[Caution] makop Ransomware Disguised as a Resume (April 13)
![[Caution] makop Ransomware Disguised as a Resume (April 13)](https://asec.ahnlab.com/wp-content/uploads/2020/09/mask_keyboard-1-803x490.png?crop=1)
On April 13, ASEC analysis team discovered makop ransomware disguised and distributed as a resume. It is being distributed in the form of an archive attachment file via email, and there are Hangul Word Processor file (.hwp) icon and an executable (exe) within the archive file. The filename of the distributed file confirmed on the same day contained an unnatural sounding sentence and the word spacing was awkward. From this, we can assume that the malware distributor is not a fluent Korean speaker.
- Portfolio(200413)_I will work with diligence regardlessof tasks given to me)
- Resume(200413)_I will work with diligence regardlessof tasks given to me)
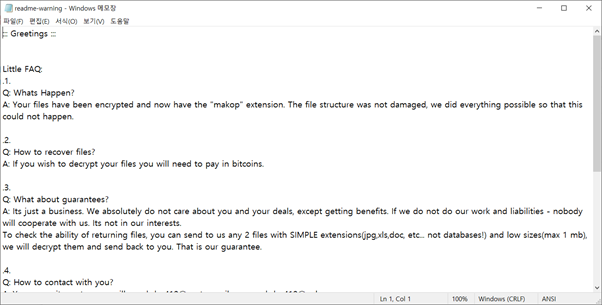
Upon infection, the filename is changed to original filename.[8 random characters].[akzhq412@protonmail.ch].makop.
The ransomware disguising as a resume that used MalPe packer is being distributed 2–3 times per month by using different ransomware each time. The distribution method and the use of packer remain unchanged, but users must remain vigilant due to consistent attacks. When opening an email and running an attachment file from an unknown source, the user must assume that it may be a ransomware and not run it if there is a document file icon or if the file’s extension is in a form of an executable file.
AhnLab’s V3 products detect the ransomware under the following aliases:
[File Detection]
- Trojan/Win32.MalPe.R332354



