Dynamic Analysis on Bypass Method of GandCrab v5.2
In a widely distributed ransomware GandCrab, the code is inserted to bypass a dynamic analysis equipment. Thus, Gandcrab can bypass the detection by getting terminated in dynamic analysis equipment without proper operation or delaying the analysis process.
Below are the codes to bypass the dynamic analysis equipment:
- Anti-Sandbox via SetErrorMode function
- Delay of time using SetTimer function
1. Anti-Sandbox via SetErrorMode function
First, the packer that GandCrab mostly utilizes contains the code that uses SetErrorMode function to bypass Cuckoo Sandbox as seen in Figure 1.

Figure 1. Anti-Sandbox via SetErrorMode
SetErrorMode function sets ProcessDefaultHardErrorMode and returns the previously set ErrorMode. ErrorMode sets how the system will cope with the error that has occurred. Below is the flow of operation in normal circumstances.
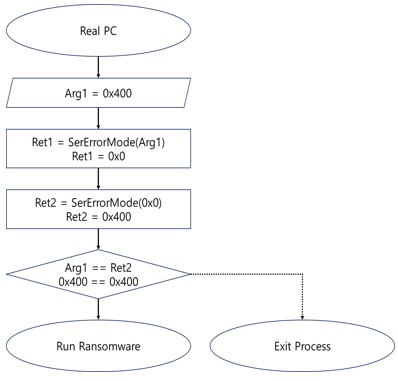
Figure 2. Run flow in normal circumstances
(1) SetErrorMode(0x400)
– Set ErrorMode to 0x400 and return previously-set ErrorMode value.
(2) SetErrorMode(0x0)
– Set ErrorMode to 0x0 and return parameter 0x400 of (1) that was previously set.
(3) CMP, JE, ExitProcess
– Check if 0x400, a value returned as a result of (2) is same as 0x400, used as a parameter for (1) and then branch, which is same with executing ransomware.
The problem here is SEM_NOALIGNMENTFAULTEXCEPT (0x0004) ErrorMode utilized in Cuckoo Sandbox and others
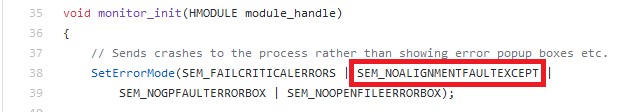
Figure 3. ErrorMode utilized in Cuckoo Sandbox (Reference: https://github.com/cuckoosandbox/monitor/blob/master/bin/monitor.c)
The value automatically edits Memory alignment fault. One of its property is that once it is set, it ignores an attempt to reset the value. After ErrorMode is set to this value, flow of code shown in Figure 1 gets differed with the flow in Figure 2 and becomes what is shown below in Figure 4.
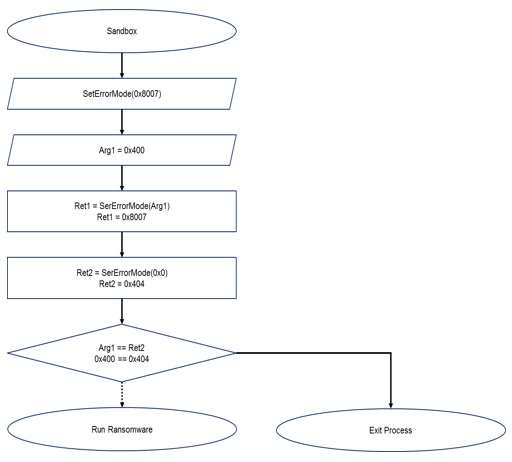
Figure 4. Run flow in an environment where SEM_NOALIGNMENTFAULTEXCEPT is set
(1) SetErrorMode(0x400)
– There is an attempt to set ErrorMode to 0x400. However, attempt to reset the previously set SEM_NOALIGNMENTFAULTEXCEPT is ignored and 0x404 is set instead. 0x8007 is returned due to how the code is set, shown in Figure 3.
(2) SetErrorMode(0x0)
– There is an attempt to set ErrorMode to 0x0. However, attempt to reset the previously set SEM_NOALIGNMENTFAULTEXCEPT is ignored and 0x4 is set instead. 0x404 is returned as a result of (1).
(3) CMP, JE, ExitProcess
– Since the returned value 0x404, a result of (2) is different from 0x400 which was used as a parameter value of (1), the process is terminated.
As such, there is a technique using SetErrorMode function to detect Sandbox and terminate process so that dynamic analysis equipment cannot deliver the precise result.
2. Delay of time using SetTimer function
Next, we will be explaining how GandCrab’s major encryption methods are implemented with a delay to certain extent by using SetTimer function. GandCrab used Windows procedure and message as the method of setting and running SetTimer.
It creates a Windows procedure with class name ‘AnaLab_sucks’ and makes it perform SetTimer feature. At this point, GandCrab sets a timer of 1.337 seconds.
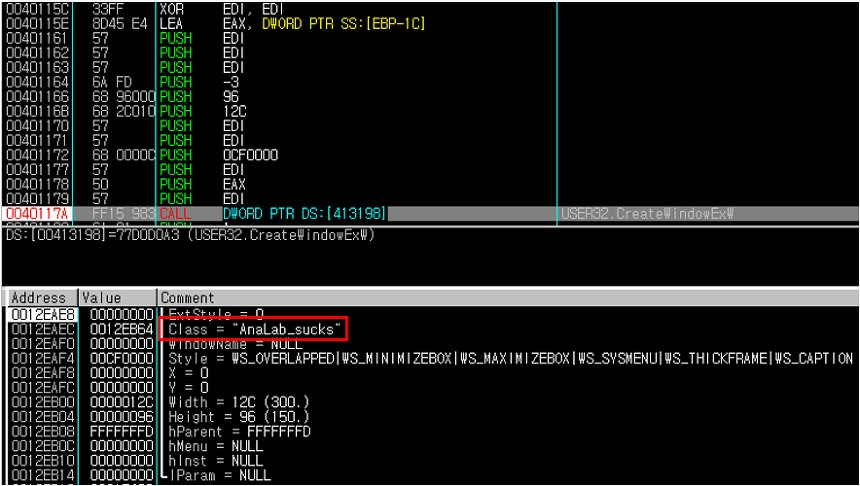
Figure 5. Creating Windows procedure via CreateWindowExW
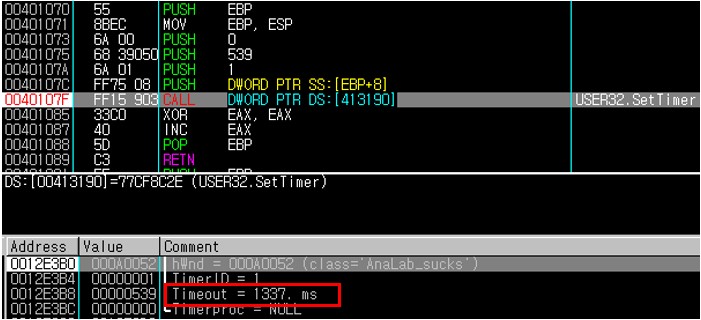
Figure 6. Setting SetTimer to 1337ms
It also uses DispatchMessage function to call the procedure called ‘AnaLab_sucks.’ As above, since ‘AnaLab_sucks’ was set to run SetTimer, a delay of 1.337 seconds takes place whenever ‘AnaLab_sucks’ is called via DispatchMessage.
A recently distributed GandCrab implements DispatchMessage for twenty times, lengthening the delay to 26.74 seconds.
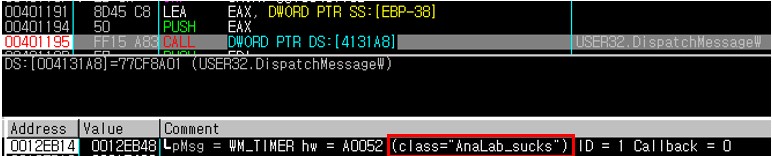
Figure 7. Calling ‘AnaLab_sucks’ by DispatchMessageW procedure
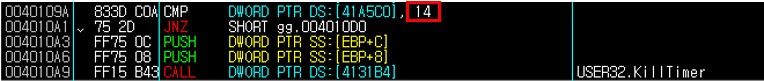
Figure 8. End of delay with KillTimer after checking the occurrence of 20(0x14)
This intentional delay complicates the detection from real time monitoring by a dynamic analysis equipment. AhnLab has been conducting continuous monitoring and analysis to properly detect new files and prevent them from bypassing.
V3 detects GandCrab under the following aliases:
- File Detection: Trojan/Win32.GandCrab
- Behavior Detection: Malware/MDP.Ransom.M1711


