A New Attempt to Disable Korean Anti-malware Software (GandCrab v5.0.4)
As monitoring the GandCrab distribution script, AhnLab ASEC recently spotted a new method to disable Korean anti-malware software. While the previous version tried to delete the software via executing ‘Uninst.exe’ as Figure 1 below, recently discovered distribution script leverages a new method to terminate V3 software.

Figure 1. Code related to uninstall V3Lite (GandCrab v5.0.3)
Also, there was a change in its operation method. In previous version, GandCrab ransomware executable was created and executed by Javascript file(*.JS) but the recent one is operated in fileless format via powershell and the encryption is conducted by PowerShell.exe. Furthermore, it operates after a 15-minute delay (Sleep() function) if widely used Korean anti-malware software is running.
A distributed *.js file is obfuscated as shown in Figure 2, and is designed to run PowerShell.exe internally.

Figure 2. Javascript file containing malicious dll
It runs “랜덤명.log” (translated: random_name.log) file via command below.
“C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe”
-ExecutionPolicy Bypass -Command “IEX (([System.IO.File]::ReadAllText(‘C:\Users\(User_ID)\Desktop\(랜덤명).log’)).Replace(‘?’,”));”
랜덤명.log(random_name.log) file is encoded to Base64 like Figure 3 below. Figure 4 is a decoded powershell script.

Figure 3. Encoded powershell script (랜덤명.log or random_name.log)
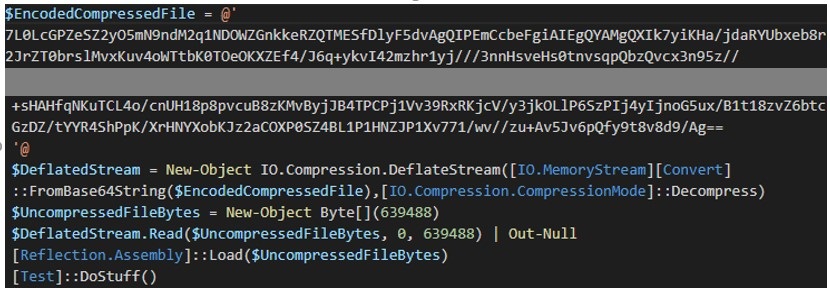
Figure 4. Decoded powershell script
Ultimately, the Figure 4 script is run, and this powershell script runs Delphi code(Figure 6.) in memory.
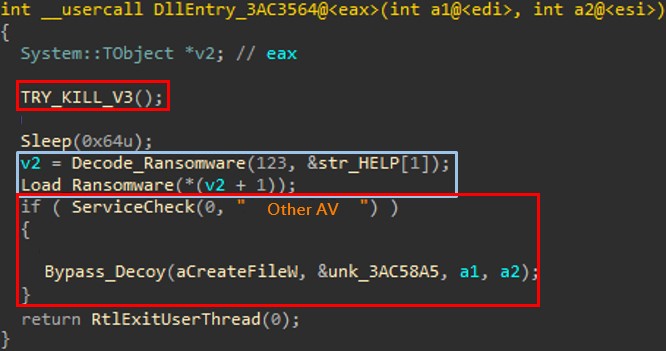
Figure 5. A part of internal Delphi code
In Figure 5, the code in red box is a function to disable two Korean anti-malware software, and the code in the blue box commands the same infection behavior with an existing GandCrab ransomware. The execution order is as below
(1) Check if V3 service is active (“V3 Service”)
(2) Sleep() for 15 minutes
(3) Attempt to terminate V3 service
(4) Run DLL ransomware
(5) Check if other Korean anti-malware service is active (“ALYac_RTSrv”)
(6) Attempt to bypass Decoy folder of other anti-malware software
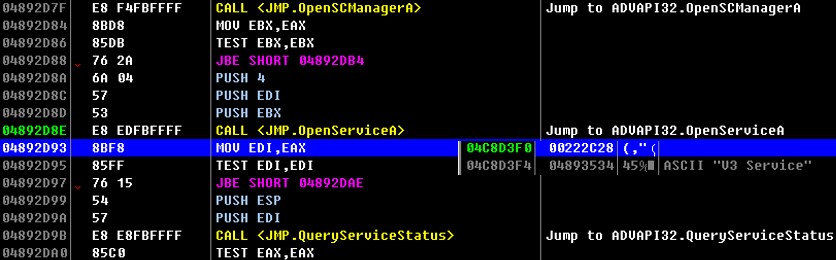
Figure 6. Internal DLL code
As previous GandCrab has become unable to delete anti-malware software due to application of CAPTCHA code, it began terminating the anti-malware instead. As shown in Figure 7, it searches for the service named “V3 Service” to check whether it is running, and if so, the malware waits (Sleep() function) for 15 minutes and attempts to terminate the service.
Other local security vendors also leverage the decoy method which creates a randomly named decoy folder in a certain directory of drive and detects the encryption of document in a folder as ransomware behavior.
To bypass this decoy detection of anti-malware providers, the new GandCrab refers to the list of strings used as folder name for each drive. If a certain string from the list (Table 2.) is discovered, it bypasses the decoy and files inside the folder. For example, if a decoy folder named “!@GNNh” is created in C Drive, the path will be as Table 1. below.
| Decoy folder directory: C:\!@GNNh\ GandCrab bypass string: C:\!@GNNh\ |
In the example above, since the first letter of decoy’s path is a special character (!), GandCrab attempted to bypass it with the technique that utilizes 9 particular strings. Bypassed strings are as Table 2. below.
| Number | Filtered Strings |
| 1 | :\! |
| 2 | :\@ |
| 3 | :\# |
| 4 | :\$ |
| 5 | :\% |
| 6 | :\^ |
| 7 | :\& |
| 8 | :\= |
| 9 | :\- |
AhnLab’s V3 detects and blocks the samples below under the following aliases.
File Detection (related to disabling V3)
– Win-Trojan/AVKill.Exp
Behavior Detection (ransomware behavior detection)
– Malware/MDP.Ransom.M1996
Behavior Detection (privilege escalation behavior detection)
– Malware/MDP.Behavior.M2084


