ASEC Weekly Malware Statistics (May 24th, 2021 – May 30th, 2021)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known malware. This post will list weekly statistics collected from May 24th, 2021 (Monday) to May 30th, 2021 (Sunday).
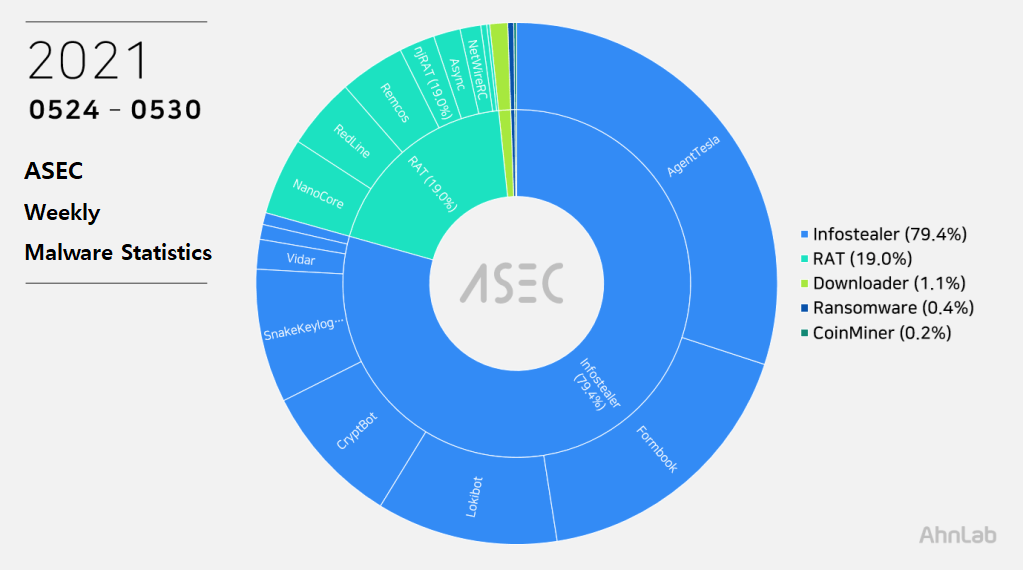
For the main category, info-stealer ranked top with 79.4%, followed by RAT (Remote Administration Tool) malware with 19.0%, downloader with 1.1%, ransomware with 0.4%, and CoinMiner with 0.2%.
Top 1 – AgentTesla
AgentTesla was ranked first place with 30.0%. It is an info-stealer malware that leaks user information saved in web browsers, e-mails, and FTP clients.
Recently collected samples use the following mail servers and user accounts when leaking the collected information.
- smtp.yandex.com
sender: alberthumphery@yandex.com
receiver: alberthumphery@yandex.com
user: alberthumphery@yandex.com
pw: we***gic123 - smtp.ojototheworld.us
sender: alert@ojototheworld.us
receiver: alert@ojototheworld.us
user: alert@ojototheworld.us
pw: pa***2020 - smtp.boydsteamships.com
sender: davide.cavallaro@boydsteamships.com
receiver: davide.cavallaro@boydsteamships.com
user: davide.cavallaro@boydsteamships.com
pw: gy***jZMW5
As most are distributed through spam mails disguised as invoice, shipment document, and purchase order, the file names contain such words shown above (Invoice, Shipment, P.O. – Purchase Order). Some samples have extensions disguised as document files such as pdf and xlsx or Auto CAD blueprint files such as dwg.
- 5_25_2021_73632xls.exe
- DA_Query_-180397-03-03-21_Port_Agency_Appointment_pdf.exe
- DHL.exe
- Document_01928832.pdf.exe
- Enquiry_requirements_20210526.exe
- INV-257591_77134027.exe
- MV.PVT DIAMOND V.21089.exe
- MV._WANTONG_SPIRIT_V.2101-_PDA_for_loading_31000mt_coke_IN_BULK_pdf.exe
- NEW PO2309.exe
- NISAN_2021_EKSTRE.exe
- old invoice payment1.exe
- Order #7763888DG0E.exe
- Order_Data_Specification_Sheet.exe
- ORDER_TBLFG252021.exe
- Payment Advice Note from 26.05.2021 to 608710.exe
- PAYMENT_ADVISE.exe
- PAYMENT_BANK_INSTRUCTIONS_COPY.exe
- payment_copy.exe
- PO21000641.exe
- pre final hire invoice doc-no. 165655739 030nov2020 (mon) 1958 (+0530) sxs_pdf.exe
- proofofpayment.exe
- Purchase order.exe
- qoute_pdf.exe
- quotes.exe
- Request for quotation SPRANWPD21020.pdf.exe
- Request_for_PDA_pdf.exe
- RF-SHIPTPY20210524.exe
- Scan docs.exe
- TBN__PDA_quotation_for_discharging_cement_pdf.exe
- updated_statement.exe
Top 2 – Formbook
Formbook is an info-stealer malware ranked in second place with 17.5%.
Like other info-stealer malware, it is mainly distributed through spam mails. The distributed file names are close to each other.
- 210503_mcdermott_nfe_rfq.exe
- Advised Original Copy.exe
- BANK DETAILS.exe
- content.3534.28278.10140
- List of quotation items_pdf.exe
- NEW ORDER01.exe
- New_Order_PO_1164_HD-F_4020_6K.exe
- Outstanding orders.exe
- Pdf MT103 – Remittance.pdf.exe
- Pdf_Scen_Invoice_17INV06003.exe
- PO_2021005.exe
- price-quotation-2.exe
- Quotation.exe
- Req_Invoice.exe
- rfq & product details-revisedcopy 20210521_pdf.exe
- rfq_brat_metal_tech_ltd.exe
- Specification_HT_20200527.exe
- SWIFT_JP.SCR
- SWIFT-EUR_51720-PDF.exe
- SWIFT-PDF.exe
Also, it was confirmed that the site that distributes CryptBot disguising as a utility program download page is distributing Formbook as well. The filenames of these distributed malware are disguised as installer filenames
- x86_x64_setup.exe
- setup_installer.exe
- setup_install.exe
As Formbook is injected in a normal process that is in the directory of explorer.exe and system32, the malicious behaviors are performed by the normal process. Besides user account information in the web browser, the malware can steal various information through keylogging, clipboard grabbing, and web browser form grabbing. Below is the list of confirmed C&C server URLs of Formbook.
- hxxp://www.baincot[.]com/aipc/
- hxxp://www.bostonm[.]info/onqm/
- hxxp://www.bunies3[.]com/cu6s/
- hxxp://www.byonf[.]com/nyd/
- hxxp://www.casnop[.]com/ccr/
- hxxp://www.chaytel[.]com/dxe/
- hxxp://www.contex3[.]info/vfm2/
- hxxp://www.contorig2[.]com/u8nw/
- hxxp://www.cunerier[.]com/m3rc/
- hxxp://www.danfrem[.]com/grb/
- hxxp://www.iregentos[.]info/nu8e/
- hxxp://www.joomlas123[.]info/n7ak/
- hxxp://www.jumlasx[.]xyz/ewws/
- hxxp://www.jumtix[.]xyz/a9ab/
- hxxp://www.juxrams[.]info/cgsp/
- hxxp://www.luisxe[.]info/ngvm/
- hxxp://www.magentos6[.]com/suod/
- hxxp://www.magetu[.]info/p2io/
- hxxp://www.mex33[.]info/ainq/
- hxxp://www.mimik33[.]info/66op/
- hxxp://www.nelivo[.]com/bwk/
- hxxp://www.psm-gen[.]com/dei5/
- hxxp://www.racevx[.]xyz/3edq/
- hxxp://www.senmec23[.]com/i8be/
- hxxp://www.solevux[.]com/fw6/
- hxxp://www.suxfi[.]com/hlx/
- hxxp://www.tomrings[.]com/a8si/
Top 3 – Lokibot
This week, Lokibot ranked third place with 11.2%. It is an info-stealer malware that leaks information about programs such as web browsers, mail clients, and FTP clients.
Being a malware that is distributed through spam mails, it shares similar distributed file names with other malware that are distributed through spam mails.
- Estimate Request _20210525.xls
- 0526_General Order.exe
- Ac*biopharm.exe
- dkol0010-bb011.exe
- DR0638.dwg.exe
- GT210526 RFQ_01.xls.exe
- IN*UNG_PO6001255.exe
- Jin*ung Precision.exe
- List of Quotataion.exe
- NRTEC RFQ_21523UY-1.exe
- NRTEC RFQ_21525HF78.exe
- ORDER.exe
- PO 210524-0122.exe
- PO 210525-0021.exe
- PO 210526-054.exe
- PO 210528-2101.exe
- PO_20210528.exe
- PO20210517.exe
- Po20210526.exe
- PO210525.exe
- PO26052021.exe
- PO5660012.exe
- PO858696000060.exe
- PURCHASE.exe
- QUOTATION-FORM.exe
- QUOTE B1020363.exe
- Quote JQ102474.pdf.exe
- Quote.exe
- Quote-4563-20210528.exe
- Tae*insa RFQ 210528GH5.exe
- TBN LOAD STEELS – 26.05.2021.xlsx.exe
- ttr_117843-20210528.exe
- VT-154-210525.exe
- VT-154442-210526.exe
- VT-LIST-1544-210526.exe
- Woo*ung Enterprise.exe
As shown in the below, most Lokibot C&C server URLs tend to end in fre.php.
- hxxp://104.168.166[.]188/agwo/fre.php
- hxxp://104.168.175[.]179/agwo/panel/fre.php
- hxxp://173.208.204[.]37/k.php/1FfRFNkqX9s48
- hxxp://axz1[.]xyz/wv1/fre.php
- hxxp://digitaltaqwa[.]com/scss/five/fre.php
- hxxp://gimpex-imreys[.]com/Bn2/fre.php
- hxxp://greenbazaar[.]xyz/blac/panel/five/fre.php
- hxxp://locandasolagna[.]xyz/dar/panel/five/fre.php
- hxxp://manvim[.]co/fc5/fre.php
- hxxp://mbyi[.]xyz/five/fre.php
- hxxp://nijawright[.]tk/documents/fre.php
- hxxp://sspmoct[.]xyz/tkrr2/T2/43t/fre.php
- hxxp://underdog1[.]xyz/taker/Panel/five/fre.php
- hxxp://vietphatjsc[.]xyz/dumbo/dumbo3/fre.php
- hxxp://vihaiha[.]com/.cc/news/school/boy/choo/fre.php
Top 4 – CryptBot
CryptBot malware, for the first time, ranked fourth place with 8.8%. The malware is downloaded through PUP programs and has features of stealing additional information and downloading additional malware.
It is mainly distributed from phishing sites disguised as utility program download pages which are shown when searching certain keywords in Google.
The following are the confirmed C&C server URLs and additional malware download URLs of CryptBot.
- C&C 1 : hxxp://geotuk27[.]top/index.php
C&C 2 : hxxp://moreok02[.]top/index.php
Download URL : hxxp://rogmzx03[.]top/download.php?file=lv.exe - C&C 1 : hxxp://soguex75[.]top/index.php
C&C 2 : hxxp://moreru07[.]top/index.php
Download URL : hxxp://doumbw10[.]top/download.php?file=lv.exe - C&C 1 : hxxp://geozwy35[.]top/index.php
C&C 2 : hxxp://morzax03[.]top/index.php
Download URL : hxxp://rogyqs04[.]top/download.php?file=lv.exe - C&C 1 : hxxp://sogqfs71[.]top/index.php
C&C 2 : hxxp://moreru07[.]top/index.php
Download URL : hxxp://doumbw10[.]top/download.php?file=lv.exe - C&C 1 : hxxp://geoytl61[.]top/index.php
C&C 2 : hxxp://moruxl06[.]top/index.php
Download URL : hxxp://rogsjt09[.]top/download.php?file=lv.exe
The filenames distributed from phishing sites disguised as utility program download pages are as follows.
- setup_x86_x64_install.exe
- Mainsetupv1.0.exe
- newfullserup.exe
- Setup.exe
- x32_x64_mainsetup.exe
- main-setupfile.exe
Top 5 – SnakeKeylogger
Taking fifth place with 8.3%, SnakeKeylogger is an info-stealer type malware that leaks information such as user key inputs, system clipboards, and browser account information.
Like AgentTesla, this malware uses mail servers and user accounts when leaking collected information. The following is the accounts used by recently collected samples.
- mail.prozero-d[.]com
sender: chuki@prozero-d[.]com
receiver: chuki@prozero-d[.]com
user: stchuki@gmail[.]com
pw: icu***u2@@ - mail.adionshop[.]ro
sender: goziee@adionshop[.]ro
receiver: goziee@adionshop[.]ro
user: goziee@adionshop[.]ro
pw: 1rAvd***-Hq[ - smtp.vivaldi[.]net
sender: fastonefast@vivaldi[.]net
receiver: fastonefast@vivaldi[.]net
user: fastonefast@vivaldi[.]net
pw: cass***12345
Similar to other info-stealer malware, it is distributed through spam mails disguised as invoices, shipment documents, and purchase orders, so the file names contain such words shown above (Invoice, Shipment, P.O. – Purchase Order).
- requested_product_lists.PDF_________________________________________________.exe
- KPCPU-231(MECH)NBI20-21.exe
- New_Order.exe
- Our REVISED Order 5252021.exe
- po_51637.exe
- Quotation#975072.exe
- QUOTATION_REQUIREMENT.exe
- SoapYearMonth.exe
- Spare Parts Quotation.exe
- Swift-Copy.exe



