Ransom & Dark Web Issues Week 2, February 2026
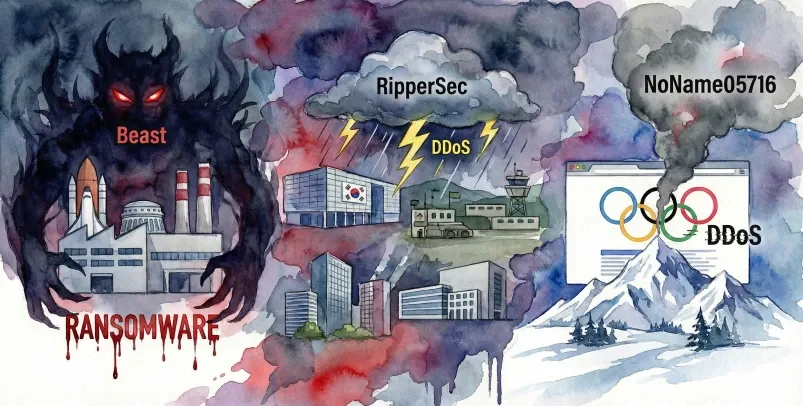
ASEC Blog publishes Ransom & Dark Web Issues Week 2, February 2026 Beast, Ransomware Attack Targeting a South Korean Aerospace Component Manufacturer RipperSec, Claims of DDoS Attacks Targeting South Korean Exhibition Centers, Military Training Grounds, Associations, and Defense-related Companies [1], [2], [3], [4] NoName05716, Claims
Ransom & Dark Web Issues Week 1, Fabruary 2026
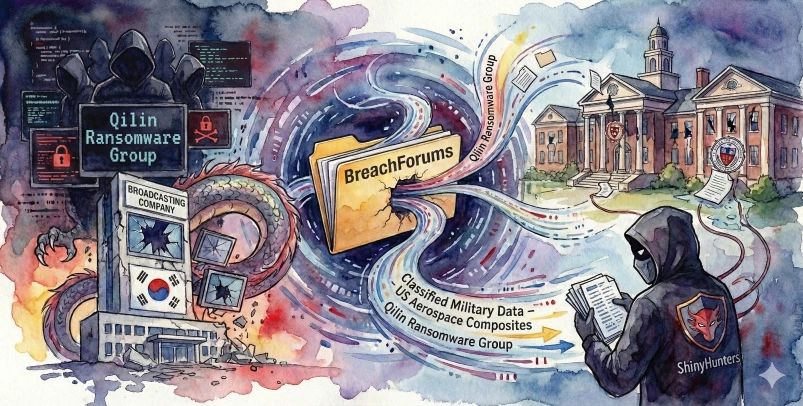
ASEC Blog publishes Ransom & Dark Web Issues Week 1, Fabruary 2026 Qilin Targets South Korean Public Broadcaster with Ransomware Confidential Military Data from U.S. Aerospace Composites Manufacturer Sold on BreachForums ShinyHunters Leaks Data from Two Prestigious U.S. Private Universities
Ransom & Dark Web Issues Week 4, January 2026
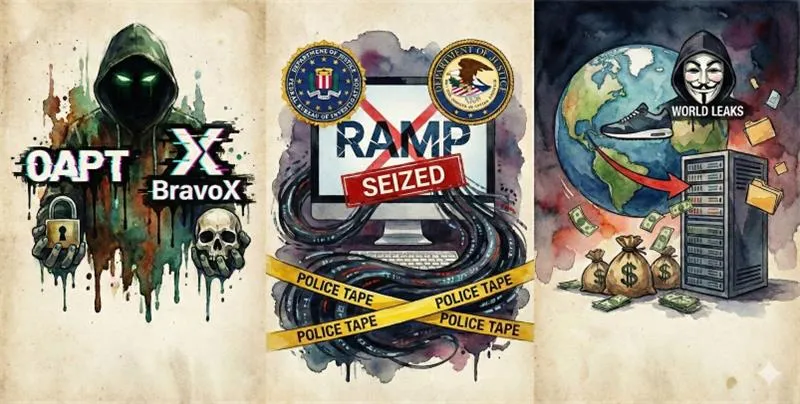
ASEC Blog publishes Ransom & Dark Web Issues Week 4, January 2026 New Ransomware Group 0APT and BravoX Identified [1], [2] RAMP Cybercrime Forum Domains Seized by FBI and DOJ World Leaks Targets U.S. Global Sportswear Company in Ransomware Attack
Ransom & Dark Web Issues Week 3, January 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 3, January 2026 Qilin Ransomware Targets Korean Specialist in Semiconductor/Display Components & Surface Treatment U.S. DOJ: Access Broker “r1z” Pleads Guilty Qilin Ransomware Targets Vietnam’s National Airlines
Ransom & Dark Web Issues Week 2, January 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 2, January 2026 Qilin ransomware attack against a Korean automotive smart factory automation equipment manufacturer Customer data of a Korean cloud and hosting service provider shared on DarkForums Everest ransomware attack against a major Japanese automobile
Ransom & Dark Web Issues Week 1, January 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 1, January 2026 South Korean University Website Data Shared on DarkForums Saudi Arabian Employment Platform Data Sold on BreachForums and DarkForums Recent Security Activity Involving the Ransomware Group Vect
Statistics Report on Malware Targeting Windows Database Servers in Q4 2025
AhnLab SEcurity intelligence Center (ASEC) utilizes the AhnLab Smart Defense (ASD) infrastructure to respond to and categorize attacks targeting MS-SQL and MySQL servers installed on Windows operating systems. This post covers the damage status of MS-SQL and MySQL servers that have become attack targets and statistics on attacks against these
In-Depth Analysis Report on LockBit 5.0: Operation and Countermeasures
Since its first appearance in September 2019, LockBit has been known as one of the most notorious and active Ransomware-as-a-Service (RaaS) groups worldwide. LockBit operates on the RaaS model and is characterized by sophisticated encryption technology and automated propagation capabilities. Initial access is typically gained through vulnerability exploits, brute force
Ransom & Dark Web Issues Week 2, December 2025
ASEC Blog publishes Ransom & Dark Web Issues Weeks 2, December 2025. Source code from a South Korean camping reservation platform sold on DarkForums LockBit 5.0 targets 25 companies worldwide with ransomware attack Agencies from USA and Europe escalate pressure on pro-Russian hacktivists
Threats Behind the Mask of Gentlemen Ransomware
Gentlemen is a new ransomware group first identified around August 2025. The group operates a double extortion model that involves breaching corporate networks, exfiltrating data, encrypting the data, and then using the encrypted data to extort victims. During the breach, the group employs typical tactics seen in advanced ransomware groups,