ASEC Weekly Malware Statistics (April 26th, 2021 – May 2nd, 2021)

The ASEC analysis team is using the ASEC automatic analysis system RAPIT to categorize and respond to known malware. This post will list weekly statistics collected from April 26th, 2021 Monday to May 2nd, 2021 Sunday.
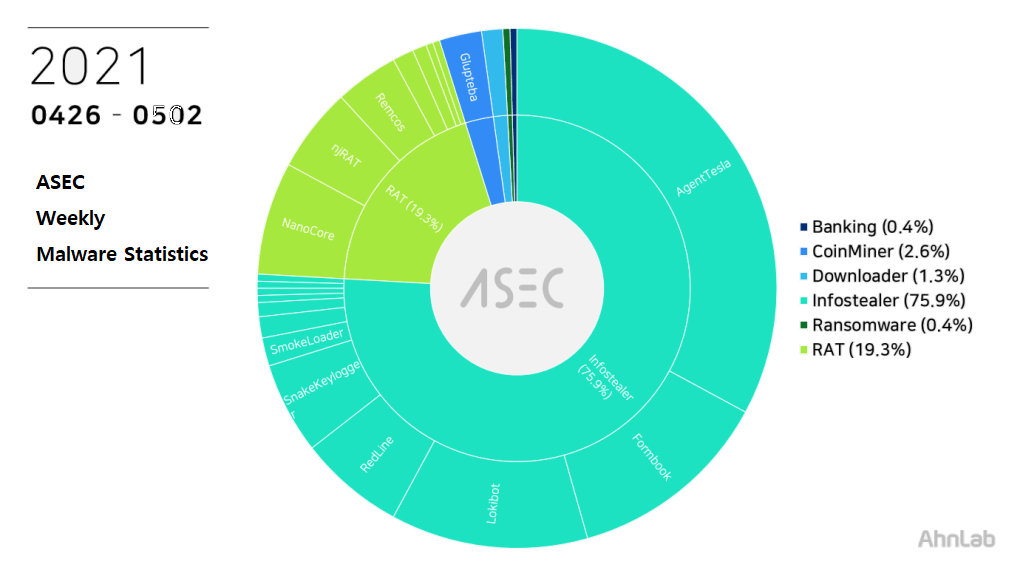
For the main category, info-stealer ranked top with 75.9%, followed by RAT (Remote Administration Tool) malware with 19.3%, downloader with 1.3%, and CoinMiner with 2.6%. Ransomware and banking malware accounted for 0.4%.
Top 1 – AgentTesla
AgentTesla was ranked first place with 32.9%. It is an info-stealer malware that leaks user information saved in web browsers, e-mails, and FTP clients.
Recently collected samples use the following mail servers and user accounts when leaking the collected information.
- mail.barraprime[.]com
sender: info@barraprime[.]com
receiver: info@barraprime[.]com
user: info@barraprime[.]com
pw: 1mar****17 - wasstech[.]com
sender: rasha.adel@wasstech[.]com
receiver: rasha.adel@wasstech[.]com
user: rasha.adel@wasstech[.]com
pw: Sunr****00@@ - smtp.oneoceanmaritimes[.]com
sender: mylogs2021@oneoceanmaritimes[.]com
receiver: mylogs2021@oneoceanmaritimes[.]com
user: mylogs2021@oneoceanmaritimes[.]com
pw: (mH****8 - mail.privateemail[.]com
sender: moj@bosenmouid[.]com
receiver: moj@bosenmouid[.]com
user: moj@bosenmouid[.]com
pw: m****7 - smtp.privateemail[.]com
sender: aammorris@askoblue[.]com
receiver: aammorris@askoblue[.]com
user: aammorris@askoblue[.]com
pw: hb****^3
As most are distributed through spam mails disguised as invoice, shipment document, and purchase order, the file names contain such words shown above. Some samples have extensions disguised as document files such as pdf and xlsx or Auto CAD blueprint files such as dwg.
- Invoice and Package Listpdf_____________________.exe
- albarán factura_pdf____________________________________.exe
- ALTISYS_MANU_29042021_164906_2_479.pdf.exe
- BANK_DETAIL.exe
- BL Draft – HL-88313627-1.exe
- Fattura_0011_20201230_TRAFILERIE_EDOARDO_GILARDI_C_S_R_L_.exe
- Mercury J – UNISEASMARINE.exe
- MV *ONGSHENG 7 PDA.exe
- MV TBN CALL PORT FOR LOADING COAL.exe
- NEW_ORDER.exe
- orden de compra_pdf________________________.exe
- payment_copy.exe
- po#kv18re001_a5491ngocquangtradeproductionservices.exe
- Purchase_order_4500353628_1717154.PDF.exe
- purchase_order_pdf.exe
- RFQ # 041620-1 – 28 Gate Valves.exe
- SMK_6094183725.exe
- SWIFT Payment 20201229 – TC -ref00D208FT.pif.exe
- SWIFT_9500USD.exe
- WIRE_TRANSFER_FORM.exe
Top 2 – Formbook
Formbook is an info-stealer malware ranked in second place with 12.7%.
Like other info-stealer malware, it is mainly distributed through spam mails. The distributed file names are also similar to those of other malware.
- shipping_document_PDF.exe
- REQUIRED_DOCUMENTS.exe
- REQUEST_FOR_QUOTATION.exe
- PO74848393.exe
- po-647484637-rfq.exe
- PO-21-8095-UTI*ECH.exe
- PO-2021-UTI.pdf.exe
- MV._Ever_Reliance_009423578-_doc.exe
- IMG_067791.exe
As Formbook malware is injected in a normal process that is in the directory of explorer.exe and system32, the malicious behaviors are performed by the normal process. Besides web browser user account information, the malware can steal various information through keylogging, clipboard grabbing, and web browser form grabbing. Below is the list of confirmed C&C server URLs of Formbook.
- hxxp://www.cunerier[.]com/svh9/
- hxxp://www.chaytel[.]com/zui/
- hxxp://www.psm-gen[.]com/dei5/
- hxxp://www.nelivo[.]com/ple/
- hxxp://www.magentos6[.]com/b3gc/
- hxxp://www.lownak[.]com/gnk/
- hxxp://www.forenvid[.]com/vns/
- hxxp://www.floryi[.]com/z1u/
- hxxp://www.curiget[.]xyz/uabu/
- hxxp://www.cunerier[.]com/svh9/
- hxxp://www.contorig2[.]com/uv34/
- hxxp://www.contex33[.]xyz/uwec/
- hxxp://www.cinmax[.]xyz/sbjq/
- hxxp://www.cinmax[.]xyz/n7ad/
- hxxp://www.chaytel[.]com/zui/
- hxxp://www.byonf[.]com/gmn/
- hxxp://www.byonf[.]com/dug/
Top 3 – Lokibot
Lokibot takes third place with 12.3%. It is an info-stealer malware that leaks information about programs such as web browsers, mail clients, and FTP clients.
It shares similar distributed file names with other malware distributed through spam mails.
- DHL Receipt.bin
- DKOL0010-BA017.exe
- DKOL0010-BA018.exe
- DKOL0010-BB011.exe
- invoice-26.exe
- Junsung_210429 – 1.exe
- List of quotation items.exe
- LIST.exe
- ORDER.exe
- PO 210429-09.exe
- po 210430-102.exe
- PO#2021-834-1.exe
- PO.exe
- PO2604000093.exe
- PO5R57TGFFV.exe
- prj no. pg6432 khe shell-rfq-project documents & specs.exe
- QUOTATION-FORM.exe
- RFQ#42605_-_URGENT_QUOTE_REQUIRED.exe
- SYC-Q-12036(KP14 199252451) – FITTING(1).exe
- vt-154-21-khi ( 27-4-2021).exe
As shown in the below, most Lokibot malware C&C server URLs tend to end in fre.php.
- hxxp://173.208.204[.]37/k.php/9n12ImA5kRa6Y
- hxxp://104.168.140[.]79/bona/fre.php
- hxxp://104.168.140[.]79/oga/fre.php
- hxxp://104.168.175[.]179/capo/panel/fre.php
- hxxp://104.168.175[.]179/smick/panel/fre.php
- hxxp://104.168.213[.]88/ghost1/fre.php
- hxxp://173.208.204[.]37/k.php/209hwrrIygNFO
- hxxp://209.141.50[.]70/mmc/300/pin.php
- hxxp://31.210.20[.]71/tele/fre.php
- hxxp://bobydomain[.]com/okfile/five/fre.php
- hxxp://eyecos[.]ga/chang/gate.php
Top 4 – NanoCore
NanoCore ranks fourth place with 7.0%. It is a RAT malware developed with .NET. Like njRAT, it can perform various commands given by the attacker such as information leakage including keylogging.
Similar to AgentTesla, Formbook, AveMaria, and Remcos, the NanoCore is packed with .NET packing and distributed through attached files in spam mails. As such, the file names reported are not much different from those of other malware distributed through spam mails.
- COMUNICADO DE PARTE DE LA SECRETARIA DE INDUSTRIA.exe
- DFG_20938765637893.exe
- ennoblers_6251.exe
- Hpn_3093876-093873invc.exe
- NZA_098765367KJFH.exe
- ORDER SHEET – SUMMER 2021.exe
- po#kv18re001_a5491ngocquangtradeproductionservices.exe
- po.pdf.exe
- PO_copy.pdf.exe
The following list is the confirmed C&C server domains for NanoCore.
- kengoerge018.ddns[.]net
- 1119.hopto[.]org
- seatosea.duckdns[.]org
- timmy04.ddns[.]net
- kenzeey.duckdns[.]org
- kenzeey.ddns[.]net
- haash.duckdns[.]org
- windowslivesoffice.ddns[.]net
Top 5 – RedLine
For the first time, RedLine malware ranked fifth place with 6.6%. The malware steals various information such as web browser, FTP client, cryptocurrency wallet, and PC settings. It can also download additional malware by receiving commands from the C&C server.
The following are the confirmed C&C server domains for RedLine:
- hxxp://briaseynan[.]xyz
- hxxp://87.251.71[.]153
- hxxp://videdoshin[.]xyz


