting[.]com
sender: droid@multillantaszl[.]com
receiver: droid@multillantaszl[.]com
user: droid@multillantaszl[.]com
pw: icui****@@ - smtp.saisianket-tech[.]com
sender: akibapen@saisianket-tech[.]com
receiver: akibapen@saisianket-tech[.]com
user: akibapen@saisianket-tech[.]com
pw: oluwag****123 - us2.smtp.mailhostbox[.]com
sender: paola.micheli@copangroup[.]xyz
receiver: paola.micheli@copangroup[.]xyz
user: paola.micheli@copangroup[.]xyz
pw: gibs****990
As most are distributed through spam mails disguised as invoices, shipment documents, and purchase orders, the file names contain such words shown above (Invoice, Shipment, P.O. – Purchase Order). Some samples have extensions disguised as document files such as pdf and xlsx or Auto CAD blueprint files such as dwg.
- XP010-61.exe
- scan0012330.PDF_________________________________________.exe
- 委外订单-启绩物料6-1-2.exe
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.


