ASEC Weekly Malware Statistics (July 5th, 2021 – July 11th, 2021)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known malware. This post will list weekly statistics collected from July 5th, 2021 (Monday) to July 11th, 2021 (Sunday).
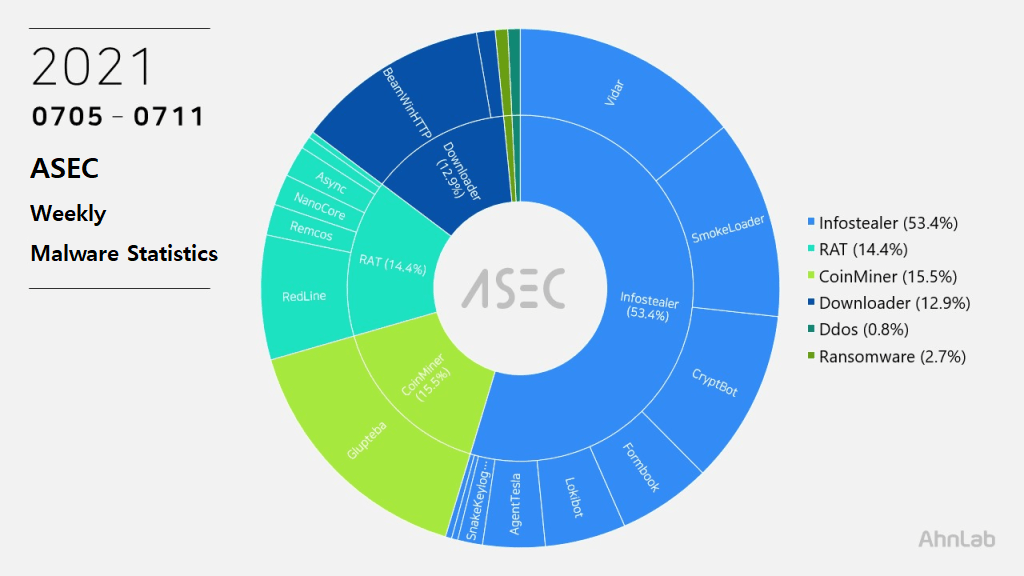
For the main category, info-stealer ranked top with 53.4%, followed by CoinMiner malware with 15.5%, RAT (Remote Administration Tool) malware with 14.4%, downloader with 12.9%, ransomware with 2.7%, and Ddos with 0.8%.
Top 1 – Glupteba
Glupteba is a malware developed with Golang, taking the first place with 15.5%. It downloads various additional modules and has various features, but it is actually a CoinMiner malware that installs XMR (Monero) CoinMiner.
When Glupteba is executed, it acquires the system permission by going through UAC Bypass and using TrustedInstaller’s permission. It then disguises as a normal process named C:Windowsrsscsrss.exe and remains in the system. Afterward, Glupteba downloads additional modules such as rootkit drivers for a purpose of concealing processes and files, and ultimately installs Eternal Blue package to spread through XMR CoinMiner and SMB vulnerabilities.
So far, most of the confirmed Glupteba samples are being downloaded and distributed via PUPs. Even though Glupteba is being distributed via PUP, it takes the appearance of a MalPe packer (it is mentioned in the previous blog post).
[Additional Module Download URL]
- hxxps://spolaect[.]info
[C&C Server URL]
- hxxps://ninhaine[.]com
- hxxps://2makestorage[.]com
- hxxps://nisdably[.]com
Top 2 – Vidar
An infostealer / downloader malware Vidar ranked second place with 14.0%. Vidar not only has features such as web browser, FTP, cryptocurrency wallet address, screenshot, but also has features that can download additional malware.
C&C URLs that were used during the period are the following.
- hxxp://157.90.127[.]76/933
- hxxp://157.90.127[.]76/865
- hxxp://157.90.127[.]76/890
- hxxp://157.90.127[.]76/706
- hxxp://turkcoder.com.tr[.]ht/main.php
- hxxp://162.55.223[.]232/933
- hxxp://162.55.223[.]232/313
- hxxp://162.55.223[.]232/865
- hxxp://notedrives.tr[.]ht/main.php
- hxxp://erolbasa.ac[.]ug/main.php
- hxxp://162.55.223[.]232/947
Top 3 – Smoke Loader
Smoke Loader is an info-stealer / downloader malware that ranked third place with 12.1%. For analysis report related to Smoke Loader, refer to the ASEC Report below.
[PDF] ASEC REPORT vol.101_Smoke Loader Learns New Tricks
The confirmed C&C server URLs are as follows.
- conceitosseg[.]com/upload/
- integrasidata[.]com/upload/
- ozentekstil[.]com/upload/
- finbelportal[.]com/upload/
- telanganadigital[.]com/upload/
- nusurtal4f[.]net/
- netomishnetojuk[.]net/
- netomishnetojuk[.]net/
- nick22doom4[.]net/
- wrioshtivsio[.]su/
- nusotiso4[.]su/
- rickkhtovkka[.]biz/
- palisotoliso[.]net/
- 999080321newfolder100231-service1022020[.]ru/
- 999080321newfolder100221-service1022020[.]ru/
- 999080321newfolder1002-012525999080321[.]ml/
- 999080321newfolder1002-012625999080321[.]ga/
- 999080321newfolder1002-012725999080321[.]cf/
- 999080321newfolder1002-012825999080321[.]gq/
Top 4 – BeamWinHTTP
BeamWinHTTP is a downloader malware that ranked fourth place with 11.7%. BeamWinHTTP is distributed via malware disguised as PUP installer. When it is executed, it installs PUP malware Garbage Cleaner and can download and install additional malware at the same time.
The confirmed C&C server URL is as follows.
- hxxp://g-partners[.]live
Top 5 – CryptBot
CryptBot malware ranked fifth with 10.6%. CryptBot is mainly distributed through malicious sites disguised as utility program download pages. Upon entering a certain keyword in the search engine, these malicious websites appear on the top page. When the PC is infected, it attempts to steal various user info and download additional malware.
The following are the C&C server URLs and additional malware download URLs of CryptBot.
- C&C1 : xeiqvo57[.]top/index.php
C&C2 : moraid05[.]top/index.php
Download URL : lopoga07[.]top/download.php?file=lv.exe - C&C1 : aleysn13[.]top/index.php
C&C2 : mordmy01[.]top/index.php
Download URL : otiasc01[.]top/download.php?file=lv.exe - C&C1 : xeinxk65[.]top/index.php
C&C2 : morksu06[.]top/index.php
Download URL : lopywn08[.]top/download.php?file=lv.exe - C&C1 : xeicwj77[.]top/index.php
C&C2 : moregy07[.]top/index.php
Download URL : lopxep10[.]top/download.php?file=lv.exe - C&C1 : alepez15[.]top/index.php
C&C2 : mordmy01[.]top/index.php
Download URL : otiasc01[.]top/download.php?file=lv.exe
The distributed filenames are as follows.
- Setup.exe
- setup_x86_x64_install.exe
- Main-Setup.exe
- x86_x64_setup.exe
- main_setup_x86x64.exe
- SetupFile-v16.2.9.exe
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.


