ASEC Weekly Malware Statistics (June 21st, 2021 – June 27th, 2021)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known malware. This post will list weekly statistics collected from June 21st, 2021 (Monday) to June 27th, 2021 (Sunday).
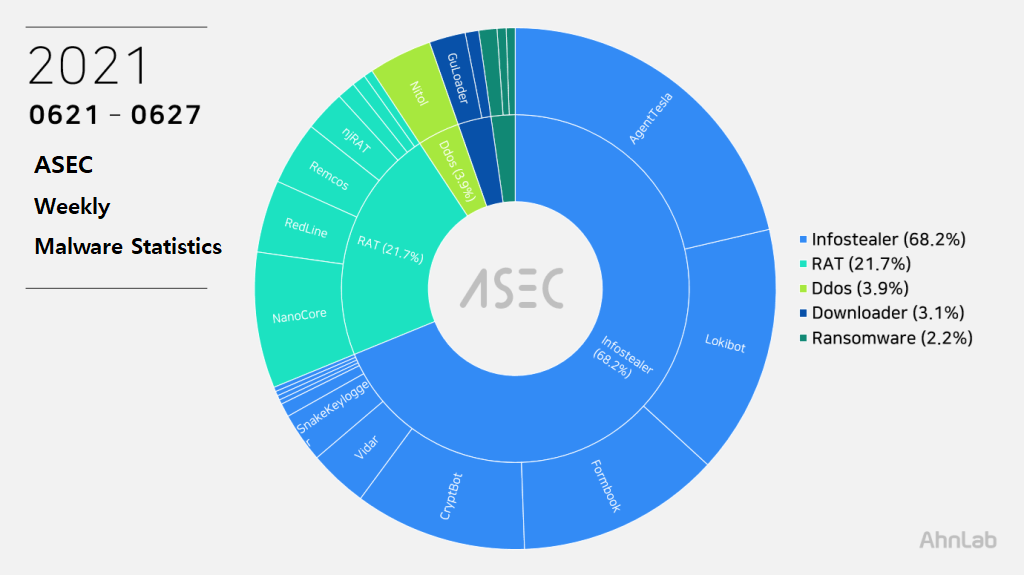
For the main category, info-stealer ranked top with 68.2%, followed by RAT (Remote Administration Tool) malware with 21.7%, DDoS with 3.9%, downloader with 3.1%, and ransomware with 2.2%.
Top 1 – AgentTesla
AgentTesla was ranked first place with 21.2%. It is an info-stealer malware that leaks user information saved in web browsers, e-mails, and FTP clients.
Recently collected samples use the following mail servers and user accounts when leaking the collected information.
- smtp.babcockvalve[.]com
sender : ziara.landa@babcockvalve[.]com
receiver : ziara.landa@babcockvalve[.]com
user : ziara.landa@babcockvalve[.]com
pw : hA$***%9 - smtp.ojototheworld[.]us
sender : alert@ojototheworld[.]us
receiver : alert@ojototheworld[.]us
user : alert@ojototheworld[.]us
pw : pas****21 - mail.w2opt[.]com
sender : zhengt@w2opt[.]com
receiver : darrishowe@yandex[.]com
user : zhengt@w2opt[.]com
pw : wTw****18
As most are distributed through spam mails disguised as invoice, shipment document, and purchase order, the file names contain such words shown above (Invoice, Shipment, P.O. – Purchase Order). Some samples have extensions disguised as document files such as pdf and xlsx or Auto CAD blueprint files such as dwg.
- TT Copy.exe
- statement_of_account.exe
- rfq-5754376.exe
- quotation-request xls.exe
- Purchase Order.exe
- PO_SJVN-NORYEPULL_#NPSJ-20210512.exe
- PO# PC00061945_000925062021.exe
- p-invoice#6547yrrf.exe
- PDA for Discharging 50000 mt Bagged rice at Conakry.exe
- Payment_Advice_Note_from_22.06.2021_to_608720.exe
- Order.pif
- Miray Kimya.exe
- LPG MARIA III_VSL PARTICULARS.docx.exe
- Kindly Confirmed all Details.exe
- invoice.pdf.exe
- invoice copy.pdf.exe
- handy vessel spec and descriptions.exe
- FEDEX_EXPRESS_TRACKING_-_COURIER_DELIVERY.exe
- DHL_Consignment_Details.exe
- BJ QUEEN – Vendor Template.docx.exe
- Bill Of Lading.exe
- 37300T, 37100T, 37150T GTIN.exe
- 20210623NQ001 LINYI YITONG INDUSTRIAL CO.LTD..exe
Top 2 – Lokibot
This week, Lokibot ranked second place with 15.3%. It is an info-stealer malware that leaks information about programs such as web browsers, mail clients, and FTP clients.
Being a malware that is distributed through spam mails, it shares similar distributed file names with other malware that are distributed through spam mails.
- Purchase Order (New)10115G*T_210623.exe
- Purchase Order (New)_10115__210624.exe
- Purchase Order (New)_10115[SA*]210624.exe
- Purchase Order (New)_10115[SA*]210622.exe
- Purchase Order (New)_10115[SA*]210621.exe
- Estimate Request_bk210623.exe
- Estimate Request_bk210622.exe
- Estimate Request_BK210621.exe
- Estimate Request_BK210620.exe
- SWIFT_Receipt.PDF.exe
- PURCHASE_ORDER.exe
- proforma-scan doc.exe proforma_pdf.exe
- PO_20210624_1747.exe
- PO_20210624.exe
- PEMBAYARAN_COPY_TT_PDF.exe
- New_PI&_Packing_list_062620021.exe
- FACTURAS.EXE
- facturas y datos bancarios.PDF.exe
- DHL_Receipt_pdf.exe
- Customer Advisory – Notice of implementing Congestion surcharge (CGD) (1).pdf.exe
- cotización.xlsx.exe
- Baltic Questionnaire.xls.exe
- 2021-06-22-Quotation-14478801 TMC.exe
- 2021062199000856.pdf.exe
As shown in the below, most Lokibot C&C server URLs tend to end in fre.php.
- hxxp://www.tepevizyon.com[.]tr/xx/Panel/fre.php
- hxxp://vihaiha[.]com/.cc/news/school/boy/choo/fre.php
- hxxp://exinmbakala[.]xyz/Panel/five/fre.php
- hxxp://es02[.]xyz/w2/fre.php
- hxxp://apponline97[.]ir/emoni/Panel/fre.php
- hxxp://apponline97[.]ir/china/Panel/fre.php
- hxxp://63.141.228[.]141/32.php/Uo2Q8E3IZNLpA
- hxxp://192.236.193[.]138/drain/drain/fre.php
- hxxp://192.119.111[.]43/zubby/fre.php
- hxxp://192.119.111[.]43/bosa/fre.php
Top 3 – Formbook
Formbook is an info-stealer malware ranked in third place with 12.5%.
Like other info-stealer malware, it is mainly distributed through spam mails. The distributed file names are close to each other.
- CONTRACT_PROPOSAL_&ORDER_LIST.exe
- DHL__Shipment_Documents.exe Document.exe
- ilshin trading co..exe
- INV_10909_202141227.exe
- INV8251335466774.exe
- New_Order_PO_1164_HD-F_4020_6K.exe
- Order210622.exe
- po.exe
- PO_NEW_ORDER_002001123.exe
- po22062021rfq.exe
- PURCHASE_CONTRACT#GJPL1202_2021-22PDF.exe
- QMF21950622.exe
- Quotation.exe
- quote.exe
- quotee.exe
- s l biochemical po#slb210624-001.exe
- samil pharm po#slb210624-001.exe
- scandocument2021_pdf.exe
- Shipment_Document_BL,INV_and_Packing_list_Attached.exe
- Shipping_Document_DHL.exe
- urgentneworder_pdf.exe
As Formbook is injected in a normal process that is in the directory of explorer.exe and system32, the malicious behaviors are performed by the normal process. Besides user account information in the web browser, the malware can steal various information through keylogging, clipboard grabbing, and web browser form grabbing. Below is the list of confirmed C&C server URLs of Formbook.
- hxxp://www.baincot[.]com/nins/
- hxxp://www.blaxies3[.]com/xfts/
- hxxp://www.blinbins[.]com/q4kr/
- hxxp://www.bonap56[.]com/im85/
- hxxp://www.calsury[.]com/wlns/
- hxxp://www.cenfoxy[.]com/bgr7/
- hxxp://www.cinmax[.]xyz/hw26/
- hxxp://www.jam-nins[.]com/3nop/
- hxxp://www.kuppers[.]info/uerb/
- hxxp://www.mimik33[.]info/pb93/
- hxxp://www.nelivo[.]com/bwk/
- hxxp://www.racevx[.]xyz/qjnt/
- hxxp://www.ravexim3[.]com/sgs8/
- hxxp://www.senmec23[.]com/se5w/
- hxxp://www.valengz[.]com/lt0h/
Top 4 – CryptBot
This week, CryptBot malware ranked fourth with 10.6%. CryptBot is mainly distributed through malicious sites disguised as utility program download pages. Upon entering a certain keyword in the search engine, these malicious websites appear on the top page. When the PC is infected, it attempts to steal various user info and download additional malware.
The following are the C&C server URLs and additional malware download URLs of CryptBot.
- C&C1: kiylbx57[.]top/index.php
C&C2: morunx05[.]top/index.php
Download URL: peoscn07[.]top/download.php?file=lv.exe - C&C1: cypaev17[.]top/index.php
C&C2: mordiu01[.]top/index.php
Download URL: dugiry01[.]top/download.php?file=lv.exe - C&C1: cypdgs21[.]top/index.php
C&C2: morutv02[.]top/index.php
Download URL: dughos03[.]top/download.php?file=lv.exe - C&C1: cypquv37[.]top/index.php
C&C2: morkyl03[.]top/index.php
Download URL: dugyly04[.]top/download.php?file=lv.exe - C&C1: cypkcq51[.]top/index.php
C&C2: morons05[.]top/index.php
Download URL: dugykz07[.]top/download.php?file=lv.exe
The distributed filenames are as follows.
- setupinstall.exe
- setup.exe
- setup_x86_x64_install.exe
- x86_x64_setup.exe
- p6.exe
- p6-2.exe
Top 5 – NanoCore
NanoCore ranked fifth place with 8.4%. It is a RAT malware developed with .NET. Like njRAT, it can perform various commands given by the attacker such as information leakage including keylogging.
Similar to AgentTesla, Formbook, AveMaria, and Remcos, the NanoCore is packed with .NET packing and distributed through attached files in spam mails. As such, the file names reported are not much different from those of other malware distributed through spam mails.
- vc_redist.x 64 (MandatoryRun).exe
- Specifications.pif
- SCANNED DOCUMENTS_EXPORT1020938 IMG054550 GEOS800 SCAN_pdf.exe
- Signed Purchase Order POUS4509622207.exe
The following list is the confirmed C&C server domains for NanoCore.
- wekeepworking12.sytes[.]net
- wekeepworking.sytes[.]net
- typejimbo.ddns[.]net
- quill.sytes[.]net
- pripri.duckdns[.]org
- night90.ddns[.]net
- newnano.ddns[.]net
- mafian222.ddns[.]net
- justinalwhitedd554.duckdns[.]org
- james12.ddns[.]net
- innocentbooii.hopto[.]org
- ifybest85fff.ddns[.]net
- fuck90.duckdns[.]org
- dubby2021.duckdns[.]org
- dbb.turbo-sy[.]com
- backu4734.duckdns[.]org
- alexwill.ddns[.]net
- 1116.hopto[.]org
Others – Nitol
Nitol did not make it into Top 5 as not many cases were found when compared with other malware, but it is noticeable that Nitol DDoS malware is constantly being reported. This malware is being distributed via archive of certain forum, and the attacker uploaded multiple posts with seed file of torrent which downloads malware. Nitol sample files distributed from this archive all use the same C&C URL, and they were disguised as installer files of various programs.
Nitol can perform malicious behaviors such as downloading additional malware and DDoS attacks by receiving commands from C&C server.
File names, file paths and C&C server URL of Nitol that are being distributed are as follows.
C&C: rlarnjsdud0502.kro[.]kr
- \[Official Korean Version] Office 2007\setup.exe
- \HWP 2020\crack.exe
- \microsoft office 2016\setup.exe
- \HancomOffice_ForEducationalInstitution_2020\install.exe
- \adobe illustrator 2020\install.exe
- \kmsauto net 2015 v1.4.5 portable\kmsauto net.exe


