Distribution of Hangul Word Processor File (HWP) during Academic Conference Season in Korea

On May, ASEC analysis team shared details of Hangul Word Processor file (HWP) malware that is being distributed across various fields (see blog post below). In the past, it was distributed with the titles related to ‘real-estate,’ however, malware today is developed with titles related to thesis and other academic items based on the scheduled academic conferences in Korea.
So far, AhnLab discovered 2 filenames that are being used by malicious HWP files, and among the topics discussed in the blog post above, the used technique belongs to the ‘Others’ section. The HWP file, when run, does not show its contents to the user normally. Instead, it only performs the action of downloading the secondary malicious file.
- 2020_XXXX_Thesis on Superconductivity.hwp
- Academic conference.hwp
It is assumed that the attacker of the malware targeted time period between May and July, when summer-season academic journals are usually submitted. The submitted malicious HWP file shows malicious behavior similar to that of internal EPS (Encapsulated PostScript) script that was introduced before.
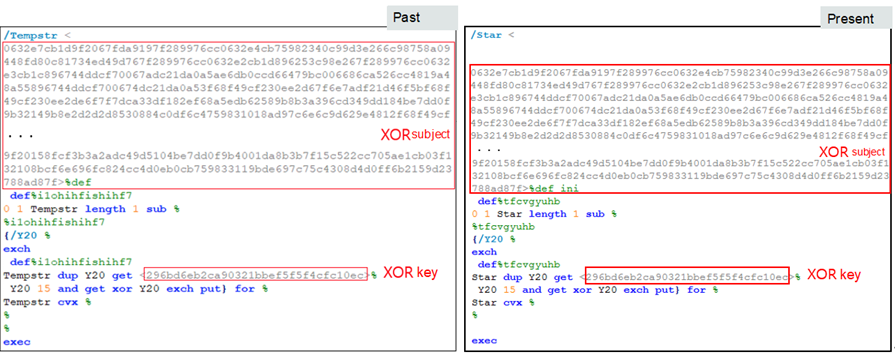
The malware is being distributed with an added blank or a different variable name within the script to bypass anti-malware detection, and the key info required to decrypt XOR-encoded shellcode is the same as the old malware. With this, we can assume the malware is being distributed under various names by the same attacker.
The shellcode integrated into EPS downloads the secondary malicious file (*.BAT, *.CAB) from the C2 server. The archive file with CAB format includes the files shown below, collects certain info from the user PC, sends it to C2 server, and downloads additional files.

The following is detailed explanations of the execution flow started by the internal EPS code upon launching the HWP file.
Stage 1) Download script
The encrypted shellcode downloads batch script (‘no1.bat’) and Base64-encoded CAB archive file (‘vbs.txt’).
There are various scripts within the CAB archive file such as the ones below:
- hxxp://resulview.com/5hado/no1.txt
- hxxp://resulview.com/5hado/vbs.txt
Stage 2) Add autorun
– Adds run key for autorun.
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run
- Add start.vbs within the CAB archive file to ‘svchostno2.’
Stage 3) Collect and upload info
– Collect the information below from the user PC and send it to the malicious C2 (hxxp://resulview.com/5hadr/upload.php).
- List of downloads folder
- List of documents folder
- Desktop
- List of Program Files
- IP address of user PC
- List of tasklist
- Systeminfo of user PC
Stage 4) Additional Download
The PC infected with this malware has a downloading feature to allow the attacker to perform additional activities. Thus, additional damage is expected after data leakage from PC. The downloaded file is assumed to be an archive file, and it runs via ‘temprun.bat’ which is the internal file. Furthermore, it is designed to decide whether to terminate the script by the existence of ‘pakistan.txt.’
- Download URL: hxxp://resulview.com/5hado/%COMPUTERNAME%.txt
The ground zero of the HWP file is currently distributing the malware with filename ‘Naver blog lawsuit.hwp,’ therefore users must not open document files from unknown sources (key features such as C2 and URL take the form of academic info).
AhnLab’s V3 products detect the malware under the following aliases:
- Exploit/HWP.Generic (2020.06.04.05)
- EPS/Exploit.mexp (2020.02.08.00)
- Malware/MDP.Execute.M1473




