February 2026 Security Issues Related to the Korean & Global Financial Sector

This report comprehensively covers actual cyber threats and related security issues targeting financial institutions in South Korea and abroad.
It includes analysis of malware and phishing cases distributed targeting the financial sector, presents the Top 10 major malware targeting the financial sector, and provides statistics on the industry sectors of South Korean accounts leaked via Telegram. It also details cases of phishing emails distributed targeting the financial sector.
Furthermore, it analyzes major financial threats and cases originating from the dark web. It investigates threats and actual cases of credit card data leaks, as well as threats and incidents of database leaks at financial institutions. It also analyzes ransomware intrusion threats targeting the financial sector, damage cases resulting from infections, and various cyberattack threats against financial institutions along with actual damage cases.
[Statistical Data Summary]
-
Malware distribution statistics targeting the financial sector

-
Statistics on the industrial sectors of accounts in South Korea leaked via Telegram

[Summary of Key Deep and Dark Web Issues Related to the Financial Sector]
- Case of Damage from the Sale of Access Credentials
Affected company: Chinese Financial Institutions
Access credentials for firewall and network administrator panels of Chinese financial institutions are being sold on the cybercrime forum BreachForums.
The threat actor (miyako) claims this access provides administrator privileges, enabling direct control over the internal network, including root-level remote code execution (RCE) and shell access on Linux-based firewall devices.
The threat actor (miyako) is known as an Initial Access Broker (IAB) dealing in initial penetration rights. They are promoting the ability to seize control of core infrastructure equipment for a relatively low price of $300, while also having a confirmed history of repeatedly selling access credentials to other companies’ firewalls.
Such leaks of administrator privileges on network perimeter devices can directly lead to full internal network takeover, financial data theft, additional ransomware deployment, and supply chain propagation attacks. This is assessed as a high-risk situation where exposure of a single account alone can escalate into an enterprise-wide breach.

- Database Leak Case
Affected company: w***s.com
A post claiming a large-scale data breach against W***s, Inc., a California-based mortgage broker, appeared on the cybercrime forum DarkForums.
W***s is a company that processes mortgage applications across multiple states through its proprietary loan processing platform.
The threat actor (FulcrumSec) claims to have stolen over 19,000 mortgage application documents, including development/operational environments, internal source code, and loan integration configuration data. They stated that highly sensitive information such as Social Security Numbers (SSNs), driver’s licenses, tax returns, bank account details, and income/debt information was included. Evidence indicates that detailed information was publicly disclosed in the form of some samples. The threat actor also claimed possession of technical materials related to financial infrastructure, including MongoDB credentials, internal loan program configurations, and interest rate engine source code. The sample data link provided at the time of the announcement (Feb 18, 2026) is currently inaccessible.
Considering the threat actor’s (FulcrumSec) past activities and reputation, the claims carry a certain level of credibility. However, the actual scope of the leak and the integrity of the data require further verification. Given the nature of mortgage application data, the risk of secondary financial fraud and identity theft is high, necessitating continuous monitoring.

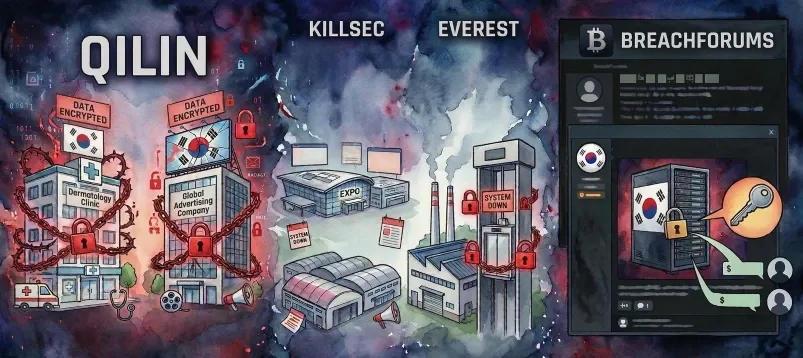
- Ransomware Infection Victim Cases
Ransomware groups such as CL0P, DragonForce, and Qilin have compromised numerous financial-related companies and publicly exposed victims on their dedicated leak sites (DLS). This report focuses solely on the top three most affected financial companies, selected based on corporate recognition and revenue scale, from among the many ransomware compromise cases this month.
Ransomware: Qilin
Affected company: t***e.com
The ransomware group Qilin has posted T***s as a victim.
However, approximately 12 hours after the posting, the leak page displayed a “Forbidden (#403) – Blog not active” error screen and was confirmed to be inaccessible.
This suggests the group may have temporarily deactivated the post, changed internal settings, or implemented access control measures. Additionally, some ransomware groups deactivate or delete posts after receiving ransom payments from victims. Therefore, the possibility that a ransom payment was made cannot be ruled out in this case. However, as there is currently no clear evidence to support this, this possibility should only be considered a hypothesis.
The actual release of data or plans for additional uploads also remain unclear. Therefore, continuous monitoring is necessary regarding the page’s reactivation status and potential secondary distribution.