Ransom & Dark Web Issues Week 4, March 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 4, March 2026 Japanese Automaker Suffers Personal Data Breach via Unauthorized External Access INC Ransom Targets South Korean Steel Manufacturer in Ransomware Attack LeakBase Forum Administrator Arrested in Russia
Ransom & Dark Web Issues Week 2, March 2026
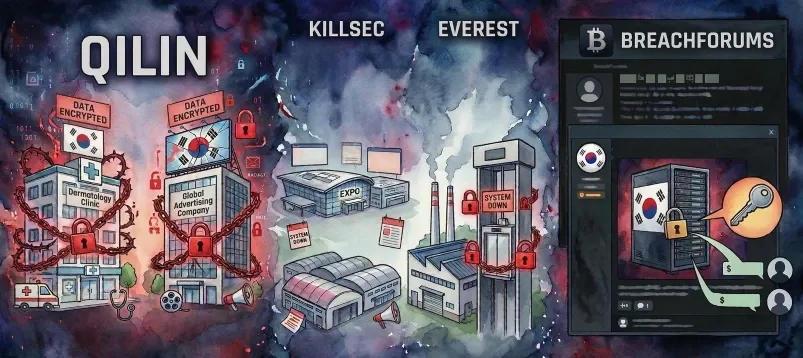
ASEC Blog publishes Ransom & Dark Web Issues Week 2, March 2026 Qilin ransomware attack targeting a well-known dermatology clinic in South Korea and the Korean branch of a global advertising company [1], [2] KillSec and Everest ransomware attacks targeting a South Korean exhibition management platform
Ransom & Dark Web Issues Week 1, March 2026
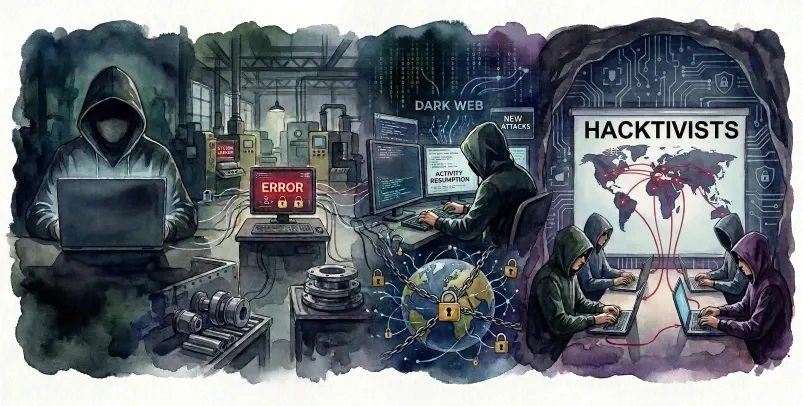
ASEC Blog publishes Ransom & Dark Web Issues Week 1, March 2026 Morpheus Launches Ransomware Attack on South Korean Plating Company Ailock Resumes Activity and Republishes Previous Ransomware Victims Pro-Iranian and Pro-Islamist Hacktivist Groups Launch Cyber Attacks on Middle Eastern and Pro-Western Targets [1], [2]
Ransom & Dark Web Issues Week 4, Fabruary 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 4, Fabruary 2026 Source code of a South Korean accounting automation solution provider sold on BreachForums Beast ransomware attack targeting a South Korean pharmaceutical company and battery safety component manufacturer [1], [2] Atomsilo resumes activity and
Ransom & Dark Web Issues Week 2, February 2026
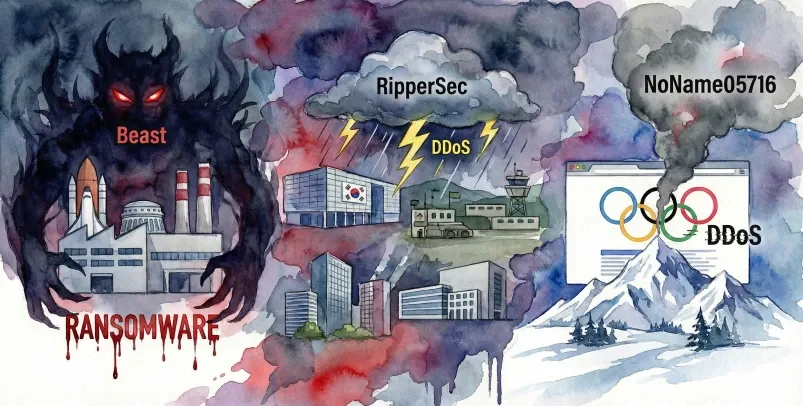
ASEC Blog publishes Ransom & Dark Web Issues Week 2, February 2026 Beast, Ransomware Attack Targeting a South Korean Aerospace Component Manufacturer RipperSec, Claims of DDoS Attacks Targeting South Korean Exhibition Centers, Military Training Grounds, Associations, and Defense-related Companies [1], [2], [3], [4] NoName05716, Claims
Ransom & Dark Web Issues Week 1, Fabruary 2026
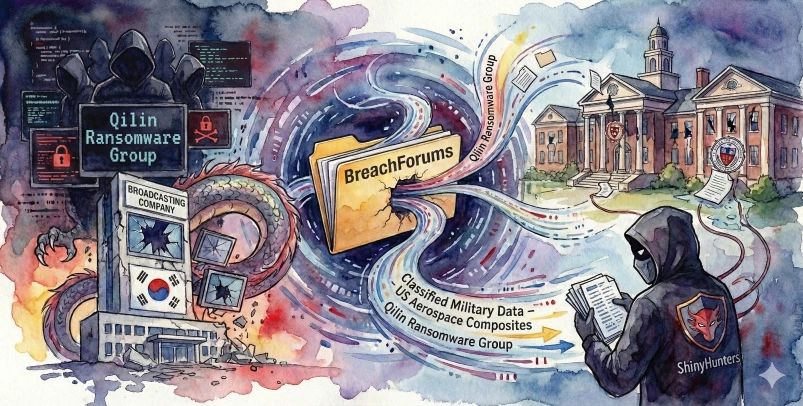
ASEC Blog publishes Ransom & Dark Web Issues Week 1, Fabruary 2026 Qilin Targets South Korean Public Broadcaster with Ransomware Confidential Military Data from U.S. Aerospace Composites Manufacturer Sold on BreachForums ShinyHunters Leaks Data from Two Prestigious U.S. Private Universities
Ransom & Dark Web Issues Week 3, January 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 3, January 2026 Qilin Ransomware Targets Korean Specialist in Semiconductor/Display Components & Surface Treatment U.S. DOJ: Access Broker “r1z” Pleads Guilty Qilin Ransomware Targets Vietnam’s National Airlines
Ransom & Dark Web Issues Week 1, January 2026
ASEC Blog publishes Ransom & Dark Web Issues Week 1, January 2026 South Korean University Website Data Shared on DarkForums Saudi Arabian Employment Platform Data Sold on BreachForums and DarkForums Recent Security Activity Involving the Ransomware Group Vect
Ransom & Dark Web Issues Week 2, December 2025
ASEC Blog publishes Ransom & Dark Web Issues Weeks 2, December 2025. Source code from a South Korean camping reservation platform sold on DarkForums LockBit 5.0 targets 25 companies worldwide with ransomware attack Agencies from USA and Europe escalate pressure on pro-Russian hacktivists
Ransom & Dark Web Issues Week 1, December 2025
ASEC Blog publishes Ransom & Dark Web Issues Week 1, December 2025. Source code from a South Korean AI solution company, shared on DarkForums Nova (RALord) targets a South Korean industrial equipment manufacturer with ransomware attack PLAY targets a South Korean auto parts manufacturer with