Security Issues in the Financial Sector in December 2024

This report comprehensively covers actual cyber threats and security issues that have occurred in the financial industry in South Korea and abroad.
This includes the analysis of malware and phishing cases distributed to the financial sector, the Top 10 malware targeting the financial sector, and statistics on the industries of leaked South Korean accounts. A case of phishing emails distributed to the financial sector is also covered in detail.
Additionally, the analysis covers major financial threats and cases that occurred in the dark web, including the threat and cases of credit card data breach and database breach in financial institutions. It also includes the threat and cases of ransomware attacks targeting the financial sector, and various cyber threat and actual cases of attacks targeting financial institutions.
Key issues in the Deep and Dark Web Concerning the Financial Sector
Case of Database Leak
Affected Company: The name of the affected company has not been disclosed
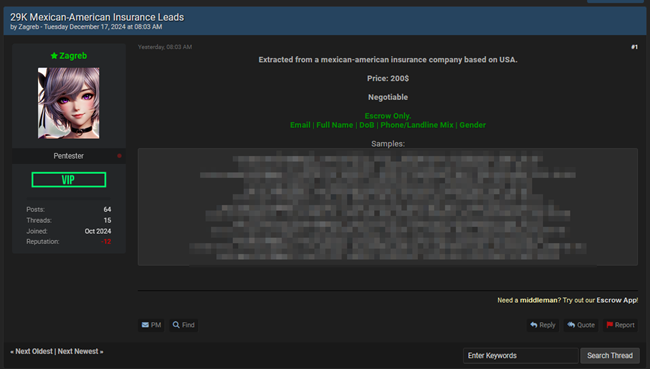
Data from a Mexican – U.S. insurance company whose name has not been disclosed is being sold on the cybercrime forum BreachForums.
The threat actor (Zagreb) did not disclose the name of the affected company, but claimed that the data was leaked from a Mexico – U.S. insurance company based in the United States. They also stated that the leaked data includes names, emails, dates of birth, phone numbers, and genders. Currently, a portion of the leaked data has been released as sample data and is being sold for $200.
As the affected company was not identified, there is a risk that the company’s clients may not be aware of the danger and may delay their response. This could cause confusion in assessing the scope of the damage and taking protective measures. If the leaked data is traced back to a Mexico-U.S. insurance company, there may be conflicts of legal jurisdiction and regulation between the two countries. There is a high risk that the leaked personal information, including names, email addresses, birth dates, phone numbers, and genders, may be exploited for phishing, spam, and identity theft. In particular, the fact that this information is already being shared as a sample and sold at a low price raises the urgency of the threat. Both companies and clients must actively monitor and take measures to protect their data.
Ransomware Breach Case
Ransomware groups such as 8Base, Bashe, Hunters International, and RansomHub have breached multiple financial companies and posted them as victims on their Dedicated Leak Sites (DLS). The cases of damage are as follows.
Ransomware: RansomHub
Affected Company: https://www.****life.com/
The ransomware gang RansomHub claimed responsibility for the attack on ****Life.
****Life is a U.S.-based global insurance and retirement services company that provides life, accident, and health insurance, as well as retirement and savings products. With a history of more than 153 years, it is trusted by millions of customers worldwide and serves 96 of the top 100 companies listed in the FORTUNE 500®. The company has also been named one of the “100 Most Just Companies” in the United States by JUST Capital for three consecutive years and has been engaging in over 315,000 hours of volunteer work with its employees in the communities it serves since 2021.
RansomHub claims to have stolen 1 TB of data from the organization and released a sample screenshot that includes a *** AFP document. *** AFP is a pension fund company in Chile that was acquired by ****Life in 2013. The gang explicitly stated that they would release the organization’s data on January 12th.
The fact that the attack targeted ****Life, a global insurance company in the United States, increases the likelihood that this incident will attract attention worldwide. As the stolen data amounts to 1TB, it is highly likely that the breach led to the exposure of sensitive information. In particular, the fact that documents related to the AFP were included raises concerns that customers’ financial and personal information may be exploited.
****Life must strengthen its security system through an immediate response and take proactive measures to restore customer trust. In addition, measures to protect local customers related to the AFP breach and further legal responses should also be considered. This incident may serve as a warning for the global financial and insurance industries to enhance their security measures.
 |
 |
Case of Access Permission Being Sold
Affected Company: Unnamed U.S. Mega Bank
Access to the firewall and VPN hosting servers of a large U.S. bank, whose name has not been disclosed, is being sold on the cybercrime forum BreachForums.
The threat actor (miyako) claimed to be selling root-level access to servers hosting the firewalls and VPNs of a large U.S. bank. The sale price is $1,000, and they stated that the price is non-negotiable. This threat actor has previously sold access to the firewall server of the German city-state government, access to an electronic device design and manufacturing company, and financial and asset management system data from Indonesia on BreachForums.
As the affected company has not been revealed, the trust in a wide range of institutions may be affected. If root access to servers hosting firewalls and VPNs is leaked, complete control of the bank’s internal network may be compromised. This could lead to not only financial data loss, but also the large-scale leak of customer information.
As the threat actor has a history of selling a large amount of sensitive data, it is highly likely that this incident will lead to secondary damages in a different form. To prevent such threats from reoccurring, the bank must strengthen their security measures and establish a threat monitoring system within their collaboration network. In addition, a thorough check on the vulnerabilities of the firewall and VPN security systems must be conducted following this incident.






