Ransom & Dark Web Issues Week 1, April 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 1, April 2026 Ransomware group NetRunner attack against the Indian subsidiary of a South Korean auto parts manufacturer Ransomware group Everest attack against a major Japanese automaker ShinyHunters claims of source code and internal data leak
Ransom & Dark Web Issues Week 4, March 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 4, March 2026 Japanese Automaker Suffers Personal Data Breach via Unauthorized External Access INC Ransom Targets South Korean Steel Manufacturer in Ransomware Attack LeakBase Forum Administrator Arrested in Russia
Attack Targeting MS‑SQL Servers to Deploy the ICE Cloud Scanner (Larva-26002)
AhnLab SEcurity intelligence Center (ASEC) has confirmed that the Larva-26002 threat actor continues to target improperly managed MS-SQL servers in 2026. The Larva-26002 threat actor has distributed Trigona and Mimic ransomware in the past, and has since seized control of infected systems and installed scanners. The latest confirmed attack utilizes
Ransom & Dark Web Issues Week 3, March 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 3, March 2026 New Threat Actor CipherForce Claims Cyberattack on South Korean Job Portal New Threat Actor Loki Emerges, Leaks US Citizens’ Personal Data Cybercrime Forum LeakBase Shut Down Again by Russian Authorities
Ransom & Dark Web Issues Week 2, March 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 2, March 2026 Qilin ransomware attack targeting a well-known dermatology clinic in South Korea and the Korean branch of a global advertising company [1], [2] KillSec and Everest ransomware attacks targeting a South Korean exhibition management platform
Ransom & Dark Web Issues Week 1, March 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 1, March 2026 Morpheus Launches Ransomware Attack on South Korean Plating Company Ailock Resumes Activity and Republishes Previous Ransomware Victims Pro-Iranian and Pro-Islamist Hacktivist Groups Launch Cyber Attacks on Middle Eastern and Pro-Western Targets [1], [2]
복호화 가능성이 존재하는 Green Blood 랜섬웨어 분석
Green Blood 랜섬웨어 그룹은 2026년 1월부터 활동이 확인된 신규 랜섬웨어 그룹으로, Golang 기반의 랜섬웨어 페이로드를 운영하는 것이 특징이다. 이들은 남아시아와 아프리카, 남미 일부 국가를 중심으로 공격을 전개하고 있으며, 다른 랜섬웨어 그룹과 마찬가지로 감염된 시스템의 파일을 암호화하고 피해 기업의 민감 정보를 탈취하는 이중 갈취 방식을 사용한다. 또한 몸값이 지불되지 않을 경우
Ransom & Dark Web Issues Week 4, Fabruary 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 4, Fabruary 2026 Source code of a South Korean accounting automation solution provider sold on BreachForums Beast ransomware attack targeting a South Korean pharmaceutical company and battery safety component manufacturer [1], [2] Atomsilo resumes activity and
Ransom & Dark Web Issues Week 3, Fabruary 2026
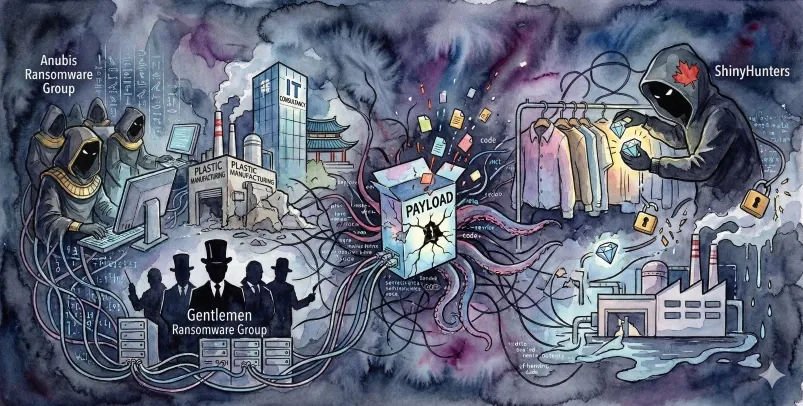
ASEC Blog publishes Ransom & Dark Web Issues Week 3, Fabruary 2026 Anubis and The Gentlemen launch ransomware attacks targeting a South Korean plastics manufacturer and an IT consulting company [1], [2] Emergence of the new ransomware group Payload ShinyHunters claims data breach involving a
Ransom & Dark Web Issues Week 2, February 2026
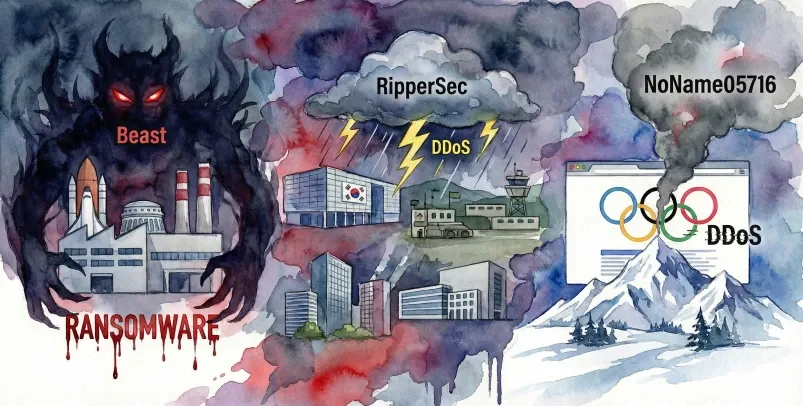
ASEC Blog publishes Ransom & Dark Web Issues Week 2, February 2026 Beast, Ransomware Attack Targeting a South Korean Aerospace Component Manufacturer RipperSec, Claims of DDoS Attacks Targeting South Korean Exhibition Centers, Military Training Grounds, Associations, and Defense-related Companies [1], [2], [3], [4] NoName05716, Claims