New NEMTY Ransomware v3.1 Being Distributed in Korea (April 1, 2020)

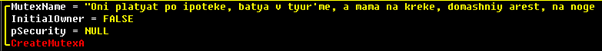
On April 1, AhnLab ASEC detected distributions of NEMTY REVENUE 3.1, which is the updated version of NEMTY ransomware. Similar to the previous version, the malware was distributed through an email attachment. Detected filenames are ‘resume’, ‘portfolio’, ‘breach of electronic commerce act,’ which are hardly changed compared to the previous version.
- Request for the retention of data processing and nontranscriptional resource (20200401)_retain resource to prevent unjust gain.exe
- Notice on violation of electronic commerce act_retain resource to prevent unjust gain.exe
- Resume_Kim Ji-myung_I will work hard with passion and enthusiasm thank you.exe
- Portfolio_Kim Ji-myung_I will work hard with passion and enthusiasm thank you.exe
Key features of the ransomware remain unchanged, but unlike NEMTY v2.x, there were changes in desktop and infection-excluded extensions & files after infection. Furthermore, it is not infected if the network is unavailable, and there are no changes in desktop either.
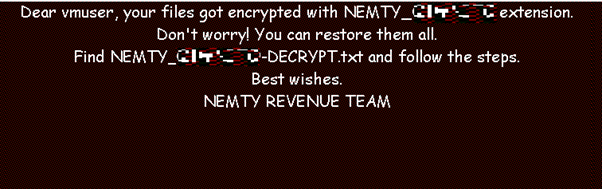
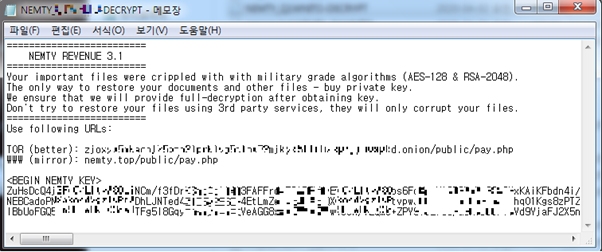
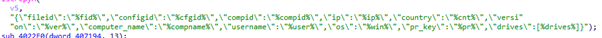
Unlike Nemty v2.x, log, program files (x86), NEMTY, .mp3, .mp4, .NEPHILIM, .msi infection-excluded folders, filenames, and extensions were added, and there were excluded files and folders. It does check for the country, but codes such as infection-exclusion code have disappeared.
| Excluded folders and filenames | windows, $RECYCLE.BIN, rsa, NTDETECT.COM, |
| Excluded extensions | .pif, .ttf, .url, .dll, .ini, .cpl, .com, .cmd, .cab, .log, .exe, .lnk, .mp3, .mp4, .NEPHILIM, .msi |
NEMTY v2.x was continually distributed from November 2019 to March 17, 2020 and the updated version v3, has continually been distributed via social engineering technique since April 1 this year. Users must take extra caution when opening a suspicious email or attachment file. AhnLab’s V3 products detect the ransomware under the following aliases:
[File Detection]
- Trojan/Win32.MalPe (2020.04.01.05)




